Face Morphing Attack Detection And Localization Based On Feature Wise Supervision
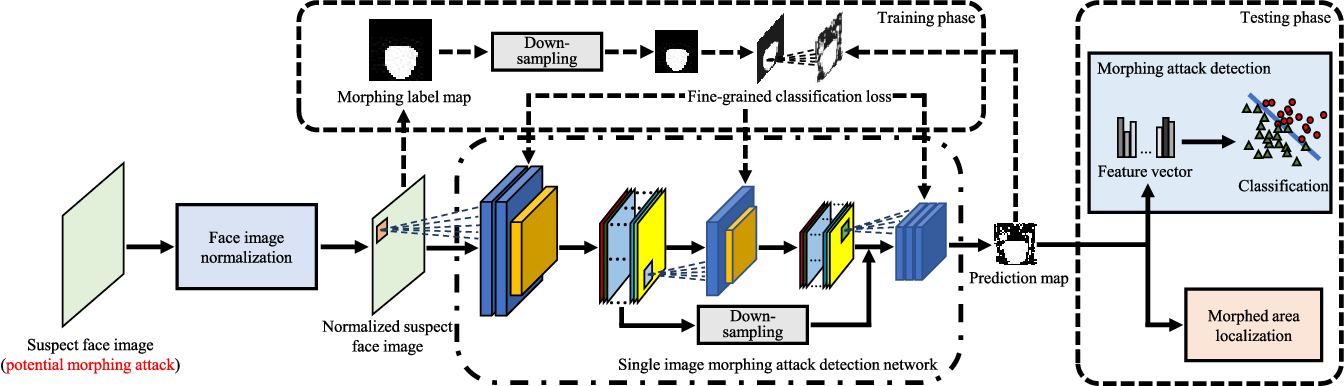
Figure 3 From Face Morphing Attack Detection And Localization Based On Abstract: to strengthen the security of face recognition systems to morphing attacks (mas), many countermeasures were proposed. A face morphing attack image can be verified to multiple identities, making this attack a major vulnerability to processes based on identity verification, such as border checks.
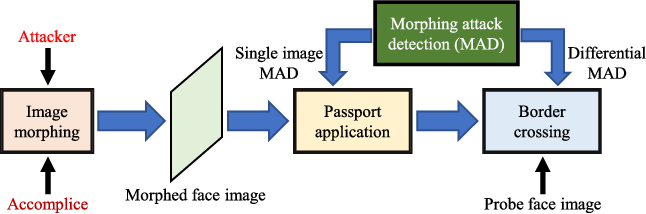
Figure 1 From Face Morphing Attack Detection And Localization Based On To this end, this paper presents a method for detecting and locating face mas by the use of feature wise supervision. This work addresses the generalization problem of face morphing attack detection by adapting a pixel wise supervision approach where a network is trained to classify each pixel of the image into an attack or not during the training process, rather than only having one label for the whole image. Article "face morphing attack detection and localization based on feature wise supervision" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). To strengthen the security of face recognition systems to morphing attacks (mas), many countermeasures were proposed.
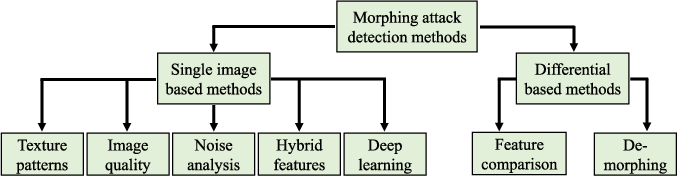
Figure 1 From Face Morphing Attack Detection And Localization Based On Article "face morphing attack detection and localization based on feature wise supervision" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). To strengthen the security of face recognition systems to morphing attacks (mas), many countermeasures were proposed. To foster the research of face morphing attack detection, the database will be released to researchers for academic research purpose upon request. the database is developed based on the face images from the public nd iiitd database and the self collected face images. Bibliographic details on face morphing attack detection and localization based on feature wise supervision. It is carried out by comparing a suspect image with the biometric references contained in a watchlist, and its detection process is accomplished by analyzing the results of face comparison. once a morphed image is detected, its morphing attacker is also identified. In this work, we address this generalization problem by adapting a pixel wise supervision approach where we train a network to classify each pixel of the image into an attack or not, rather than only having one label for the whole image.
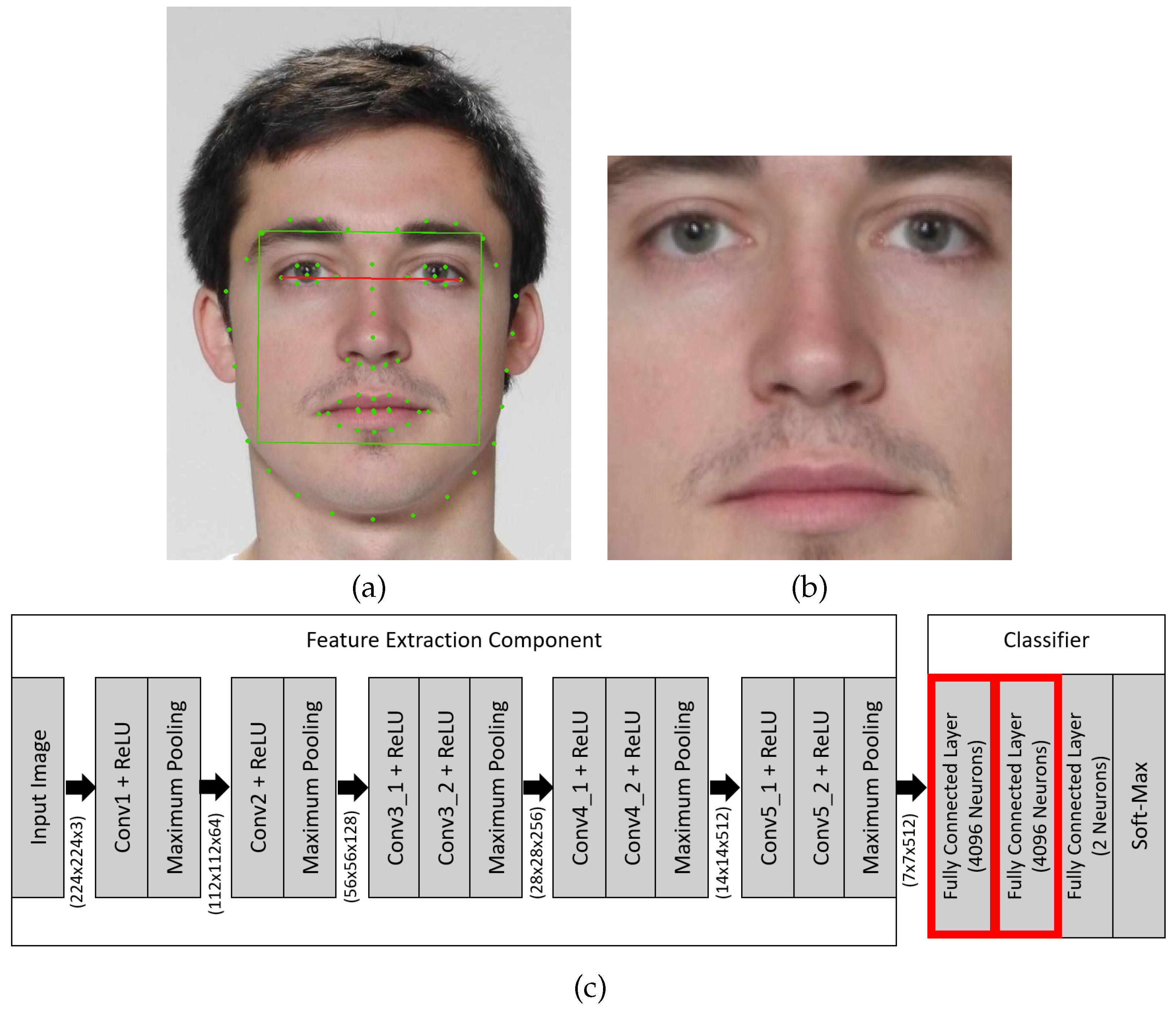
Feature Focus Towards Explainable And Transparent Deep Face Morphing To foster the research of face morphing attack detection, the database will be released to researchers for academic research purpose upon request. the database is developed based on the face images from the public nd iiitd database and the self collected face images. Bibliographic details on face morphing attack detection and localization based on feature wise supervision. It is carried out by comparing a suspect image with the biometric references contained in a watchlist, and its detection process is accomplished by analyzing the results of face comparison. once a morphed image is detected, its morphing attacker is also identified. In this work, we address this generalization problem by adapting a pixel wise supervision approach where we train a network to classify each pixel of the image into an attack or not, rather than only having one label for the whole image.
Comments are closed.