What Is A Digital Signature Algorithm Rsa Vs Dsa Algorithm
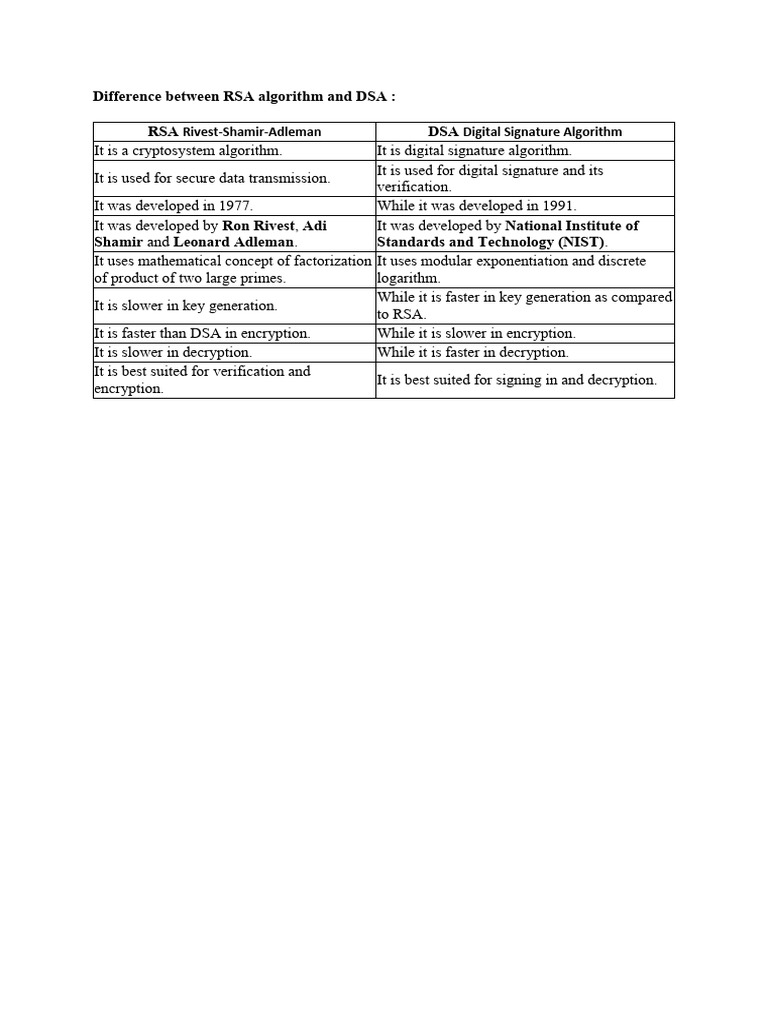
Difference Between Rsa Algorithm And Dsa Pdf Cryptography Encryption Whereas, rsa is used for secure data transmission and encryption, dsa is used for checking the authenticity of the message, generating and verifying signatures. Two of the most prominent asymmetric algorithms are rsa (rivest shamir adleman) and dsa (digital signature algorithm). while both rely on public private key cryptography, they differ sharply in design, mathematical foundations, and use cases.
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature In short, rsa is primarily used for encryption and decryption, while dsa is used to generate and validate digital signatures. both are useful cryptographic tools, with their own set of advantages and applications. Learn the core differences between rsa vs dsa algorithms, their benefits, working mechanisms, python implementations, and top applications in data security. We call several different algorithms rsa, some of which sign (e.g. rsa pss), some of which encrypt (e.g. rsa oaep). but we gave every algorithms in group based crypto a different name, calling one of the encryption algorithms elgamal encryption and calling one of the signature algorithms dsa. Rsa is a public‑key cryptosystem that can do encryption and signatures, built on the hardness of factoring large integers. dsa is a signature‑only algorithm built on discrete logarithms in a finite field.

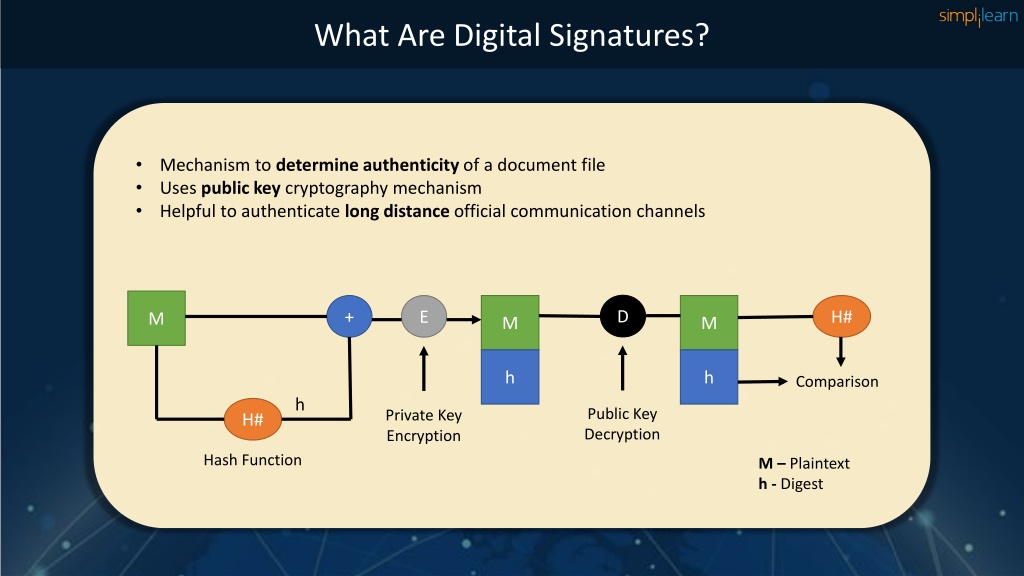
8 Dsa Digital Signature Algorithm Royalty Free Images Stock Photos We call several different algorithms rsa, some of which sign (e.g. rsa pss), some of which encrypt (e.g. rsa oaep). but we gave every algorithms in group based crypto a different name, calling one of the encryption algorithms elgamal encryption and calling one of the signature algorithms dsa. Rsa is a public‑key cryptosystem that can do encryption and signatures, built on the hardness of factoring large integers. dsa is a signature‑only algorithm built on discrete logarithms in a finite field. In rsa, the private key is used for decryption or signing, while the public key is used for encryption or signature verification. dsa, on the other hand, uses the private key strictly for signing and the public key strictly for verification. Digital signature algorithms, such as rsa (rivest shamir adleman) and dsa (digital signature algorithm), are widely used to generate and verify these signatures. In this article, we will dive into the difference between rsa algorithm and dsa algorithm in a tabular form. but let us first know a bit more about each of these in detail. Rsa and dsa signatures are crucial cryptographic tools for ensuring digital security. they use complex math to create unforgeable digital signatures, verifying the authenticity and integrity of messages or documents in various applications.
Ppt Dsa Digital Signature Algorithm Powerpoint Presentation Free In rsa, the private key is used for decryption or signing, while the public key is used for encryption or signature verification. dsa, on the other hand, uses the private key strictly for signing and the public key strictly for verification. Digital signature algorithms, such as rsa (rivest shamir adleman) and dsa (digital signature algorithm), are widely used to generate and verify these signatures. In this article, we will dive into the difference between rsa algorithm and dsa algorithm in a tabular form. but let us first know a bit more about each of these in detail. Rsa and dsa signatures are crucial cryptographic tools for ensuring digital security. they use complex math to create unforgeable digital signatures, verifying the authenticity and integrity of messages or documents in various applications.
Comments are closed.