Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature
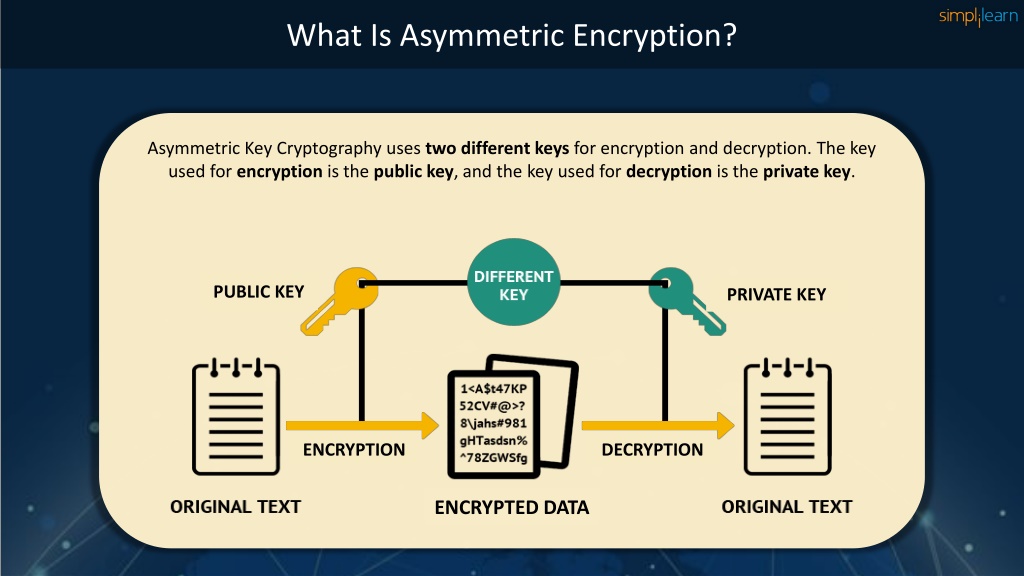
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature In this presentation on the dsa algorithm, we learn about the global standard in authentication and verification of digital signatures. The digital signature algorithm (dsa) is used to generate and verify digital signatures to prevent message tampering. it uses a key pair consisting of a private key and public key. to sign a message, the sender uses their private key to generate a signature based on the message.
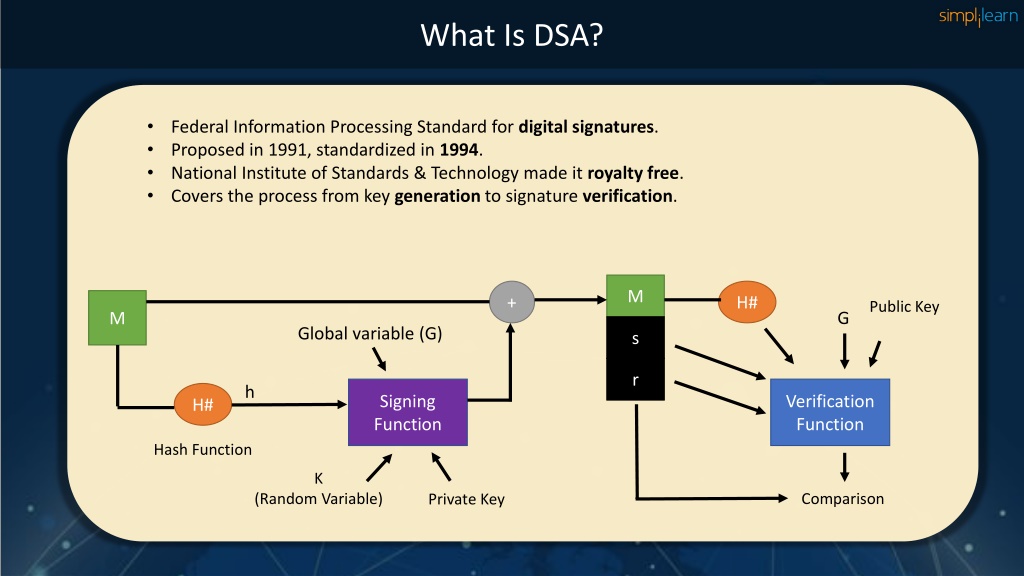
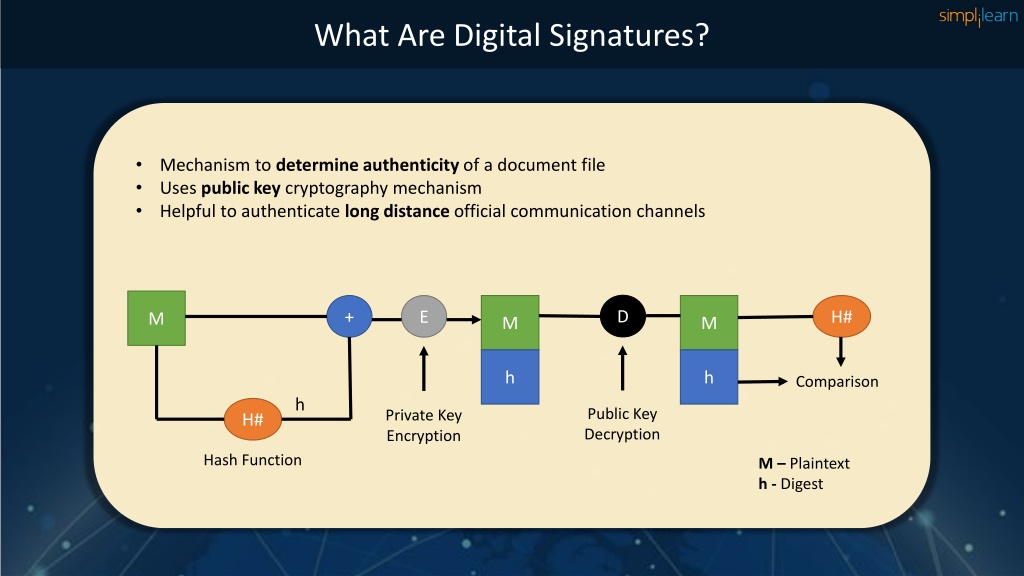
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature The dss makes use of the secure hash algorithm (sha) described in chapter 12 and presents a new digital signature technique, the digital signature algorithm (dsa). The digital signature algorithm (dsa) is a reliable and standardised mechanism for digital signatures that ensures message authenticity, integrity, and non repudiation. Technically, digital signature is performed by a signing algorithm and it is verified by a verification algorithm. a copy of digital (conventional) signature is identical (usually distinguishable) to (from) the origin. a care has therefore to be made that a classical signature is not misused. Cs555 topic 22 * outline and readings outline the dsa signature scheme lamport’s one time signature blind signature readings: katz and lindell: chapter 12.1 12.4 topic 22 * digital signature algorithm (dsa) also known as digital signature standard (dss) key generation select two prime numbers (p,q) such that q | (p 1) early standard.
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature Technically, digital signature is performed by a signing algorithm and it is verified by a verification algorithm. a copy of digital (conventional) signature is identical (usually distinguishable) to (from) the origin. a care has therefore to be made that a classical signature is not misused. Cs555 topic 22 * outline and readings outline the dsa signature scheme lamport’s one time signature blind signature readings: katz and lindell: chapter 12.1 12.4 topic 22 * digital signature algorithm (dsa) also known as digital signature standard (dss) key generation select two prime numbers (p,q) such that q | (p 1) early standard. Common algorithms like dsa are implemented in programming languages to enable digital signatures. cybersecurity frameworks provide guidance for assessing risks and developing strategies to mitigate threats. What is the digital signature algorithm (dsa) and how does it function? the digital signature algorithm (dsa) is a cryptographic standard that creates digital signatures using mathematical keys to verify document authenticity and sender identity. The dsa approach: the dsa uses an algorithm that is designed to provide only the digital signature function. at the sender: the hash code is provided as input to a signature function along with a random number k. In this guide, you will learn how dsa works, the key parameters used in the algorithm, the steps involved in signature generation and verification, and the security considerations when implementing digital signatures.
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature Common algorithms like dsa are implemented in programming languages to enable digital signatures. cybersecurity frameworks provide guidance for assessing risks and developing strategies to mitigate threats. What is the digital signature algorithm (dsa) and how does it function? the digital signature algorithm (dsa) is a cryptographic standard that creates digital signatures using mathematical keys to verify document authenticity and sender identity. The dsa approach: the dsa uses an algorithm that is designed to provide only the digital signature function. at the sender: the hash code is provided as input to a signature function along with a random number k. In this guide, you will learn how dsa works, the key parameters used in the algorithm, the steps involved in signature generation and verification, and the security considerations when implementing digital signatures.

Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature The dsa approach: the dsa uses an algorithm that is designed to provide only the digital signature function. at the sender: the hash code is provided as input to a signature function along with a random number k. In this guide, you will learn how dsa works, the key parameters used in the algorithm, the steps involved in signature generation and verification, and the security considerations when implementing digital signatures.
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature
Comments are closed.