Rsa Algorithm In Cryptography And Network Security Asymmetric
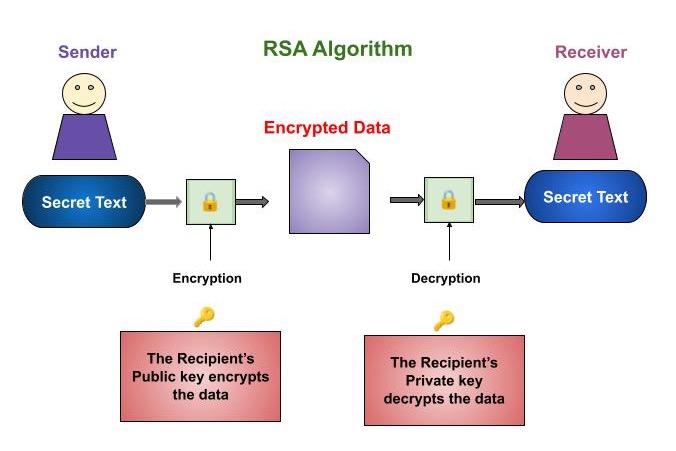
Cryptography Rsa Algorithm Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key. My immediate goal in this section is to convey to the reader what is meant by cca. as to how rsa is made secure against cca is a story of what goes into the padding bytes that are prepended to the data bytes in order to create a block of bytes that spans the width of the modulus.
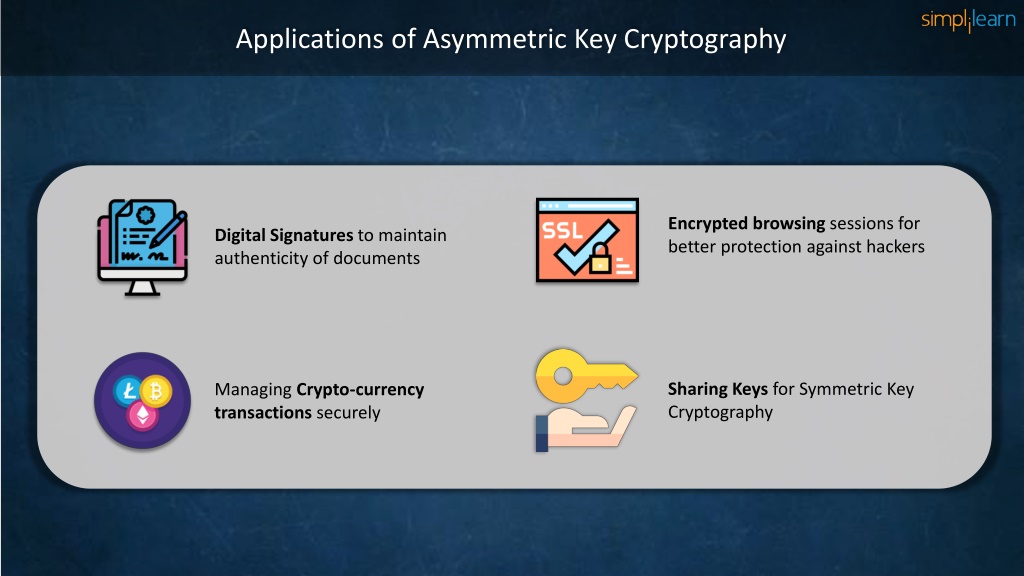
Ppt Asymmetric Key Cryptography Rsa Encryption Algorithm With As a result of this work, cryptographers now recommend the use of provably secure padding schemes such as optimal asymmetric encryption padding, and rsa laboratories has released new versions of pkcs #1 that are not vulnerable to these attacks. Rsa signature verification is one of the most commonly performed operations in network connected systems. rsa is a type of asymmetric encryption, which uses linked public and private keys. symmetric encryption uses only a private key. Rsa encryption, a type of public key cryptography, is one of the encryption algorithms that employ asymmetric encryption. introduced in 1977, rsa was named after its inventors—ron rivest, adi shamir, and leonard adleman. This attribute is one reason why rsa has become the most widely used asymmetric algorithm: it provides a method of assuring the confidentiality, integrity, authenticity and non reputability of electronic communications and data storage.
Ppt Asymmetric Key Cryptography Rsa Encryption Algorithm With Rsa encryption, a type of public key cryptography, is one of the encryption algorithms that employ asymmetric encryption. introduced in 1977, rsa was named after its inventors—ron rivest, adi shamir, and leonard adleman. This attribute is one reason why rsa has become the most widely used asymmetric algorithm: it provides a method of assuring the confidentiality, integrity, authenticity and non reputability of electronic communications and data storage. Algorithms like rsa and ecc — combined with the structure of pki — turn open networks into controlled, verifiable spaces where only trusted devices and users can communicate. Learn the main types of encryption — symmetric (aes) and asymmetric (rsa) — with side by side comparisons, real world use cases, and a decision checklist for it teams. Rivest shamir adleman (rsa) is a well known public key or asymmetric cryptographic algorithm. it protects sensitive data through encryption and decryption using a private and public key pair. Abstract aphy method used to securely transmit data. it uses a public and pri ate key pair for encryption and decryption. rsa works by making it computationally difficult for anyone to derive the private key from the public key, ven though they are related mathematically. this project explains the math concepts behind rsa and shows how to im.

Ppt Asymmetric Key Cryptography Rsa Encryption Algorithm With Algorithms like rsa and ecc — combined with the structure of pki — turn open networks into controlled, verifiable spaces where only trusted devices and users can communicate. Learn the main types of encryption — symmetric (aes) and asymmetric (rsa) — with side by side comparisons, real world use cases, and a decision checklist for it teams. Rivest shamir adleman (rsa) is a well known public key or asymmetric cryptographic algorithm. it protects sensitive data through encryption and decryption using a private and public key pair. Abstract aphy method used to securely transmit data. it uses a public and pri ate key pair for encryption and decryption. rsa works by making it computationally difficult for anyone to derive the private key from the public key, ven though they are related mathematically. this project explains the math concepts behind rsa and shows how to im.

Understanding The Rsa Algorithm A Deep Dive Into Asymmetric Cryptography Rivest shamir adleman (rsa) is a well known public key or asymmetric cryptographic algorithm. it protects sensitive data through encryption and decryption using a private and public key pair. Abstract aphy method used to securely transmit data. it uses a public and pri ate key pair for encryption and decryption. rsa works by making it computationally difficult for anyone to derive the private key from the public key, ven though they are related mathematically. this project explains the math concepts behind rsa and shows how to im.

Asymmetric Cryptography Module Rsa Algorithm Prime Factorization
Comments are closed.