Rsa Algorithm Example Public Key Cryptography Asymmetric
Public Key Cryptography Rsa Algorithm Example Gate Vidyalay Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key. The rsa algorithm involves four steps: key generation, key distribution, public key operation (used for encryption or verifying a signature), and private key operation (used for decryption or signing a message). a basic principle behind rsa is the observation that it is practical to find three very large positive integers e, d, and n, such that for all integers x (0 ≤ x < n), both (xe)d and.

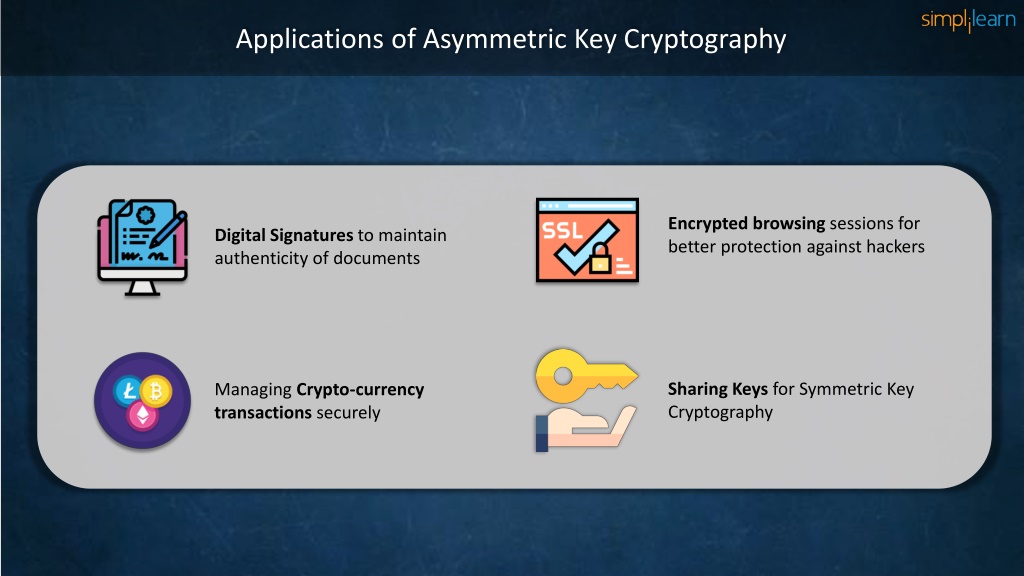
Public Key Cryptography Rsa Algorithm Example Gate Vidyalay However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Using the keys we generated in the example above, we run through the encryption process. recall, that with asymmetric encryption, we are encrypting with the public key, and decrypting with the private key. Unlike symmetric cryptography, where the key is typically just a random series of bytes, rsa keys have a complex internal structure with specific mathematical properties. To get the speed of symmetric key operations in open systems, key exchange protocols have been developed that initially use public key operations to establish a shared key for a given communication session and then use that shared key (under, e.g., aes) for the remainder of the session.
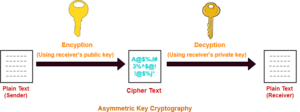
Public Key Cryptography Rsa Algorithm Example Gate Vidyalay Unlike symmetric cryptography, where the key is typically just a random series of bytes, rsa keys have a complex internal structure with specific mathematical properties. To get the speed of symmetric key operations in open systems, key exchange protocols have been developed that initially use public key operations to establish a shared key for a given communication session and then use that shared key (under, e.g., aes) for the remainder of the session. It is called an asymmetric algorithm because it uses two different keys for the encryption and decryption process. one key is public and can be shared, while the other is private and only known to the recipient of the encrypted data. What is the rsa algorithm? the rsa algorithm is an asymmetric cryptographic algorithm that relies on two keys: a public key for encryption and a private key for decryption. this concept of using two keys is what defines asymmetric cryptography. Rsa encryption, a type of public key cryptography, is one of the encryption algorithms that employ asymmetric encryption. introduced in 1977, rsa was named after its inventors—ron rivest, adi shamir, and leonard adleman. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success.
Rsa Algorithm Public Key Cryptography Ppt It is called an asymmetric algorithm because it uses two different keys for the encryption and decryption process. one key is public and can be shared, while the other is private and only known to the recipient of the encrypted data. What is the rsa algorithm? the rsa algorithm is an asymmetric cryptographic algorithm that relies on two keys: a public key for encryption and a private key for decryption. this concept of using two keys is what defines asymmetric cryptography. Rsa encryption, a type of public key cryptography, is one of the encryption algorithms that employ asymmetric encryption. introduced in 1977, rsa was named after its inventors—ron rivest, adi shamir, and leonard adleman. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success.
Ppt Asymmetric Key Cryptography Rsa Encryption Algorithm With Rsa encryption, a type of public key cryptography, is one of the encryption algorithms that employ asymmetric encryption. introduced in 1977, rsa was named after its inventors—ron rivest, adi shamir, and leonard adleman. Asymmetric cryptography for cissp: rsa, ecc, and pki explained with key concepts and real world uses for exam success.
Comments are closed.