Jwt Algorithm Confusion Attack Solution Securityboat

Jwt Algorithm Confusion Attack Solution Securityboat In a jwt algorithm confusion attack, the attacker exploits the difference between symmetric (hs256) and asymmetric (rs256) cryptography used in jwts. by changing the algorithm from rs256 to hs256, the attacker transitions from the use of a public private key pair to a shared secret key. The lightrag api is vulnerable to a jwt algorithm confusion attack where an attacker can forge tokens by specifying 'alg': 'none' in the jwt header. ….

Jwt Algorithm Confusion Attack Solution Securityboat Algorithm confusion attacks (also known as key confusion attacks) occur when an attacker is able to force the server to verify the signature of a json web token (jwt) using a different algorithm than is intended by the website's developers. Jwt algorithm confusion attacks are back — and q1 2026 has seen a cluster of critical cves across major frameworks and libraries. the root cause is always the same: trusting the attacker controlled alg field in the jwt header to select the signature verification algorithm. In this portswigger expert level lab, we exploit algorithm confusion by crafting a jwt that tricks the server into verifying an rs256 token as hs256, using the server's own public key as the hmac secret. Algorithm confusion attacks (also known as key confusion attacks or rs256 → hs256 confusion) are one of the most devastating classes of jwt vulnerabilities still encountered in real world.
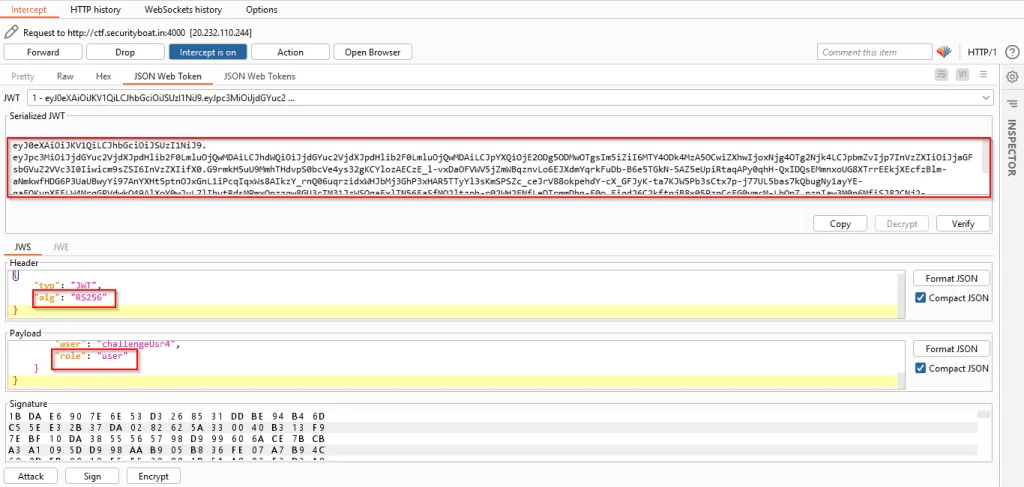
Jwt Algorithm Confusion Attack Solution Securityboat In this portswigger expert level lab, we exploit algorithm confusion by crafting a jwt that tricks the server into verifying an rs256 token as hs256, using the server's own public key as the hmac secret. Algorithm confusion attacks (also known as key confusion attacks or rs256 → hs256 confusion) are one of the most devastating classes of jwt vulnerabilities still encountered in real world. A complete breakdown of one of the most dangerous jwt vulnerabilities, from the cryptographic mechanics to the defensive code patterns that stop it. In this scenario, the attacker is able to validate a jwt signed with a different algorithm rather than the intended or implemented algorithm in the backend. this allows an attacker to forge a valid jwt without signing it with the server’s side secret key. An attacker can forge valid jwts by changing the signing algorithm from rs256 to hs256 and using the public key as the hmac secret. this allows full authentication bypass and unauthorized access to protected resources. One of the most critical yet frequently misunderstood vulnerabilities is the jwt key confusion attack, also known as the algorithm confusion attack. in this guide, we will break down exactly how this attack works, why it happens, and how you can identify and mitigate it in your infrastructure.
Comments are closed.