Rsa And Dsa Encryption Algorithms Explained Cryptography Network
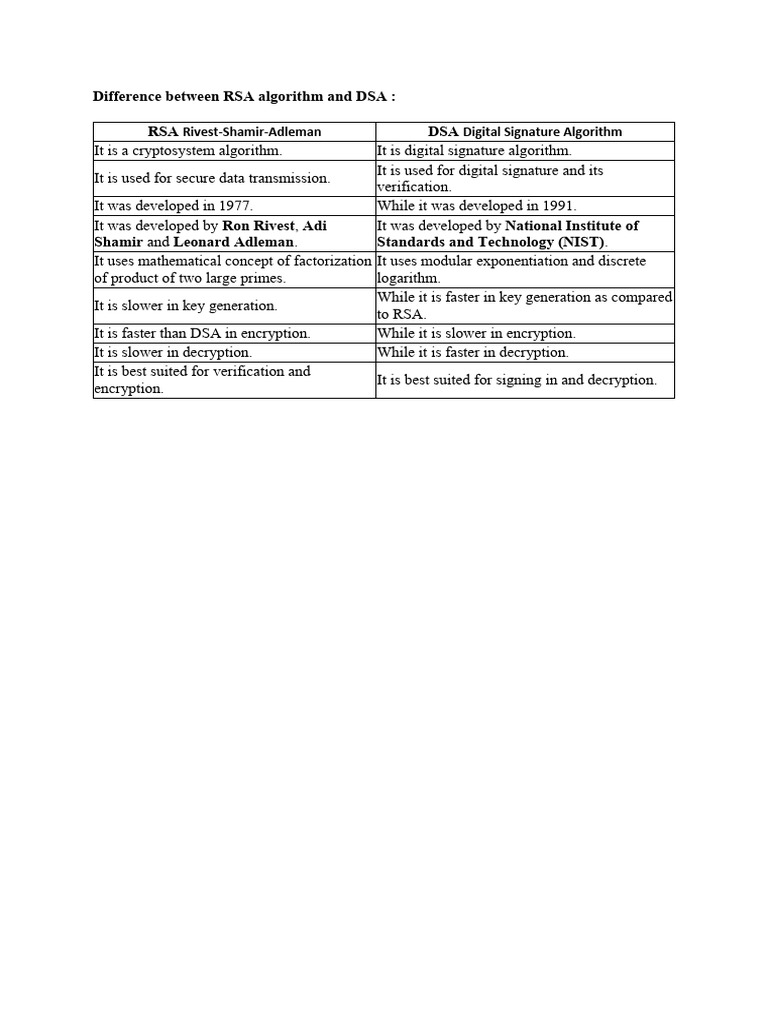
Difference Between Rsa Algorithm And Dsa Pdf Cryptography Encryption Whereas, rsa is used for secure data transmission and encryption, dsa is used for checking the authenticity of the message, generating and verifying signatures. In short, rsa is primarily used for encryption and decryption, while dsa is used to generate and validate digital signatures. both are useful cryptographic tools, with their own set of advantages and applications.
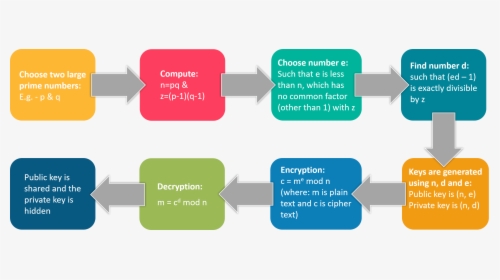
Rsa Encryption What Is Cryptography Edureka Cryptographic Algorithms Two of the most prominent asymmetric algorithms are rsa (rivest shamir adleman) and dsa (digital signature algorithm). while both rely on public private key cryptography, they differ sharply in design, mathematical foundations, and use cases. Learn the core differences between rsa vs dsa algorithms, their benefits, working mechanisms, python implementations, and top applications in data security. The world of modern cryptography is built upon the concept of asymmetric encryption, and the pillars of asymmetric encryption are these three algorithms: rsa, diffie hellman, and dsa (digital signature algorithm). In the sphere of cryptography, rsa and dsa are two pivotal algorithms distinguished by their unique approaches to encryption and digital signatures. this section offers a detailed examination of their complexities, security implications, and the mechanisms by which keys are generated and signatures are created and verified.

Rsa And Dsa Encryption Algorithms Explained Cryptography Network The world of modern cryptography is built upon the concept of asymmetric encryption, and the pillars of asymmetric encryption are these three algorithms: rsa, diffie hellman, and dsa (digital signature algorithm). In the sphere of cryptography, rsa and dsa are two pivotal algorithms distinguished by their unique approaches to encryption and digital signatures. this section offers a detailed examination of their complexities, security implications, and the mechanisms by which keys are generated and signatures are created and verified. Rsa and dsa signatures are crucial cryptographic tools for ensuring digital security. they use complex math to create unforgeable digital signatures, verifying the authenticity and integrity of messages or documents in various applications. Rsa and dsa encryption algorithms explained | cryptography & network security tutorial | simplilearn. In this tutorial, you'll learn aes, rsa, des, ecc, chacha20, post quantum cryptography explained with real production trade offs, code examples, key management lifecycle, and the mistakes that get systems pwned. Digital signature algorithms like rsa, dsa, ecc, eddsa, and gost enable the secure generation and verification of digital signatures. these algorithms provide a robust mechanism to ensure the authenticity, integrity, and non repudiation of digital messages or documents.
Comments are closed.