Api Jwt Attack And Mitigation Sailor Security

Api Jwt Attack And Mitigation Sailor Security Jwt vulnerabilities may originate from improper implementation, weak security practices of flow in token generation. these vulnerabilities can be exploited by attacker to impersonate users, gain unauthorized access or break integrity of data stored on system. As jwts are most commonly used in authentication, session management, and access control mechanisms, these vulnerabilities can potentially compromise the entire website and its users. don't worry if you're not familiar with jwts and how they work we'll cover all of the relevant details as we go.

Jwt Algorithm Confusion Attack Solution Securityboat Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. Jwt storage cookie xss protections (httponly & secure flags) are not available for browser local session storage. best practice memory only jwt token handling. protection of the crypto keys (server side). protection against csrf it’s not jwt tokens, it’s about how you use them. Validating json web tokens (jwts) with hs512 signatures is crucial for securing api communication. this guide walks you through implementing robust jwt validation within the sailor framework. Comprehensive guide to jwt security vulnerabilities, exploitation techniques, and mitigation strategies.
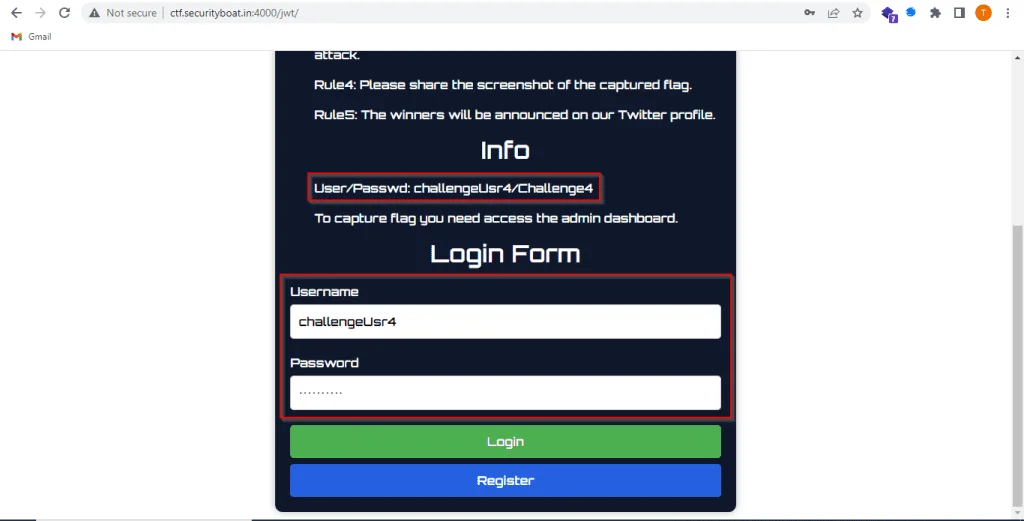
Jwt Algorithm Confusion Attack Solution Securityboat Validating json web tokens (jwts) with hs512 signatures is crucial for securing api communication. this guide walks you through implementing robust jwt validation within the sailor framework. Comprehensive guide to jwt security vulnerabilities, exploitation techniques, and mitigation strategies. In this article, we'll explore various methods by which jwts can be vulnerable to allow for authentication bypasses and injection attacks, demonstrating the importance of testing such implementations and the effectiveness of following best practices. let's dive in!. Explore common jwt attacks and vulnerabilities, including token tampering, signature bypass, and expiration exploits. learn how to secure your applications. The instructions detail a method to assess the security of jwt tokens, particularly those employing a “jku” header claim. this claim should link to a jwks (json web key set) file that contains the public key necessary for the token’s verification. Learn to validate jwts with hs512 in sailor. secure your api endpoints effectively with this practical guide for developers.
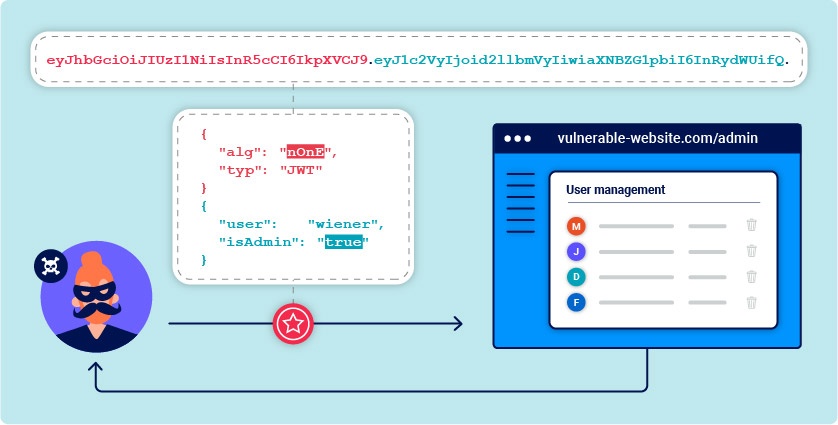
Jwt Attacks Web Security Academy In this article, we'll explore various methods by which jwts can be vulnerable to allow for authentication bypasses and injection attacks, demonstrating the importance of testing such implementations and the effectiveness of following best practices. let's dive in!. Explore common jwt attacks and vulnerabilities, including token tampering, signature bypass, and expiration exploits. learn how to secure your applications. The instructions detail a method to assess the security of jwt tokens, particularly those employing a “jku” header claim. this claim should link to a jwks (json web key set) file that contains the public key necessary for the token’s verification. Learn to validate jwts with hs512 in sailor. secure your api endpoints effectively with this practical guide for developers.

Enhancing Api Security With Jwt Core Detections Impart Security The instructions detail a method to assess the security of jwt tokens, particularly those employing a “jku” header claim. this claim should link to a jwks (json web key set) file that contains the public key necessary for the token’s verification. Learn to validate jwts with hs512 in sailor. secure your api endpoints effectively with this practical guide for developers.

Understanding Jwt Basics And Security Risks Laburity
Comments are closed.