Jwt Authentication Bypass Via Algorithm Confusion
Algorithm Confusion Attacks Web Security Academy This lab uses a jwt based mechanism for handling sessions. it uses a robust rsa key pair to sign and verify tokens. however, due to implementation flaws,. In this portswigger expert level lab, we exploit algorithm confusion by crafting a jwt that tricks the server into verifying an rs256 token as hs256, using the server's own public key as the hmac secret.
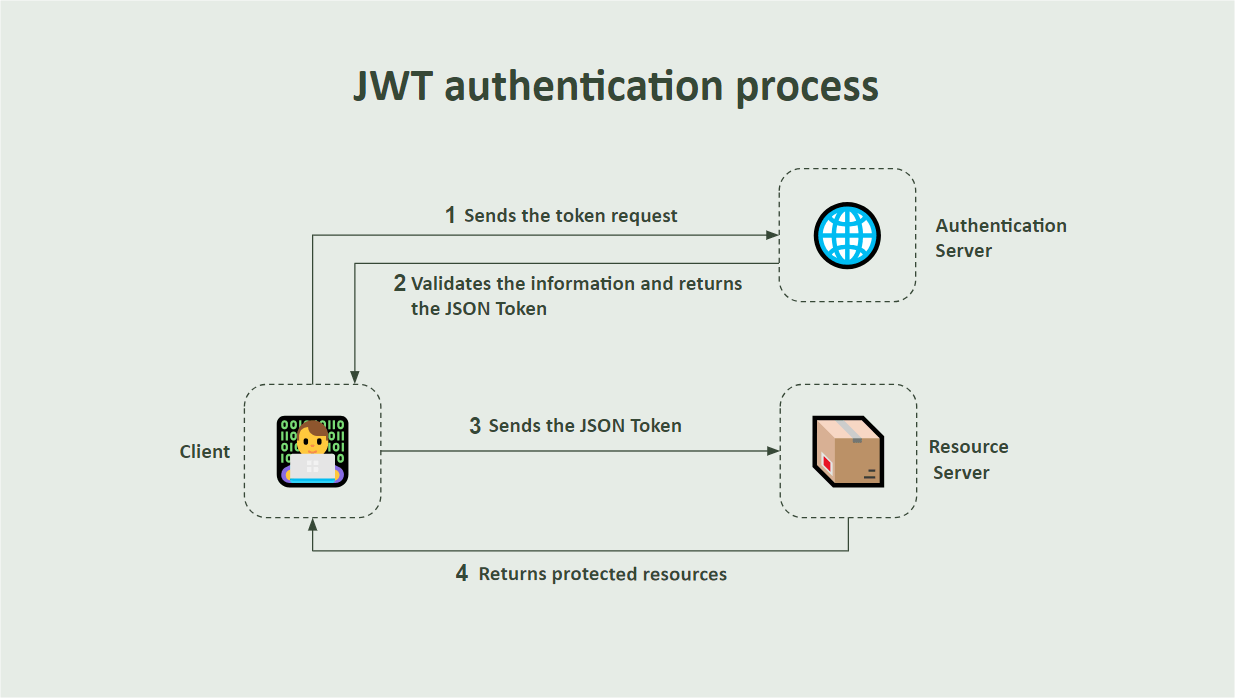
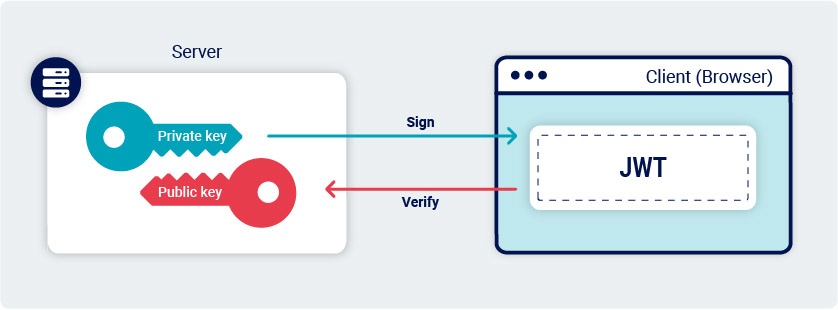
New In Net 8 Asp Net Core Identity And How To Implement It Today i’m going to show how jwt authentication can be bypassed using the algorithm confusion vulnerability, and how we can exploit it to gain admin access. we’ll be solving this. In a terminal, run the following command, passing in the two jwts as arguments. Lab: jwt authentication bypass via algorithm confusion this lab uses a jwt based mechanism for handling sessions. it uses a robust rsa key pair to sign and verify tokens. Vulnerability: jwt signature bypass (algorithm confusion). description: the application expects a jwt signed with an asymmetric algorithm (rs256) and verifies it using a known public key.
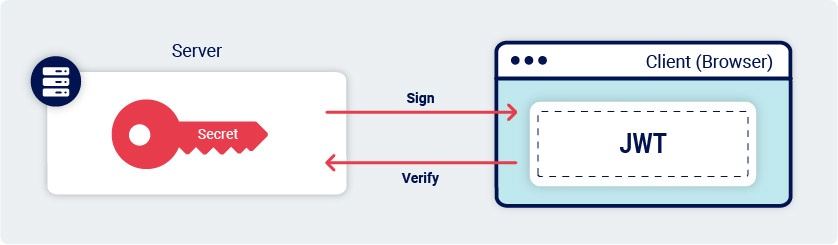
Algorithm Confusion Attacks Web Security Academy Lab: jwt authentication bypass via algorithm confusion this lab uses a jwt based mechanism for handling sessions. it uses a robust rsa key pair to sign and verify tokens. Vulnerability: jwt signature bypass (algorithm confusion). description: the application expects a jwt signed with an asymmetric algorithm (rs256) and verifies it using a known public key. An attacker can forge valid jwts by changing the signing algorithm from rs256 to hs256 and using the public key as the hmac secret. this allows full authentication bypass and unauthorized access to protected resources. Cracking jwts: a bug bounty hunting guide [part 6] jwt authentication bypass via algorithm confusion “sometimes, it’s not the algorithm’s fault — it’s the developer who blindly trusts the …. Jwt authentication bypass via algorithm confusion | portswigger academy tutorial pink boo 1.86k subscribers subscribed. Explore how jwt algorithm confusion enables attackers to forge tokens, bypass authentication, and escalate privileges. this article explains the vulnerability step by step and highlights the security pitfalls behind rs256 to hs256 misuse.

Lab Jwt Authentication Bypass Via Algorithm Confusion With No Exposed An attacker can forge valid jwts by changing the signing algorithm from rs256 to hs256 and using the public key as the hmac secret. this allows full authentication bypass and unauthorized access to protected resources. Cracking jwts: a bug bounty hunting guide [part 6] jwt authentication bypass via algorithm confusion “sometimes, it’s not the algorithm’s fault — it’s the developer who blindly trusts the …. Jwt authentication bypass via algorithm confusion | portswigger academy tutorial pink boo 1.86k subscribers subscribed. Explore how jwt algorithm confusion enables attackers to forge tokens, bypass authentication, and escalate privileges. this article explains the vulnerability step by step and highlights the security pitfalls behind rs256 to hs256 misuse.

Lab Jwt Authentication Bypass Via Algorithm Confusion Web Security Jwt authentication bypass via algorithm confusion | portswigger academy tutorial pink boo 1.86k subscribers subscribed. Explore how jwt algorithm confusion enables attackers to forge tokens, bypass authentication, and escalate privileges. this article explains the vulnerability step by step and highlights the security pitfalls behind rs256 to hs256 misuse.
Comments are closed.