Detection Of Face Morphing Attacks

Detection Of Face Morphing Attacks By Deep Learning The Institute For A major task in face recognition systems is the detection of morphing attacks. different deep learning techniques are used to recognize face attacks and face morphing. This research focuses on morphing attack detection. this research proposes a robust detection mechanism that can deal with variation in age, illumination, eye and head gears.

Generation And Detection Of Face Morphing Attacks Morphing is a challenge to face recognition (fr) for which several morphing attack detection solutions have been proposed. we argue that face recognition and differential morphing attack detection (d mad) in principle perform very similar tasks, which we support by comparing an fr system with two existing d mad approaches. we also show that currently used decision thresholds inherently lead to. Abstract face morphing attacks are a growing concern in the digital world, with the potential to compromise personal privacy and security. in this project, we investigate the application of deep learning methods for both generating and detecting face morphing attacks. In order to decide whether a face image is authentic or crated by a morphing algorithm, we trained deep convolutional neural networks on morphed and original face images. This paper proposes a robust face morphing attack detection (fmad) method (pipeline) leveraging deep learning de morphing networks.
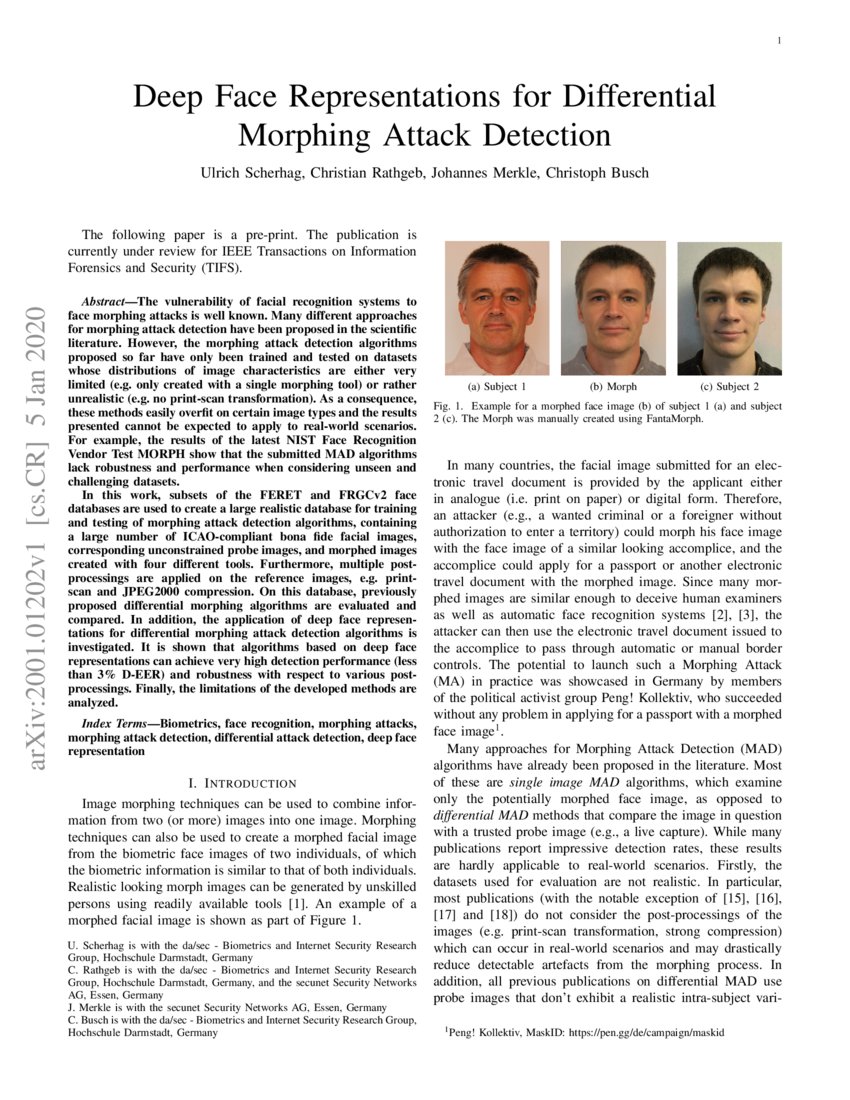
Deep Face Representations For Differential Morphing Attack Detection In order to decide whether a face image is authentic or crated by a morphing algorithm, we trained deep convolutional neural networks on morphed and original face images. This paper proposes a robust face morphing attack detection (fmad) method (pipeline) leveraging deep learning de morphing networks. To address this problem, a novel face morphing attack detection method based on high frequency features and progressive enhancement learning was proposed to effectively extract details and overcome the limitations of existing methods. In today's era, biometric authentication systems are widely used in many applications. face morph attacks are becoming a serious threat to these systems, particularly those that rely on face recognition. here, in this type of attacks, two or more face image characteristics are blended together to form a morph image. biometric systems fail to recognize such images while examining unauthorized. Different concepts of morphing attack detection are introduced and state of the art detection methods are evaluated in a comprehensive cross database experiments considering various realistic image post processings. In this project, we aim to explore both the creation and detection of face morphing attacks.
Comments are closed.