Rsa And Dsa Encryption Algorithms Explained Cryptography Network Security Tutorial Simplilearn
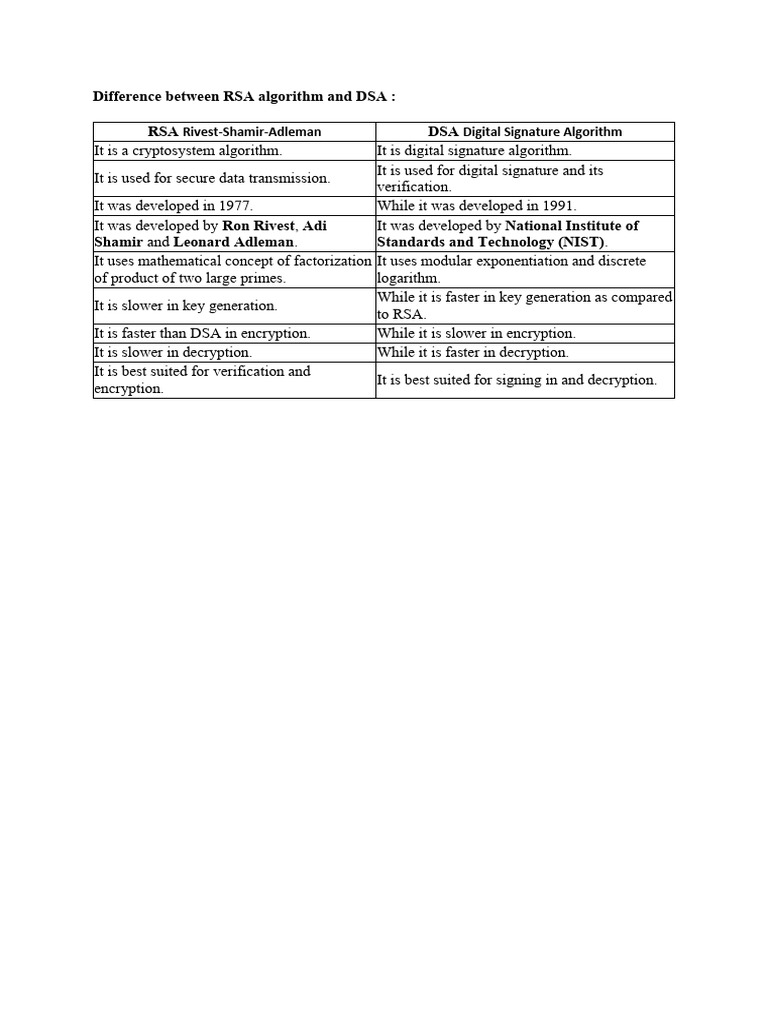
Difference Between Rsa Algorithm And Dsa Pdf Cryptography Encryption We'll learn about rsa and dsa, how they work when are they used, and their differences. what is rsa? rsa stands for rivest shamir adleman. it is a cryptosystem used for secure data transmission. in the rsa algorithm, the encryption key is public but the decryption key is private. Rsa and dsa, these two types of encryption algorithms have different abilities. we use similar applications of these two algorithms in cybersecurity. in this chapter, we will look at the tabular differences between the dsa and rsa algorithms.
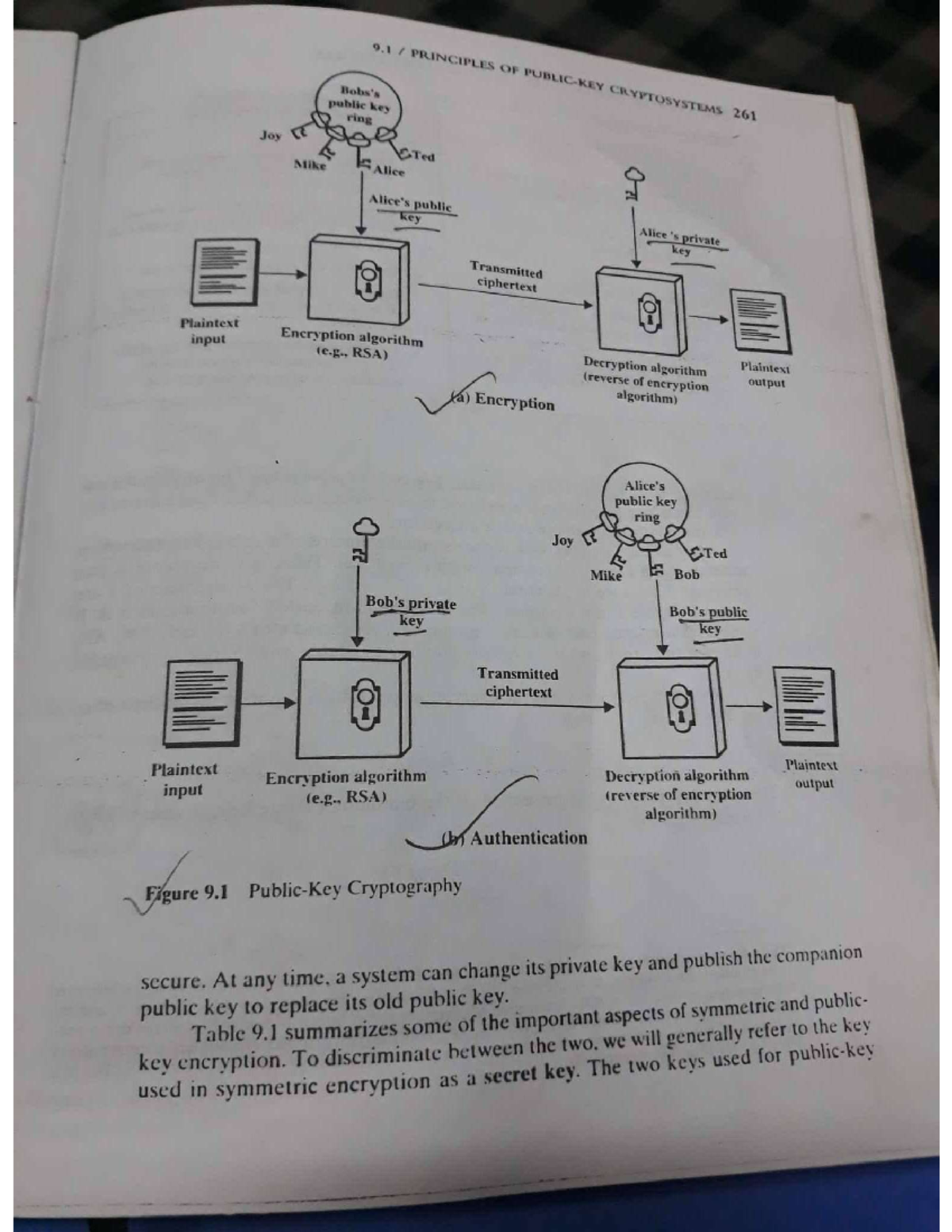
Principals Of Cryptography Rsa Network Security And Cryptography Rsa and dsa encryption algorithms explained | cryptography & network security tutorial | simplilearn. Learn about the rsa algorithm, a crucial public key encryption method. discover how it secures data, its workings, and its applications in modern cryptography. While both rely on public private key cryptography, they differ sharply in design, mathematical foundations, and use cases. this blog demystifies dsa and rsa, breaking down their inner workings, public private key mechanisms, performance tradeoffs, and suitability for client server applications. In the sphere of cryptography, rsa and dsa are two pivotal algorithms distinguished by their unique approaches to encryption and digital signatures. this section offers a detailed examination of their complexities, security implications, and the mechanisms by which keys are generated and signatures are created and verified.
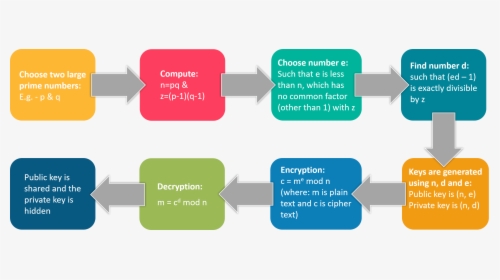
Rsa Encryption What Is Cryptography Edureka Cryptographic Algorithms While both rely on public private key cryptography, they differ sharply in design, mathematical foundations, and use cases. this blog demystifies dsa and rsa, breaking down their inner workings, public private key mechanisms, performance tradeoffs, and suitability for client server applications. In the sphere of cryptography, rsa and dsa are two pivotal algorithms distinguished by their unique approaches to encryption and digital signatures. this section offers a detailed examination of their complexities, security implications, and the mechanisms by which keys are generated and signatures are created and verified. Learn the core differences between rsa vs dsa algorithms, their benefits, working mechanisms, python implementations, and top applications in data security. Rsa and dsa signatures are crucial cryptographic tools for ensuring digital security. they use complex math to create unforgeable digital signatures, verifying the authenticity and integrity of messages or documents in various applications. In this article, we will dive into the difference between rsa algorithm and dsa algorithm in a tabular form. but let us first know a bit more about each of these in detail. This guide explains how dsa works, its parameters, signing and verification steps, security pitfalls, and how it compares with modern algorithms such as rsa, ecdsa, and eddsa.

Rsa And Dsa Encryption Algorithms Explained Cryptography Network Learn the core differences between rsa vs dsa algorithms, their benefits, working mechanisms, python implementations, and top applications in data security. Rsa and dsa signatures are crucial cryptographic tools for ensuring digital security. they use complex math to create unforgeable digital signatures, verifying the authenticity and integrity of messages or documents in various applications. In this article, we will dive into the difference between rsa algorithm and dsa algorithm in a tabular form. but let us first know a bit more about each of these in detail. This guide explains how dsa works, its parameters, signing and verification steps, security pitfalls, and how it compares with modern algorithms such as rsa, ecdsa, and eddsa.
Comments are closed.