Face Morphing Attack Detection

Github Kashiani Face Morphing Attack Detection Benchmark Face Morphing attacks are detected by analyzing facial images using deep features extracted by the tvgg16 am model, enabling the identification of manipulated or composite biometric images. Morphing is a challenge to face recognition (fr) for which several morphing attack detection solutions have been proposed. we argue that face recognition and differential morphing attack detection (d mad) in principle perform very similar tasks, which we support by comparing an fr system with two existing d mad approaches. we also show that currently used decision thresholds inherently lead to.
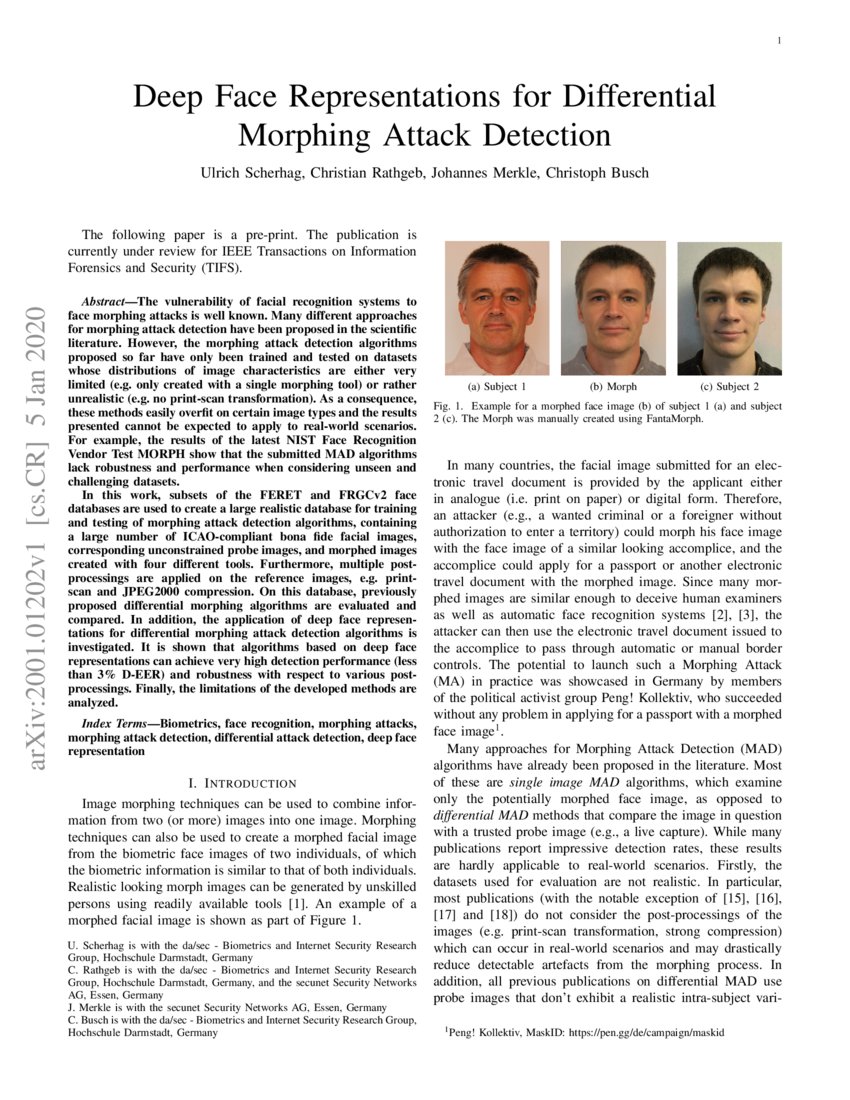
Deep Face Representations For Differential Morphing Attack Detection This paper proposes a robust face morphing attack detection (fmad) method (pipeline) leveraging deep learning de morphing networks. A novel face morphing detection method based on high frequency features was proposed. high frequency features typically represent parts of the image with high variation rates, including details and texture information. Differential morphing attack detection (d mad) offers an effective countermeasure, particularly when employing face demorphing to disentangle identities blended in the morph. however, existing methods lack operational generalizability due to limited training data and the assumption that all document inputs are morphs. In today's era, biometric authentication systems are widely used in many applications. face morph attacks are becoming a serious threat to these systems, particularly those that rely on face recognition. here, in this type of attacks, two or more face image characteristics are blended together to form a morph image. biometric systems fail to recognize such images while examining unauthorized.

Pdf Madation Face Morphing Attack Detection With Foundation Models Facial recognition systems have been found vulnerable to morphing attacks (mas). in these attacks, the facial images of two (or more) individuals are combined (morphed) and the resulting morphed facial image is then presented during registration as a biometric reference. A detector might use such characteristics to detect morphed faces, but a professional attacker can manually enhance such details to stay undetected. we developed a method based on neural style transfer that counters this image quality degeneration caused by blending. In this paper, a new face morphing attack detection approach has been proposed using two different datasets (stylegan and amsl) for testing and validation. Abstract: the possibility of various illegal acts increases when face recognition and authentication systems fail. current face recognition systems can be easily compromised by various biometric techniques. this study focuses on attack detection using morphing.

Pdf Focused Lrp Explainable Ai For Face Morphing Attack Detection In this paper, a new face morphing attack detection approach has been proposed using two different datasets (stylegan and amsl) for testing and validation. Abstract: the possibility of various illegal acts increases when face recognition and authentication systems fail. current face recognition systems can be easily compromised by various biometric techniques. this study focuses on attack detection using morphing.
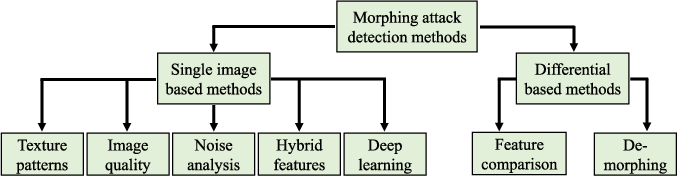
Figure 1 From Face Morphing Attack Detection And Localization Based On
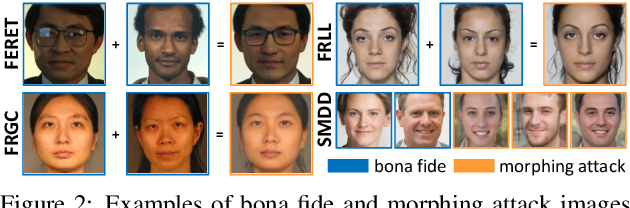
Face Morphing Attack Detection Using Privacy Aware Training Data

Unsupervised Face Morphing Attack Detection Via Self Paced Anomaly
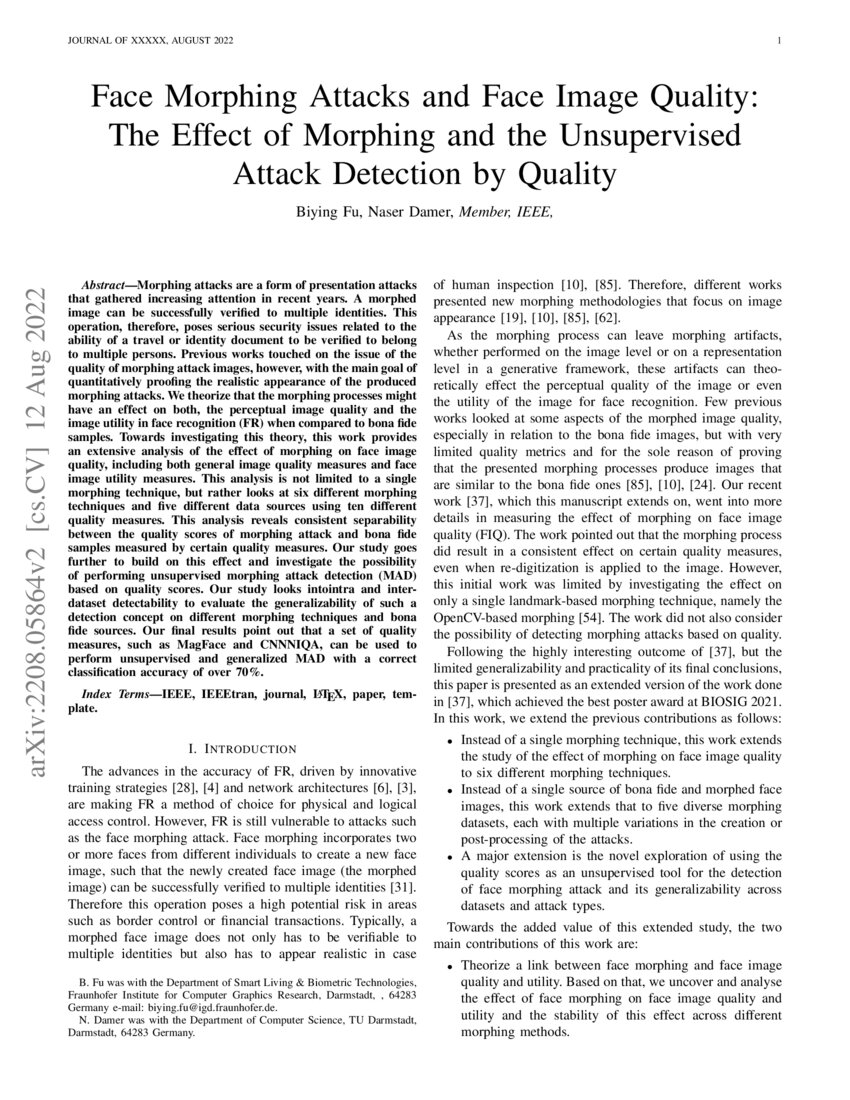
Face Morphing Attacks And Face Image Quality The Effect Of Morphing

Robust Face Morphing Attack Detection Using Fusion Of Multiple Features
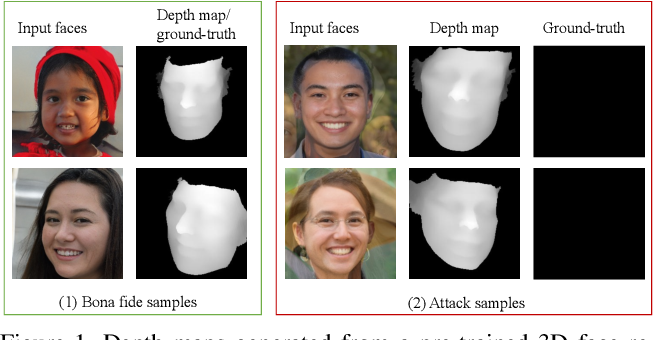
Figure 1 From Depth Guided Robust Face Morphing Attack Detection

Pdf Face Morphing Attack Generation Detection A Comprehensive Survey
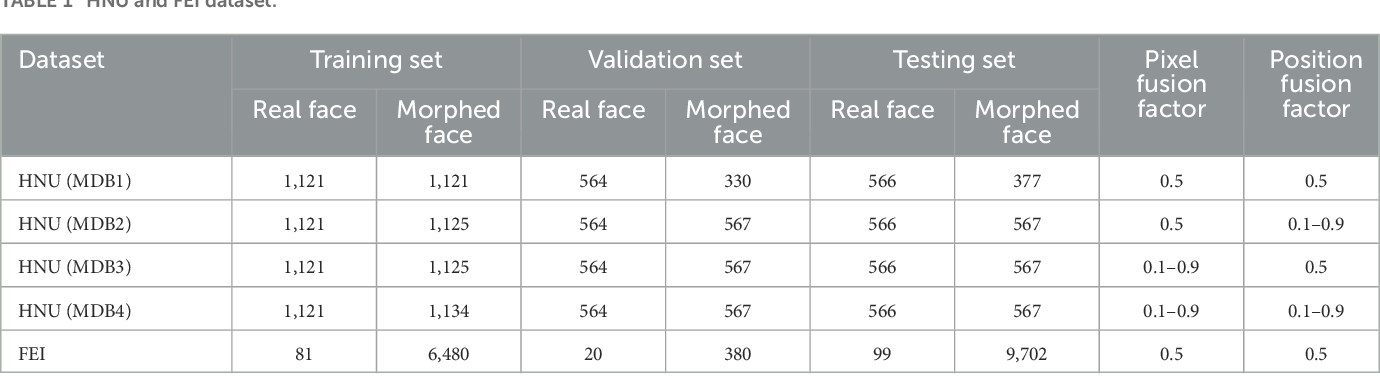
Table 1 From Face Morphing Attack Detection Based On High Frequency
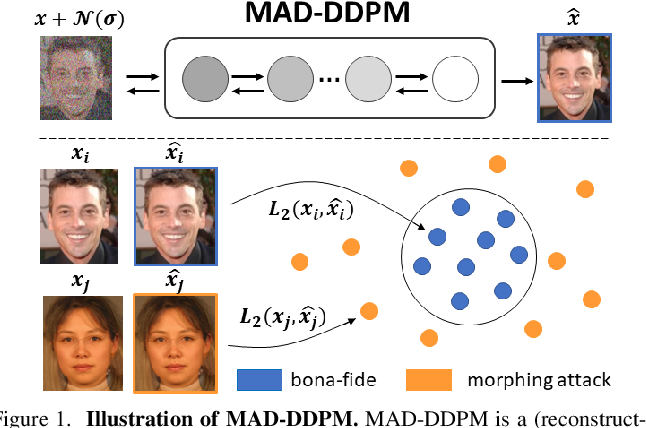
Face Morphing Attack Detection With Denoising Diffusion Probabilistic
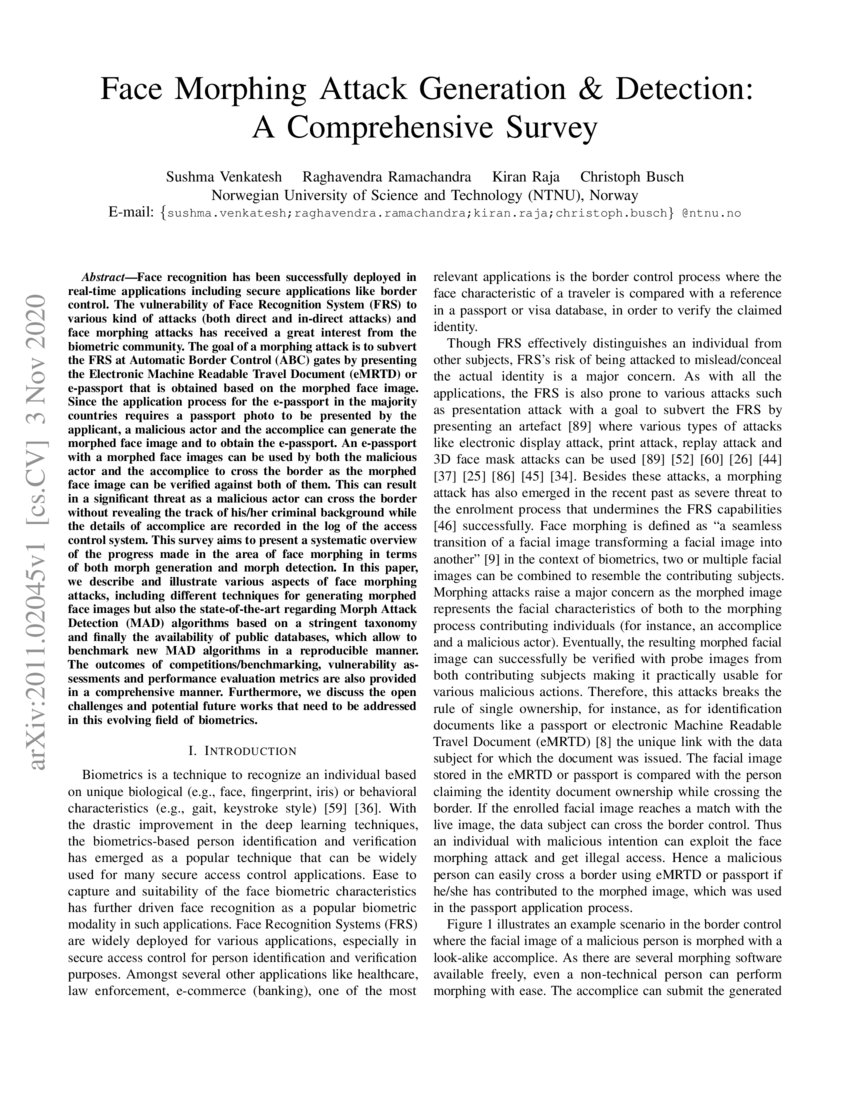
Face Morphing Attack Generation Detection A Comprehensive Survey Deepai

Multispectral Imaging For Differential Face Morphing Attack Detection

Pdf Fusion Of Face Demorphing And Deep Face Representations For
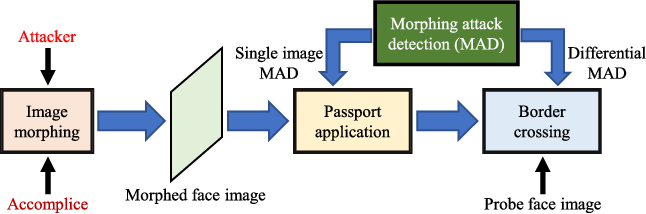
Figure 1 From Face Morphing Attack Detection And Localization Based On
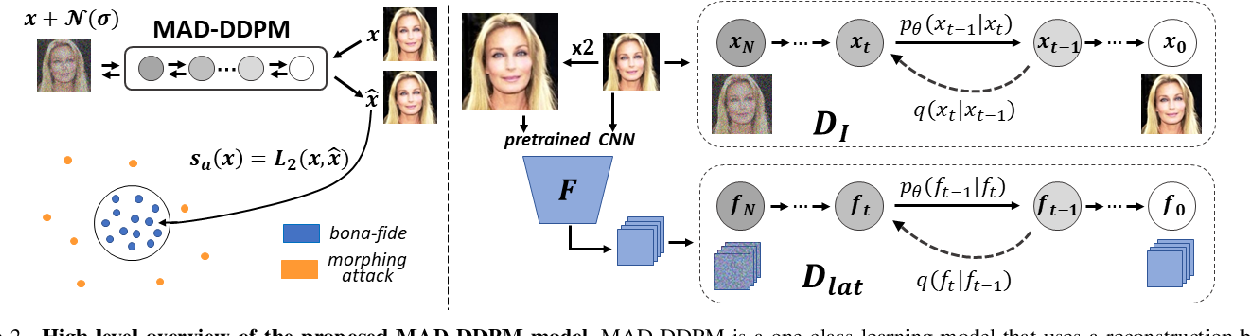
Face Morphing Attack Detection With Denoising Diffusion Probabilistic

Github Naserdamer Smdd Synthetic Face Morphing Attack Detection

Focused Lrp Explainable Ai For Face Morphing Attack Detection Deepai

Pdf Face Feature Visualisation Of Single Morphing Attack Detection

Pdf Differential Newborn Face Morphing Attack Detection Using Wavelet

Pdf Single Image Face Morphing Attack Detection Using Ensemble Of

Morphing Attack Detection By Secunet Project Secunet Ag

Pdf Face Morphing Attack Detection Using Privacy Aware Training Data

Robust Face Morphing Attack Detection Using Fusion Of Multiple Features

Figure 1 From Depth Guided Robust Face Morphing Attack Detection

Pdf Face Morphing Attack Generation Detection A Comprehensive Survey
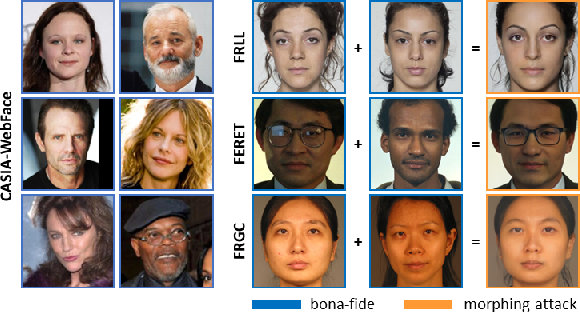
Figure 1 From Face Morphing Attack Detection With Denoising Diffusion
Github Szimhead Face Morphing Detection Differential Face Morphing

Face Feature Visualisation Of Single Morphing Attack Detection Deepai

Pdf Reflection Analysis For Face Morphing Attack Detection

Robust Face Morphing Attack Detection Using Fusion Of Multiple Features

Pdf Face Morphing Attack Detection With Denoising Diffusion

Figure 6 From Depth Guided Robust Face Morphing Attack Detection
Comments are closed.