Jwt Manipulation Attacks And Mitigating Api Security Project Part8

A Study On A Jwt Based User Authentication And Api Pdf Computer Jwt (json web token) is widely used for securing apis, but if not properly validated, it can become an attack vector. we showed: how a maliciously modified jwt token can be used to access. Jwts are widely used for authentication and authorization, but when misconfigured, they can open doors to serious vulnerabilities. here i am trying to sove the jwt security lab from.
Issue 56 Common Jwt Attacks Owasp Api Security Top 10 Cheat Sheet We showed: how a maliciously modified jwt token can be used to access protected resources. how fortiweb waf can detect and block these malicious requests, ensuring only legitimate tokens pass. Learn how to safeguard your applications from jwt vulnerabilities that can lead to token forgery and data manipulation. discover secure implementation practices with real world example code to ensure robust api security. Developers tend to trust data received from third party apis more than user input, and so tend to adopt weaker security standards. in order to compromise apis, attackers go after integrated third party services instead of trying to compromise the target api directly. In this section, we'll look at how design issues and flawed handling of json web tokens (jwts) can leave websites vulnerable to a variety of high severity attacks.
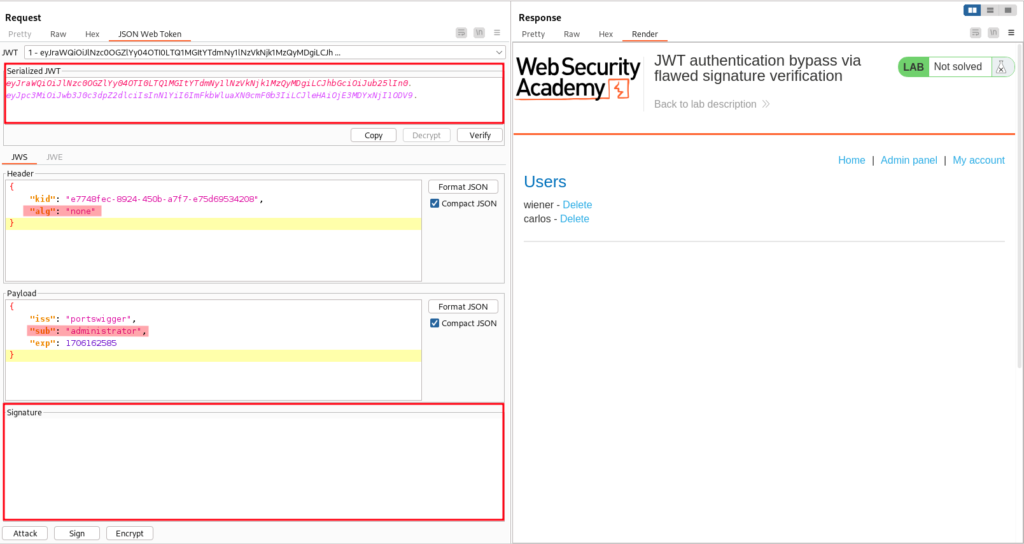
Jwt Attacks Developers tend to trust data received from third party apis more than user input, and so tend to adopt weaker security standards. in order to compromise apis, attackers go after integrated third party services instead of trying to compromise the target api directly. In this section, we'll look at how design issues and flawed handling of json web tokens (jwts) can leave websites vulnerable to a variety of high severity attacks. The instructions detail a method to assess the security of jwt tokens, particularly those employing a “jku” header claim. this claim should link to a jwks (json web key set) file that contains the public key necessary for the token’s verification. Comprehensive guide to jwt security vulnerabilities, exploitation techniques, and mitigation strategies. Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. Importance of building secure applications and raise awareness about the potential pitfalls of jwt usage when not secured.

Jwt Attacks The instructions detail a method to assess the security of jwt tokens, particularly those employing a “jku” header claim. this claim should link to a jwks (json web key set) file that contains the public key necessary for the token’s verification. Comprehensive guide to jwt security vulnerabilities, exploitation techniques, and mitigation strategies. Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. Importance of building secure applications and raise awareness about the potential pitfalls of jwt usage when not secured.

Jwt Attacks Erik Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. Importance of building secure applications and raise awareness about the potential pitfalls of jwt usage when not secured.
Comments are closed.