Difference Between Rsa Algorithm And Dsa Pdf Cryptography Encryption
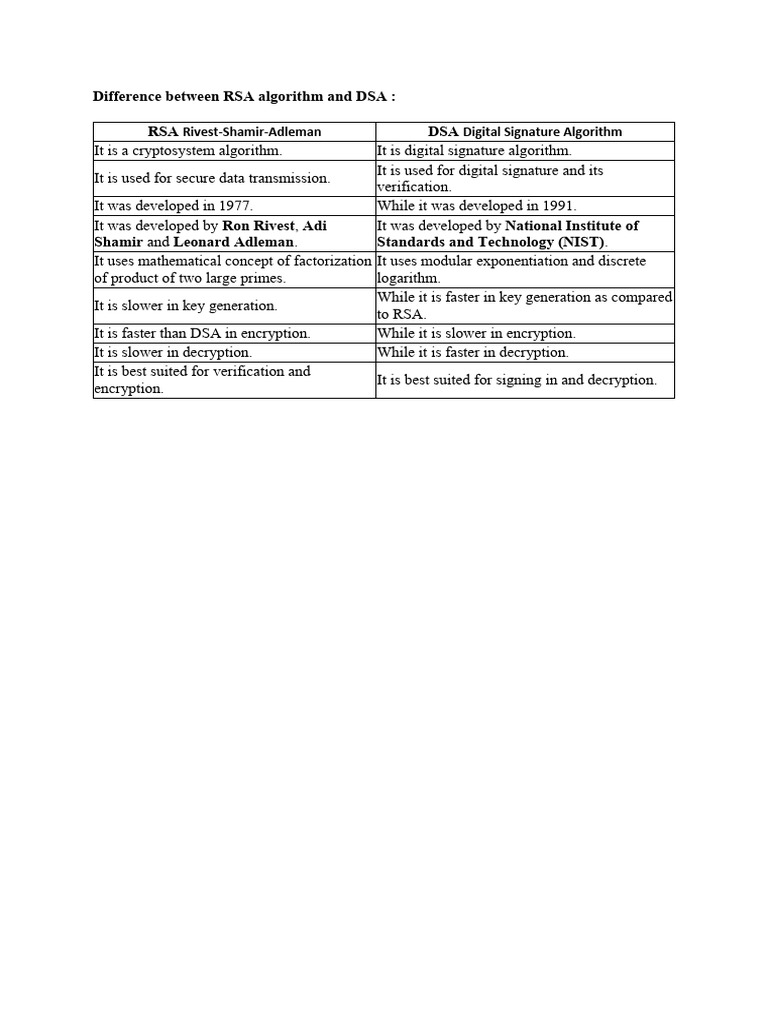
Difference Between Rsa Algorithm And Dsa Pdf Cryptography Encryption Whereas, rsa is used for secure data transmission and encryption, dsa is used for checking the authenticity of the message, generating and verifying signatures. The document outlines the differences between the rsa and dsa algorithms, highlighting rsa as a cryptosystem for secure data transmission and dsa as a digital signature algorithm.

Rsa Algorithm Pdf Key Cryptography Public Key Cryptography In short, rsa is primarily used for encryption and decryption, while dsa is used to generate and validate digital signatures. both are useful cryptographic tools, with their own set of advantages and applications. Two of the most prominent asymmetric algorithms are rsa (rivest shamir adleman) and dsa (digital signature algorithm). while both rely on public private key cryptography, they differ sharply in design, mathematical foundations, and use cases. Algorithm of rsa and dsa cryptography. download as a pdf or view online for free. Learn the core differences between rsa vs dsa algorithms, their benefits, working mechanisms, python implementations, and top applications in data security.
Understand Rsa Dsa And Ecc Encryption Algorithms In Pki Algorithm of rsa and dsa cryptography. download as a pdf or view online for free. Learn the core differences between rsa vs dsa algorithms, their benefits, working mechanisms, python implementations, and top applications in data security. In chapter 5 we explore using the rsa and dsa asymmetric algorithms as they relate to authentication and integrity checking, involving a technology known as digital signatures. for a more thorough discussion of rsa from a mathematical point of view, please see appendix b. Evices are not having enough space to store and secure all information. so, the paper is to study the comparison of two methods rsa (ronald rivest algorithm) and dsa (digital s. gnature algorithm to assure privacy and security of data cryptographic. keywords: mobile cloud co. pu. ing, securit. Learn about rsa, dsa, and ecc encryption algorithms, their differences, limitations, and performance similarities with sectigo® official. Dsa and rsa are critical algorithms used in secure file transfers, with rsa suited for both encryption and signing, while dsa was initially designed for signing but now also supports encryption.
Comments are closed.