Github Kashiani Face Morphing Attack Detection Benchmark Face

Github Kashiani Face Morphing Attack Detection Benchmark Face This repository is dedicated to the development and benchmarking of various deep learning models for detecting face morphing attacks. models include resnet, efficientnet, vision transformer, and their ensemble versions. At wvu, in collaboration with citer and nist, i explored advanced security measures for automated face recognition systems, focusing on robust detection and generation of face morphing attacks.
Github Kashiani Face Morphing Attack Detection Benchmark Face Face morphing attack detection benchmark (ijcb 2022: robust ensemble morph detection with domain generalization). Face morphing attack detection benchmark. contribute to kashiani face morphing attack detection benchmark development by creating an account on github. Face morphing attack detection benchmark (ijcb 2022: robust ensemble morph detection with domain generalization) network graph · kashiani face morphing attack detection benchmark. Github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects.
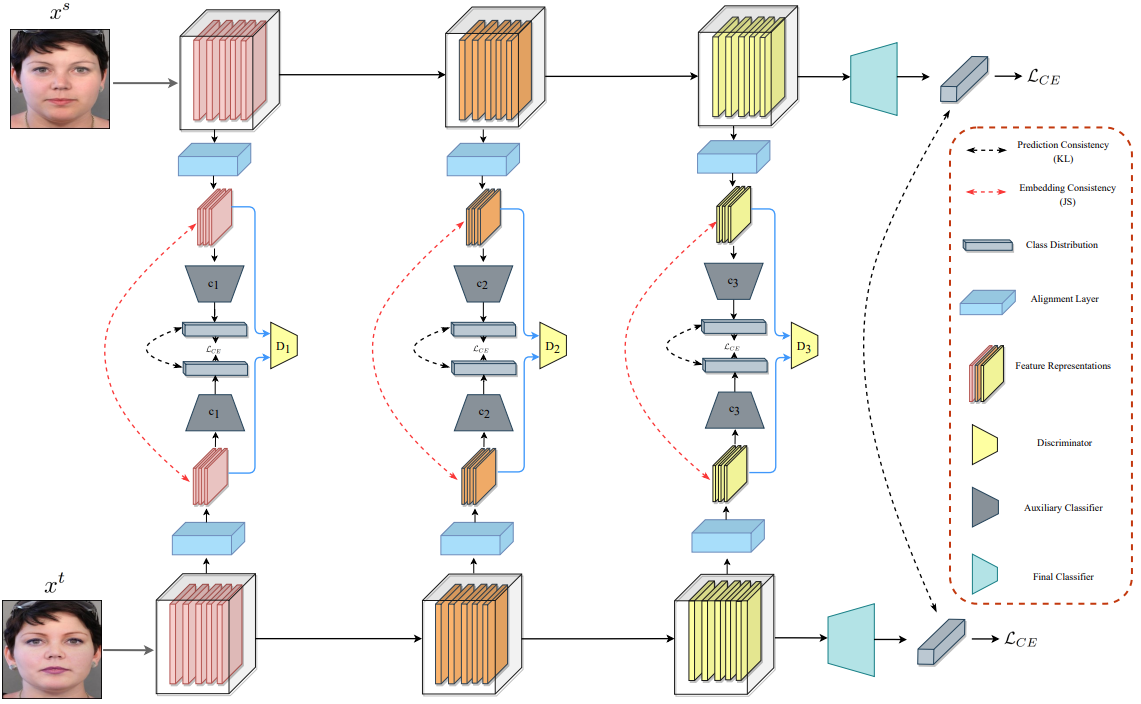
Hossein Kashiani Face morphing attack detection benchmark (ijcb 2022: robust ensemble morph detection with domain generalization) network graph · kashiani face morphing attack detection benchmark. Github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects. Face morphing attack detection benchmark (ijcb 2022: robust ensemble morph detection with domain generalization) compare · kashiani face morphing attack detection benchmark. It is carried out by comparing a suspect image with the biometric references contained in a watchlist, and its detection process is accomplished by analyzing the results of face comparison. once a morphed image is detected, its morphing attacker is also identified. In this work, we recognize the potential of fms to perform well in the mad task when properly adapted to its specificities. to this end, we adapt fm clip architectures with lora weights while simultaneously training a classification header. The proposed framework achieves high accuracy in detecting face morphing attacks, even in cases where the morphed images are visually similar to the genuine ones.
Comments are closed.