Zero Trust Harden Data Security With Intel Xeon Processors

Zero Trust Harden Data Security With Intel Xeon Processors This solution hardens security by combining powerful open source software with advanced hardware features on 3rd, 4th and 5th gen intel xeon scalable processors and intel xeon d 2700 1700 processors. Lockheed martin hardened security* offers a hardened, full stack security solution that utilizes attribute based controls to isolate and protect virtual machines (vms) at runtime and allocate compute resources for more consistent performance that creates a zero trust environment.

Trust Your Zero Trust Security Strategy The advanced crypto acceleration technologies embedded in intel xeon processors enable greater levels of cryptographic security, enhance performance, and allow for a more seamless user experience—without adding more cores and processors to the data center. We accelerate your zero trust adoption through extensive cyber resilient capabilities and a seven pillar approach that allows users to verify at every point in the it environment before permissions are granted. This paper provides a reference on how to build a more secure full disk encryption system with the 3rd, 4th and 5th gen intel® xeon® scalable processors. download pdf. This paper reviews the security features of the 3rd gen intel xeon scalable processor, such as intel tme, cryptographic instruction performance enhancements, and intel sgx, and demonstrates how to apply them with hashicorp vault to create a high performing zero trust solution.
Zero Trust Cybersecurity And System Hardening For Oil Gas This paper provides a reference on how to build a more secure full disk encryption system with the 3rd, 4th and 5th gen intel® xeon® scalable processors. download pdf. This paper reviews the security features of the 3rd gen intel xeon scalable processor, such as intel tme, cryptographic instruction performance enhancements, and intel sgx, and demonstrates how to apply them with hashicorp vault to create a high performing zero trust solution. The 3rd gen intel® xeon® scalable processor enables confidential computing with a series of on chip security features, including intel® total memory encryption (intel® tme), crypto ni, and intel® software guard extensions (intel® sgx). This business brief describes how 4th gen intel® xeon® scalable processors and built in intel® accelerators benefit cloud security and these top workloads – hyperconverged architecture, confidential computing, network management – among others. Intel xeon processors with intel® security engines provide a hardware based solution for confidential computing, allowing businesses to extract insights or deploy ai models and harness the power of data while helping keep it private. Intel xeon scalable processors with intel security engines provide a hardware based solution for confidential computing, allowing businesses to extract insights or deploy ai models and harness the power of data while helping keep it private.
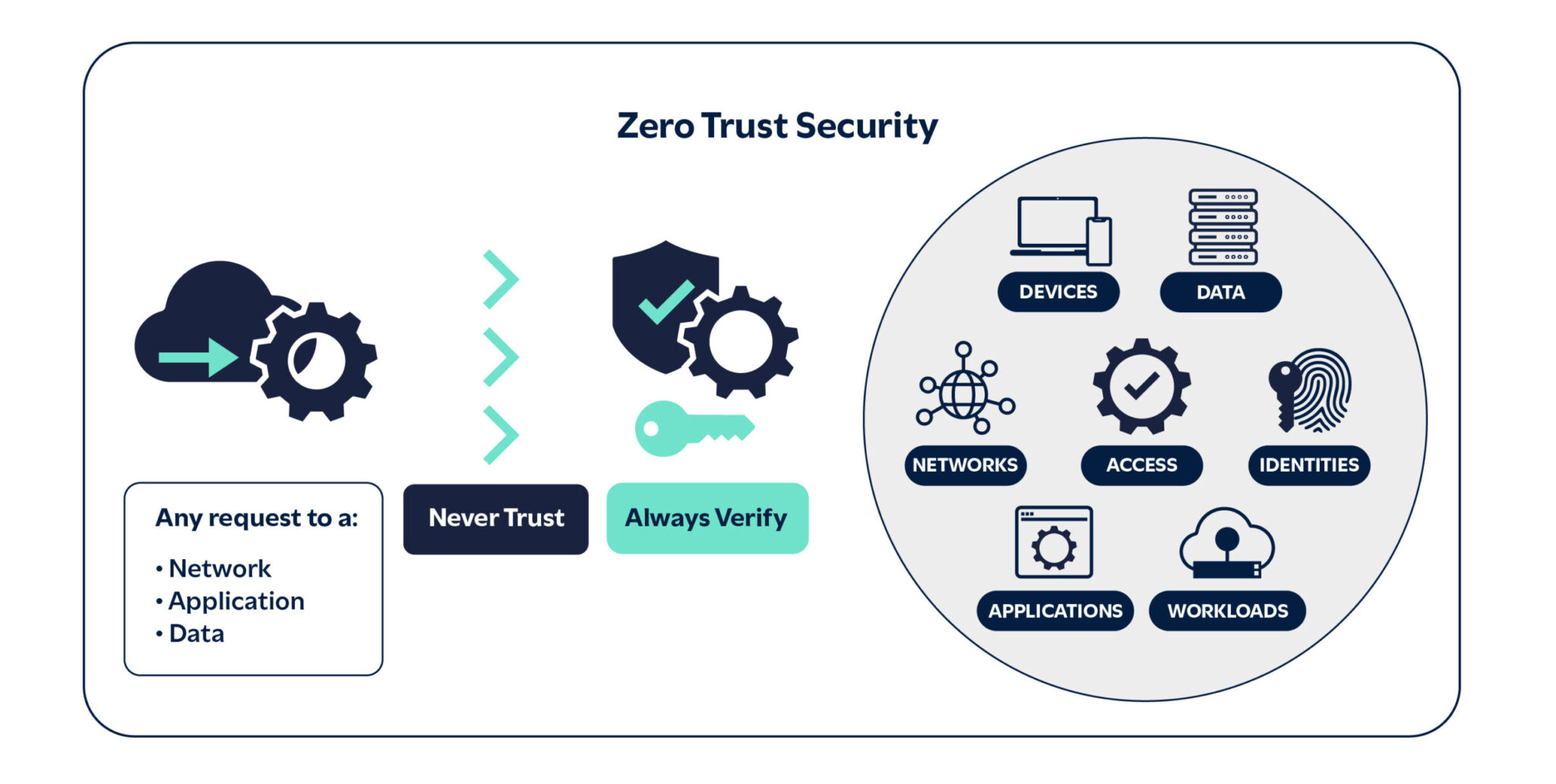
Understanding Zero Trust Principles Use Cases Benefits C8 Secure The 3rd gen intel® xeon® scalable processor enables confidential computing with a series of on chip security features, including intel® total memory encryption (intel® tme), crypto ni, and intel® software guard extensions (intel® sgx). This business brief describes how 4th gen intel® xeon® scalable processors and built in intel® accelerators benefit cloud security and these top workloads – hyperconverged architecture, confidential computing, network management – among others. Intel xeon processors with intel® security engines provide a hardware based solution for confidential computing, allowing businesses to extract insights or deploy ai models and harness the power of data while helping keep it private. Intel xeon scalable processors with intel security engines provide a hardware based solution for confidential computing, allowing businesses to extract insights or deploy ai models and harness the power of data while helping keep it private.
Comments are closed.