Cryptography Rsa Algorithm
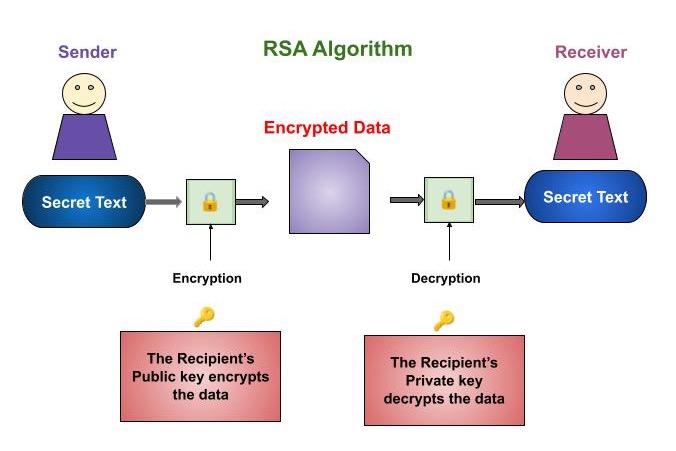
Cryptography Rsa Algorithm Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data. The rsa algorithm involves four steps: key generation, key distribution, public key operation (used for encryption or verifying a signature), and private key operation (used for decryption or signing a message).
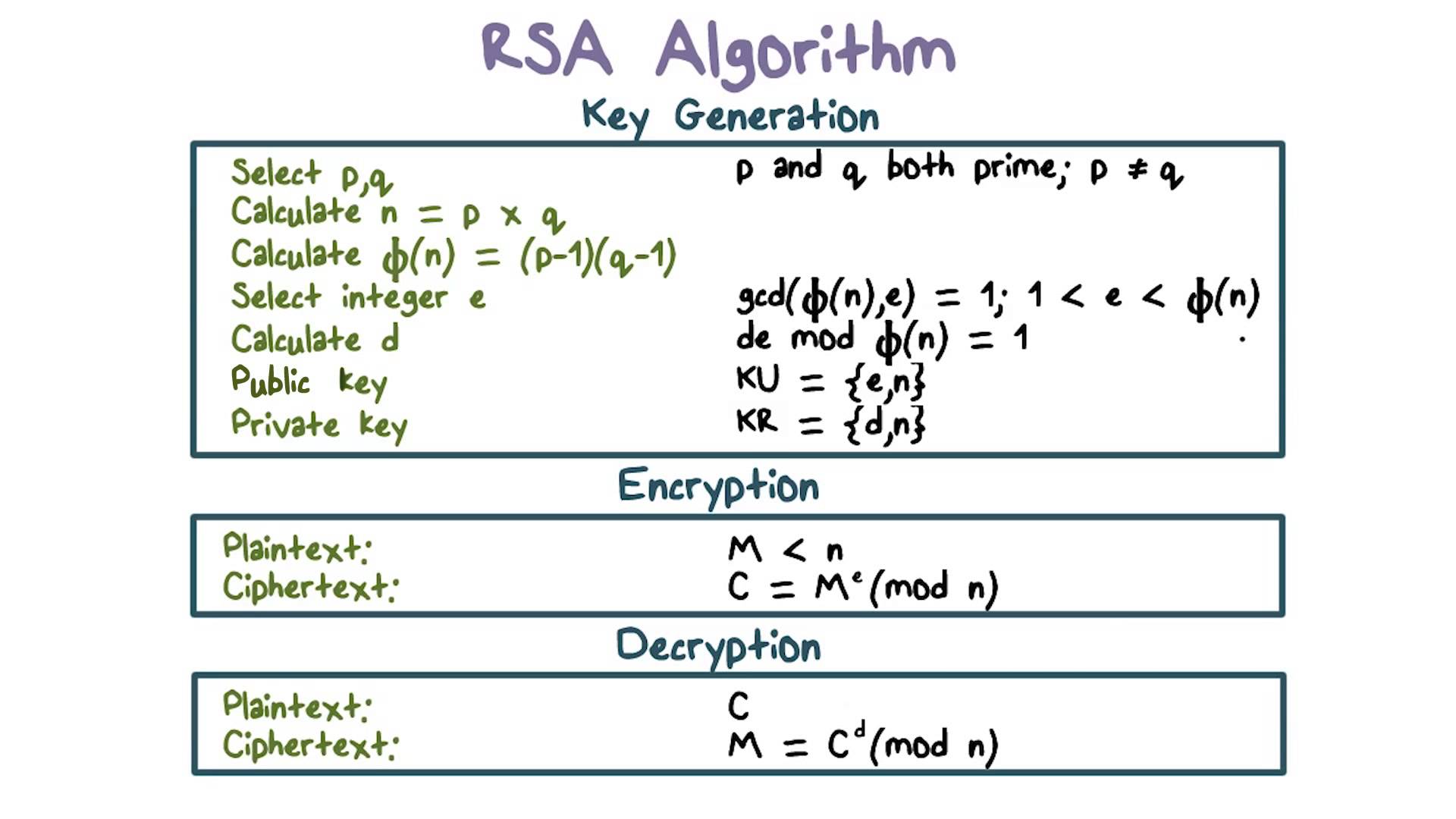
What Is Rsa Algorithm In Cryptography Ruaue Rsa, a popular encryption algorithm since 1977, employs public and private key pairs. while suitable for various tasks, rsa's complexity limits its use for encrypting large data. 12.2.1 the rsa algorithm — putting to use the basic idea the basic idea described in the previous subsection can be used to create a confidential communication channel in the manner described here. Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Hu abstract. in the field of cryptography, which aims to ensure secure message communica tion, the rsa public key cryptosystem is the oldest widely applied secure data transmi. sion method. in this expository paper, we provide a historical and technical overview of the rsa .

Rsa Algorithm Public Key Cryptography Ppt Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Hu abstract. in the field of cryptography, which aims to ensure secure message communica tion, the rsa public key cryptosystem is the oldest widely applied secure data transmi. sion method. in this expository paper, we provide a historical and technical overview of the rsa . What is the rsa algorithm? the rsa algorithm (rivest shamir adleman) is a public key cryptosystem that uses a pair of keys to secure digital communication and transactions over insecure networks, such as the internet. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Rsa is an encryption algorithm, used to securely transmit messages over the internet. it is based on the principle that it is easy to multiply large numbers, but factoring large numbers is very difficult. In rsa cryptography, both the public and the private keys can encrypt a message; the opposite key from the one used to encrypt a message is used to decrypt it.

Rsa Algorithm Public Key Cryptography Ppt What is the rsa algorithm? the rsa algorithm (rivest shamir adleman) is a public key cryptosystem that uses a pair of keys to secure digital communication and transactions over insecure networks, such as the internet. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Rsa is an encryption algorithm, used to securely transmit messages over the internet. it is based on the principle that it is easy to multiply large numbers, but factoring large numbers is very difficult. In rsa cryptography, both the public and the private keys can encrypt a message; the opposite key from the one used to encrypt a message is used to decrypt it.
Comments are closed.