Jwt Attack Tutorial And Guidelines Jwt Json Web Token Attacks
Json Web Token Jwt Attack Most Common Scenarios In this section, we'll look at how design issues and flawed handling of json web tokens (jwts) can leave websites vulnerable to a variety of high severity attacks. Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab.

Json Web Token Jwt Attack Most Common Scenarios Learn how to identify and exploit json web token (jwt) vulnerabilities using several different testing methods. read the article now!. Explore common jwt attacks and vulnerabilities, including token tampering, signature bypass, and expiration exploits. learn how to secure your applications. Json web tokens (jwts) are a standard format for sending cryptographically signed json data between systems. they’re commonly used in authentication, session management, and access control. It has been observed that some web applications rely on a trusted jwt service for the generation and management of their tokens. instances have been recorded where a token, generated for one client by the jwt service, was accepted by another client of the same jwt service.
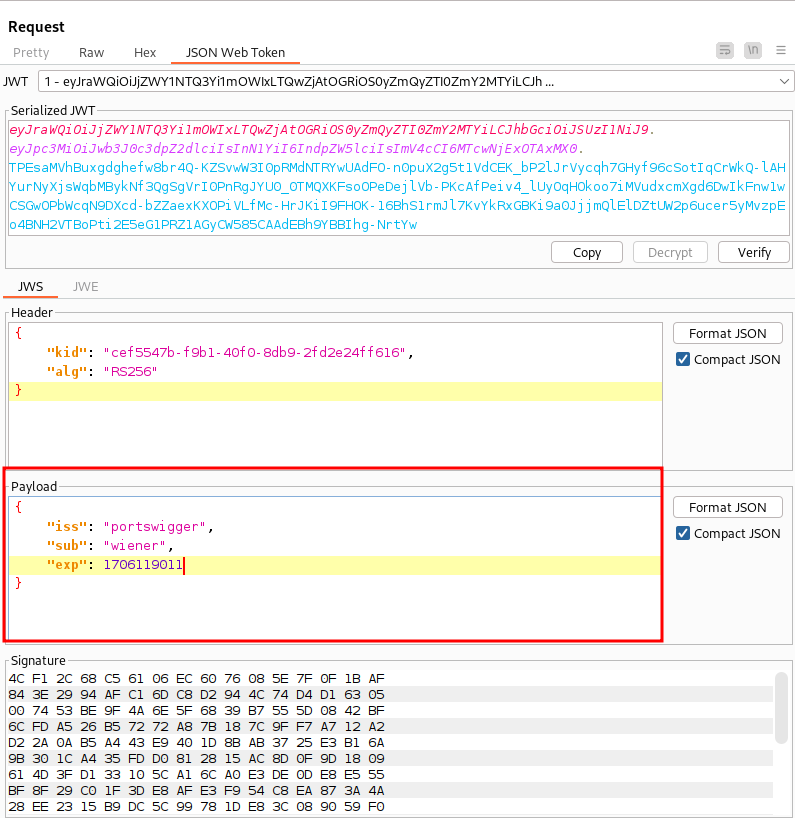
Jwt Attacks Json web tokens (jwts) are a standard format for sending cryptographically signed json data between systems. they’re commonly used in authentication, session management, and access control. It has been observed that some web applications rely on a trusted jwt service for the generation and management of their tokens. instances have been recorded where a token, generated for one client by the jwt service, was accepted by another client of the same jwt service. This page covers authentication and authorization bypass vulnerabilities, with a primary focus on json web token (jwt) attacks along with related security issues in source code management, directory services, document processing, and remote method invocation systems. This article explains how jwt (json web token) works. it also details the vulnerabilities, attacks and best practices to secure the implementation of jwt. Json web tokens (jwts) provide a way to securely exchange data using json objects. they are often used in authorization because they can be signed, verified, and therefore trusted – but only if implemented correctly. here is a technical deep dive into json web token attacks and vulnerabilities. Json web tokens (jwts) are cryptographically signed json tokens, intended to share claims between systems. they are frequently used as authentication or session tokens, particularly on rest apis.
Comments are closed.