Jwt Attacks Web Security Academy
Jwt Attacks Jwt attacks in this section, we'll look at how design issues and flawed handling of json web tokens (jwts) can leave websites vulnerable to a variety of high severity attacks. Learn how to find, exploit and defend against jwt attacks. for ethical hackers, developers and bug bounty hunters. in this course, we dive into the technical details behind jwt attacks. we explore methods for finding these vulnerabilities along with various techniques for exploiting them.

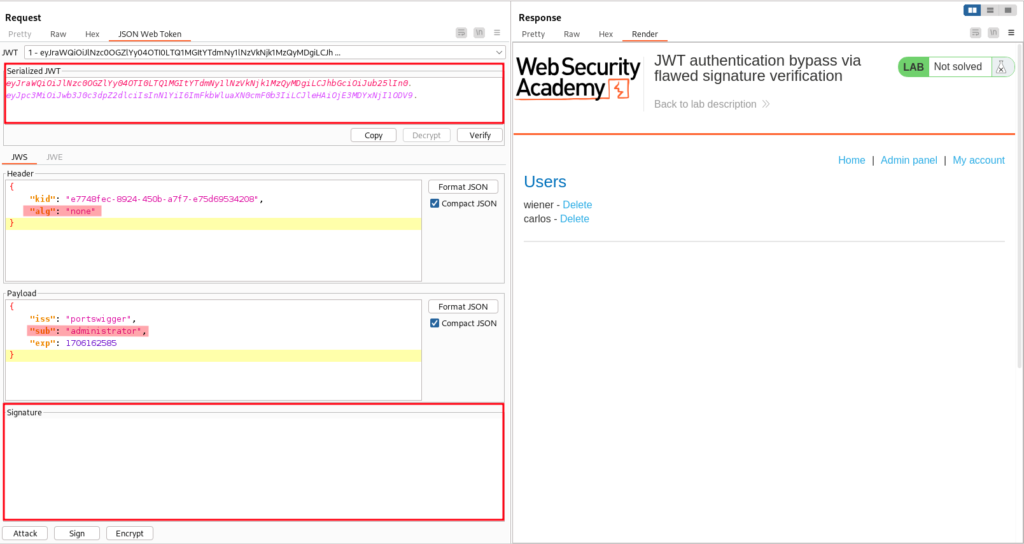
Jessica Haworth Elsayed On Linkedin Jwt Attacks Web Security Academy Walkthroughs for the jwt attack labs found on portswigger's web security academy portswigger web security jwt. This write up for the lab jwt authentication bypass via jwk header injection is part of my walk through series for portswigger's web security academy. learning path: advanced topics → jwt attacks. Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. Having established a foundational understanding of jwts, the next instalment of this series will delve into jwt attacks through practical exercises from portswigger web academy.

Json Web Token Attacks And Vulnerabilities Invicti Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. Having established a foundational understanding of jwts, the next instalment of this series will delve into jwt attacks through practical exercises from portswigger web academy. Portswigger recommends installing the jwt editor extension, which is available from the bapp store (pro version). bchecks available on github. unfortunately, the inspector cannot currently decode both the header and payload of the jwt at the same time. you need to select either one or the other. Master jwt authentication with our comprehensive guide. learn implementation best practices, security measures, and advanced protection strategies for your web applications. In this video, our researchers provide an in depth analysis of a reflected cross site scripting (xss) vulnerability stemming from weaknesses in the jwt token validation mechanism. we demonstrate how a custom built vulnerable web application can be exploited by abusing jwt tokens, allowing attacker controlled input to bypass security checks and execute malicious scripts. 🔐 covered topics. Security considerations use https prevent man in the middle attacks by transmitting jwts over https . set expiration time prevent long lived tokens that can be exploited. and use secure storage to store jwt securely for example http only cookies instead of local storage common issues with jwt jwt rejects the token if the token has expired, the.

Jwt Attacks Web Security Academy Portswigger recommends installing the jwt editor extension, which is available from the bapp store (pro version). bchecks available on github. unfortunately, the inspector cannot currently decode both the header and payload of the jwt at the same time. you need to select either one or the other. Master jwt authentication with our comprehensive guide. learn implementation best practices, security measures, and advanced protection strategies for your web applications. In this video, our researchers provide an in depth analysis of a reflected cross site scripting (xss) vulnerability stemming from weaknesses in the jwt token validation mechanism. we demonstrate how a custom built vulnerable web application can be exploited by abusing jwt tokens, allowing attacker controlled input to bypass security checks and execute malicious scripts. 🔐 covered topics. Security considerations use https prevent man in the middle attacks by transmitting jwts over https . set expiration time prevent long lived tokens that can be exploited. and use secure storage to store jwt securely for example http only cookies instead of local storage common issues with jwt jwt rejects the token if the token has expired, the.

Jwt Attacks Web Security Academy In this video, our researchers provide an in depth analysis of a reflected cross site scripting (xss) vulnerability stemming from weaknesses in the jwt token validation mechanism. we demonstrate how a custom built vulnerable web application can be exploited by abusing jwt tokens, allowing attacker controlled input to bypass security checks and execute malicious scripts. 🔐 covered topics. Security considerations use https prevent man in the middle attacks by transmitting jwts over https . set expiration time prevent long lived tokens that can be exploited. and use secure storage to store jwt securely for example http only cookies instead of local storage common issues with jwt jwt rejects the token if the token has expired, the.
Comments are closed.