Cybersecurity Cryptography Rsa Algorithm Youtube
Cybersecurity Cryptography Rsa Algorithm Youtube Understand the fundamentals of public key cryptography. explore the key components of the rsa algorithm and how they work together. Unlock the power of rsa, one of the most important cryptographic algorithms in cybersecurity! 🚀 in this video, we dive deep into the rsa algorithm, covering everything from its.

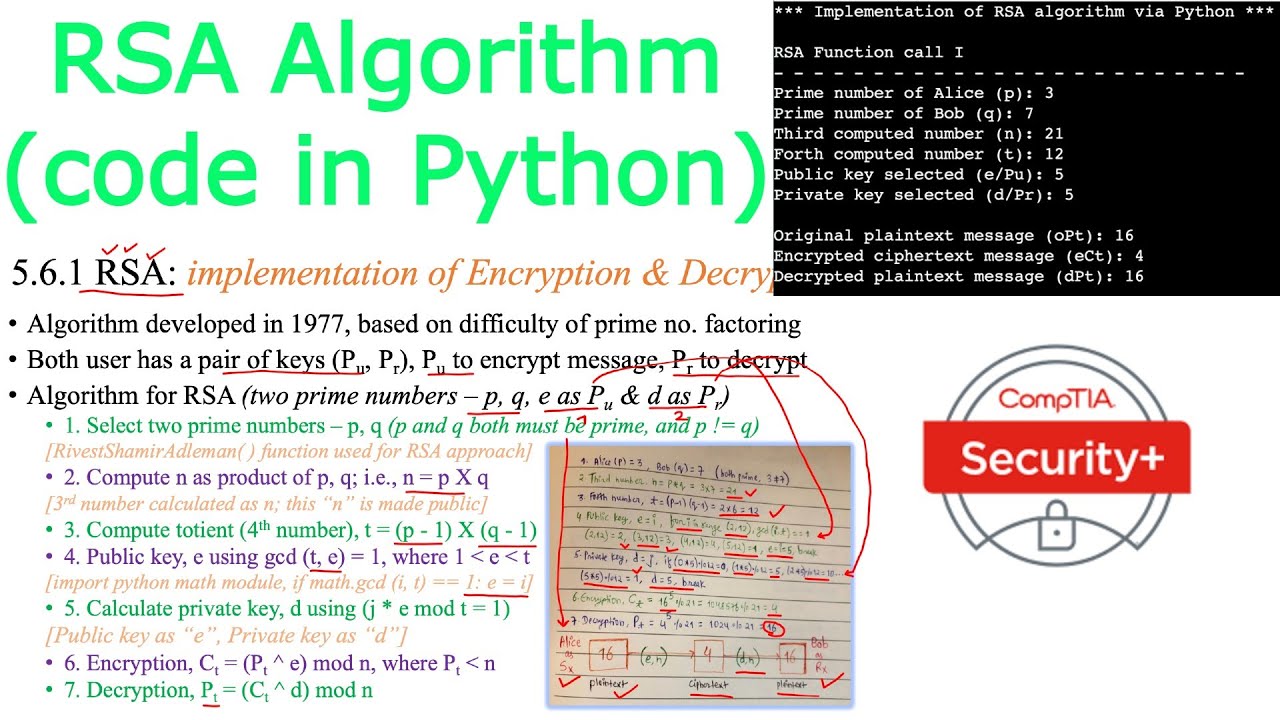
Rsa Algorithm Example Public Key Cryptography Asymmetric By the end of this video, you’ll have a solid understanding of how rsa works, from key generation to encryption and decryption, with a practical example of how alice can send a secure message to. Don't worry – i'll guide you through these fundamentals to ensure you're well prepared. 🔑 decoding rsa: the highlight of this video is our detailed breakdown of the rsa cryptosystem. Learn about the rsa algorithm, a fundamental public key encryption method, in this 23 minute video tutorial. explore the step by step process of generating public and private keys, including selecting prime numbers, calculating necessary values, and applying the keys for encryption and decryption. Hello everyone, welcome back, in this video, i am explaining rsa algorithm of asymmetric cryptography (developed in 1977, based on difficulty of factoring prime numbers) !.
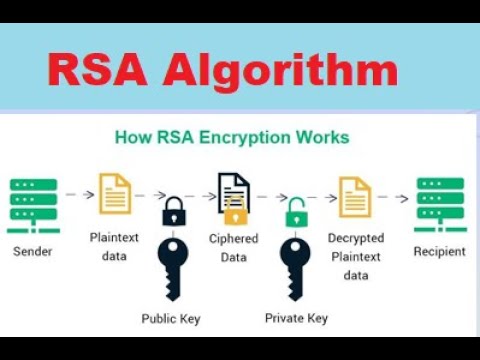
Rsa Algorithm In Information Security Public Key Cryptography Rsa Learn about the rsa algorithm, a fundamental public key encryption method, in this 23 minute video tutorial. explore the step by step process of generating public and private keys, including selecting prime numbers, calculating necessary values, and applying the keys for encryption and decryption. Hello everyone, welcome back, in this video, i am explaining rsa algorithm of asymmetric cryptography (developed in 1977, based on difficulty of factoring prime numbers) !. Rsa algorithm is a public key cryptosystem invented by three scientists in 1977. encryption involves exponentiation using a public key, while decryption requires a private key. We understand the basics of asymmetric encryption, handling of digital signatures, and how we can use rsa encryption algorithm in the verification of documents and safeguarding of private. The rsa encryption algorithm (1 of 2: computing an example) diffi hellman key exchange algorithm | cryptography and network security. Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data.
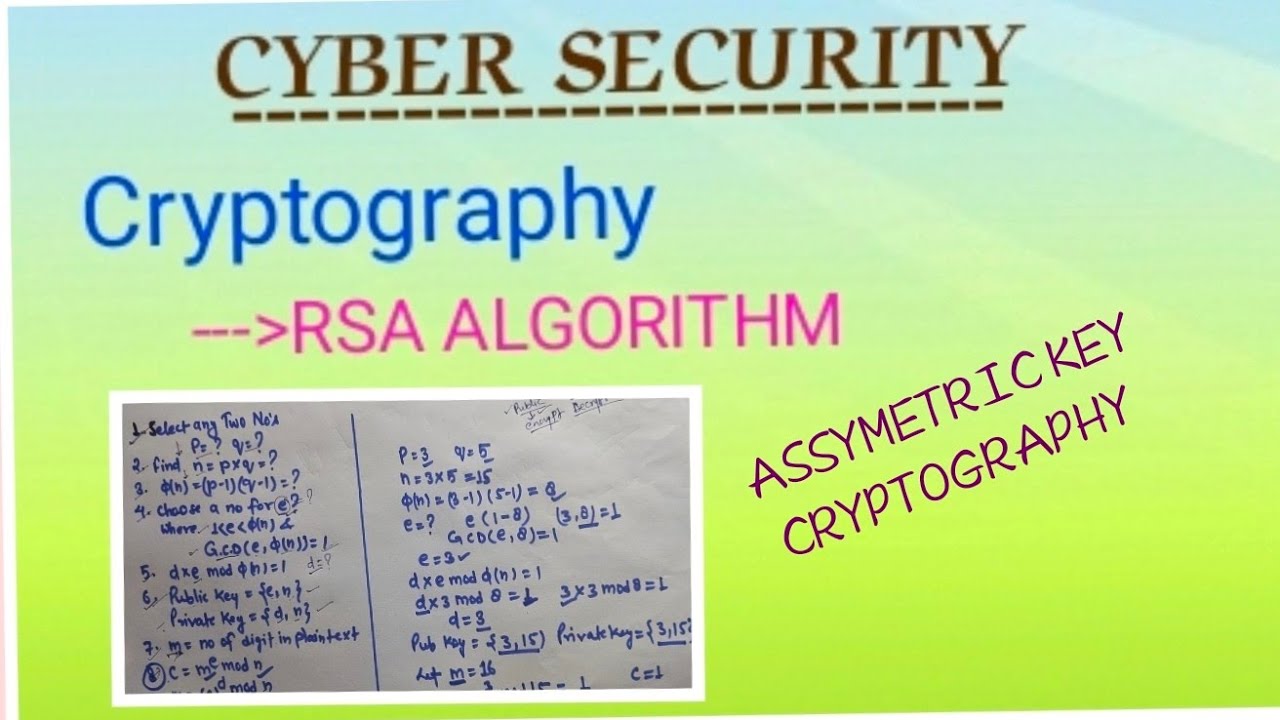
Rsa Algorithm Asymmetric Key Cryptography рџ ќпёџcyber Security Bca Rsa algorithm is a public key cryptosystem invented by three scientists in 1977. encryption involves exponentiation using a public key, while decryption requires a private key. We understand the basics of asymmetric encryption, handling of digital signatures, and how we can use rsa encryption algorithm in the verification of documents and safeguarding of private. The rsa encryption algorithm (1 of 2: computing an example) diffi hellman key exchange algorithm | cryptography and network security. Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data.
Cryptography Rsa Algorithm The rsa encryption algorithm (1 of 2: computing an example) diffi hellman key exchange algorithm | cryptography and network security. Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data.

Rsa Algorithm In Cryptography And Network Security Asymmetric
Comments are closed.