Zero Trust Security Model In Cloud Vpsie Articles
Zero Trust Security Model In Cloud Vpsie Articles Discover the power of zero trust security model in cloud environments. uncover the key principles and strategies for a resilient and secure digital landscape. This paper systematically compares the current mainstream cybersecurity models, thoroughly explores the advantages and limitations of the zero trust model, and provides an in depth review of its components and key technologies.
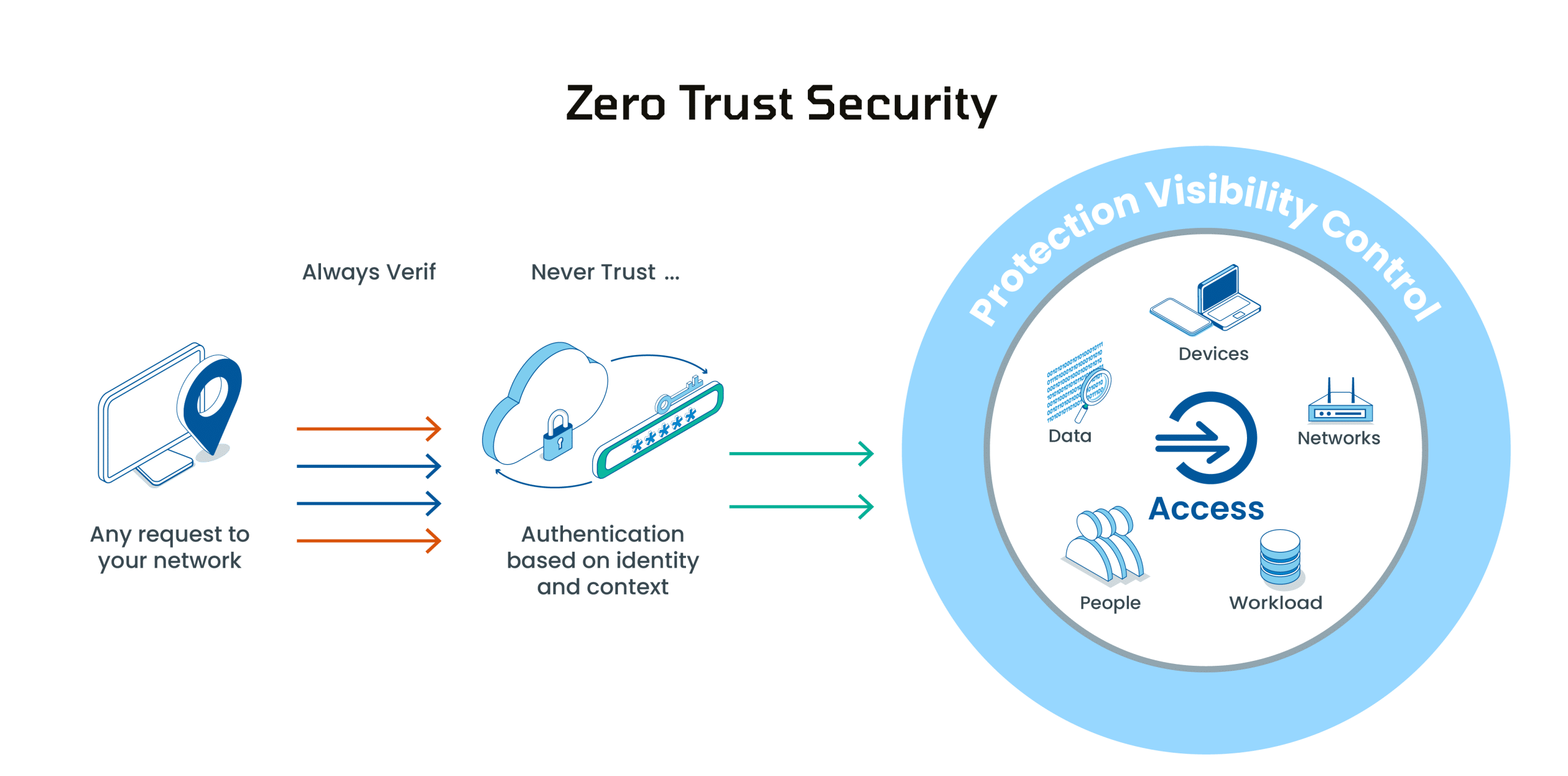
Zero Trust Security Model In Cloud Vpsie Articles Cloud computing has become essential in this digital world as it provides opportunities and challenges for organizations. this research explores the implementation and effectiveness of zero. Zero trust security models (ztsm) have emerged as a robust framework to mitigate these risks by enforcing the principle of "never trust, always verify." this review examines the foundational principles, architectural components, and practical implementations of zero trust in cloud environments. This paper compares security based features of recently published zero trust based cloud network models, frameworks and proofs of concept employed for network security. Implementing zero trust architecture (zta) in cloud native environments, while offering substantial security benefits, introduces a range of performance, scalability, and operational challenges.
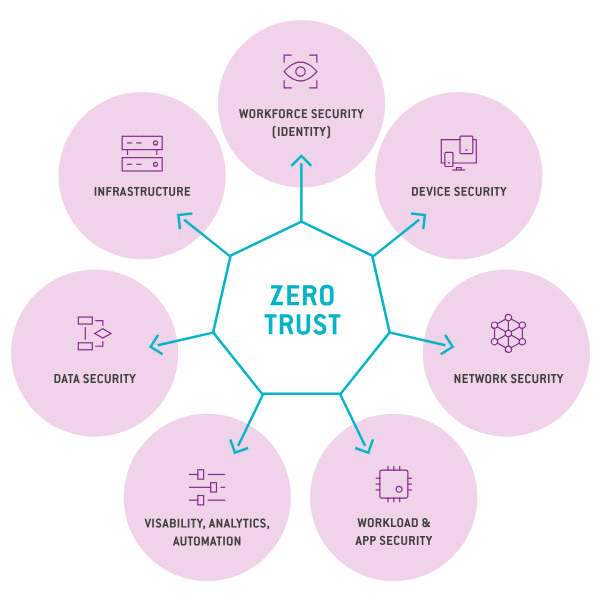
9 Benefits Of Zero Trust Architecture Security Boulevard This paper compares security based features of recently published zero trust based cloud network models, frameworks and proofs of concept employed for network security. Implementing zero trust architecture (zta) in cloud native environments, while offering substantial security benefits, introduces a range of performance, scalability, and operational challenges. This paper offers an extensive exploration of zero trust in cloud computing environments, delving into its principles, architecture, implementation strategies, challenges, and anticipated future developments. As they try to understand how to protect the isolation of tenants, stop alteration movements, and support identity cross services, the paper investigates the challenges and parts of zero trust taking effect in the multi tenant cloud. Zero trust is well suited to securing access from diverse and potentially untrusted locations. this article will explore the core principles of zero trust architecture, its implementation strategies in platform engineering, and the benefits it offers in securing modern, distributed systems. The zero trust security model has emerged as a leading approach to secure modern it environments. while traditional perimeter based defenses assume everything inside the network is trustworthy, zero trust operates on the principle that threats may exist both inside and outside the network.

Zero Trust Security Model Geeksforgeeks This paper offers an extensive exploration of zero trust in cloud computing environments, delving into its principles, architecture, implementation strategies, challenges, and anticipated future developments. As they try to understand how to protect the isolation of tenants, stop alteration movements, and support identity cross services, the paper investigates the challenges and parts of zero trust taking effect in the multi tenant cloud. Zero trust is well suited to securing access from diverse and potentially untrusted locations. this article will explore the core principles of zero trust architecture, its implementation strategies in platform engineering, and the benefits it offers in securing modern, distributed systems. The zero trust security model has emerged as a leading approach to secure modern it environments. while traditional perimeter based defenses assume everything inside the network is trustworthy, zero trust operates on the principle that threats may exist both inside and outside the network.
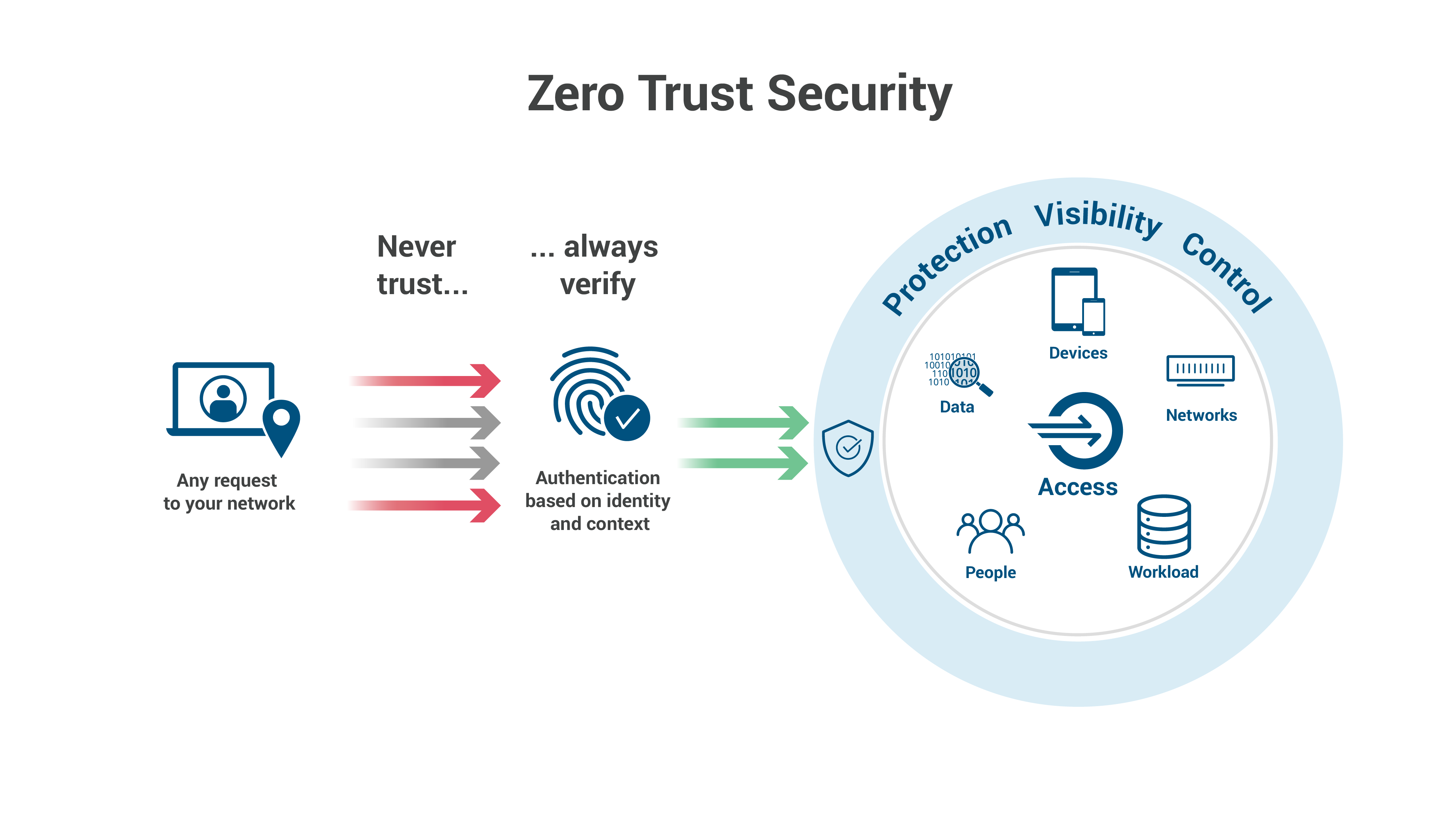
Implementing Zero Trust Architecture On Azure Hybrid Cloud Zero trust is well suited to securing access from diverse and potentially untrusted locations. this article will explore the core principles of zero trust architecture, its implementation strategies in platform engineering, and the benefits it offers in securing modern, distributed systems. The zero trust security model has emerged as a leading approach to secure modern it environments. while traditional perimeter based defenses assume everything inside the network is trustworthy, zero trust operates on the principle that threats may exist both inside and outside the network.
Comments are closed.