Face Morphing Attacks Explained Cybersecurity Threats Prevention
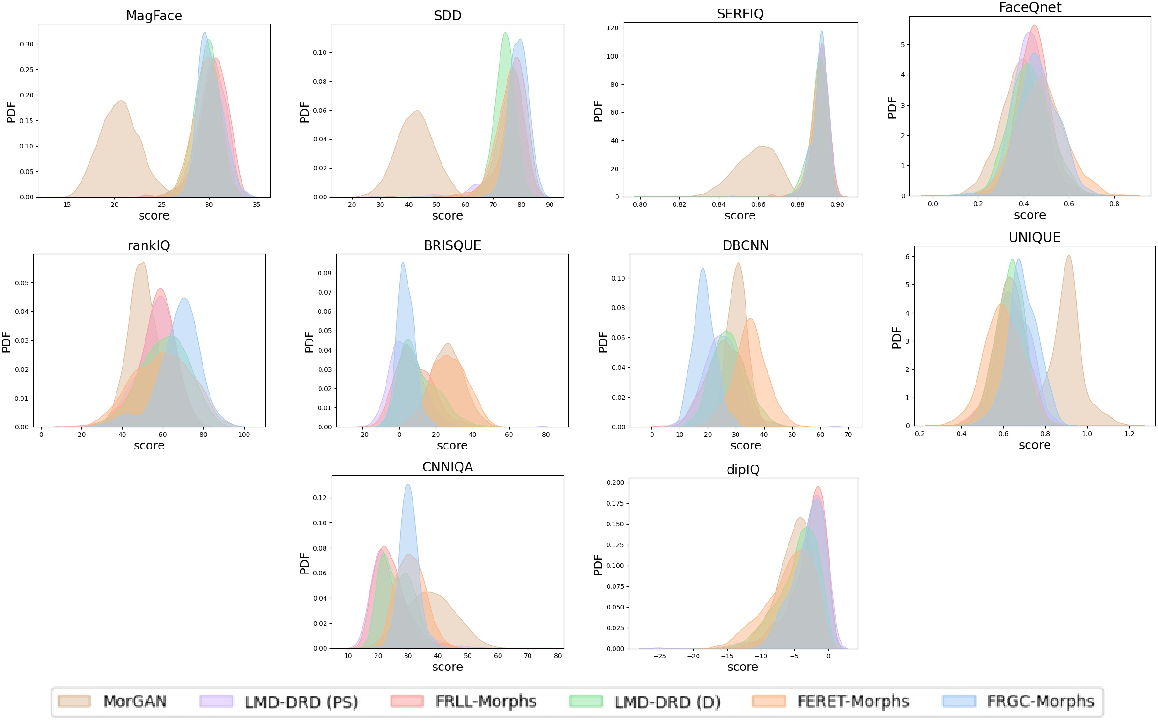
Face Morphing Attacks And Face Image Quality The Effect Of Morphing In this 5 minute explainer, we break down how morphing attacks work, the most common techniques (2d, 3d, mesh & feature based), and why humans often fail to spot them. Face morphing is a sophisticated image manipulation technique that poses a serious threat to digital identities of users online. explore how facial morphing works and what are its prevention techniques.
Detection And Generation Of Face Morphing Attacks Pptx This survey aims to present a systematic overview of the progress made in the area of face morphing in terms of both morph generation and morph detection. The aim of this paper is to present a qualitative assessment of the morphing attack issue, and the challenges it entails, highlighting both the technological and human aspects of the problem. Abstract: the possibility of various illegal acts increases when face recognition and authentication systems fail. current face recognition systems can be easily compromised by various biometric techniques. this study focuses on attack detection using morphing. This paper aims to provide a comprehensive overview of face morphing attacks and the developments happening in this field.
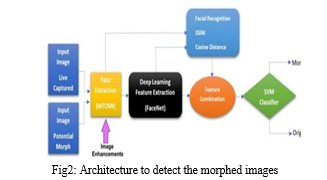
Generation And Detection Of Face Morphing Attacks Abstract: the possibility of various illegal acts increases when face recognition and authentication systems fail. current face recognition systems can be easily compromised by various biometric techniques. this study focuses on attack detection using morphing. This paper aims to provide a comprehensive overview of face morphing attacks and the developments happening in this field. Here, we investigate human and computer performance with high quality morphs, comparable with those expected to be used by criminals. over four experiments, we found that people were highly error prone when detecting morphs and that training did not produce improvements. Face photo morphing enables identity fraud, allowing multiple individuals to share one passport. learn about real world cases, detection methods, and how organizations can defend against this growing threat. In this project, we aim to explore both the creation and detection of face morphing attacks. Face morphing attacks pose a critical security threat to biometric systems by blending features of two individuals into a single synthetic image that can be falsely accepted by facial.

3 D Face Morphing Attacks Generation Vulnerability And Detection Pdf Here, we investigate human and computer performance with high quality morphs, comparable with those expected to be used by criminals. over four experiments, we found that people were highly error prone when detecting morphs and that training did not produce improvements. Face photo morphing enables identity fraud, allowing multiple individuals to share one passport. learn about real world cases, detection methods, and how organizations can defend against this growing threat. In this project, we aim to explore both the creation and detection of face morphing attacks. Face morphing attacks pose a critical security threat to biometric systems by blending features of two individuals into a single synthetic image that can be falsely accepted by facial.

Vulnerability Of Face Morphing Attacks A Case Study On Lookalike And In this project, we aim to explore both the creation and detection of face morphing attacks. Face morphing attacks pose a critical security threat to biometric systems by blending features of two individuals into a single synthetic image that can be falsely accepted by facial.

Face Feature Visualisation Of Single Morphing Attack Detection Deepai
Comments are closed.