Dsa Algorithm Dsa Algorithm Explained Digital Signature Algorithm
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature The digital signature algorithm (dsa) is a reliable and standardised mechanism for digital signatures that ensures message authenticity, integrity, and non repudiation. The digital signature algorithm (dsa) is a public key cryptosystem and federal information processing standard for digital signatures, based on the mathematical concept of modular exponentiation and the discrete logarithm problem.
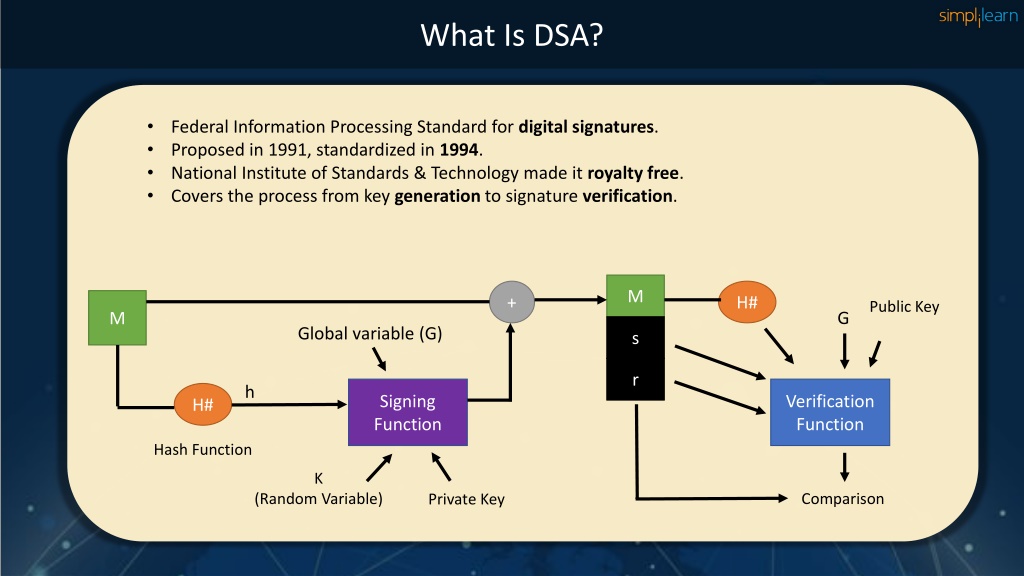
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature In this guide, you will learn how dsa works, the key parameters used in the algorithm, the steps involved in signature generation and verification, and the security considerations when implementing digital signatures. Navigating the digital signature algorithm (dsa) involves several key steps to ensure the secure exchange of digital messages. these steps include key generation, signature generation, and signature verification. The two standard ways to obtain digital signatures are rsa (rivest–shamir–adleman) and dsa (digital signature) algorithms, but both differ in performing encryption and decryption functions. Explore how the digital signature algorithm (dsa) works, its security features, and how it protects your online data integrity effectively.
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature The two standard ways to obtain digital signatures are rsa (rivest–shamir–adleman) and dsa (digital signature) algorithms, but both differ in performing encryption and decryption functions. Explore how the digital signature algorithm (dsa) works, its security features, and how it protects your online data integrity effectively. Cryptography | digital signature algorithm (dsa): in this tutorial, we will learn about the digital signature algorithm (dsa), its steps of encryption and decryption, and the types of messages in the digital signature algorithm. Credible authentication mechanisms must be addressed with digital space characterized by data security and integrity at stake. one such type is a mechanism such as a digital signature algorithm (dsa), a cryptographic method with authenticity, integrity, and non repudiation of electronic data. The digital signature algorithm (dsa) is a public key cryptographic algorithm developed by the national institute of standards and technology (nist) for generating and verifying digital signatures. The digital signature algorithm (dsa) is a fips (federal information processing standard) and public key cryptosystem that’s used for digital signatures. it utilizes the modular exponentiation and the discrete logarithm problem to generate 2 digital signatures.
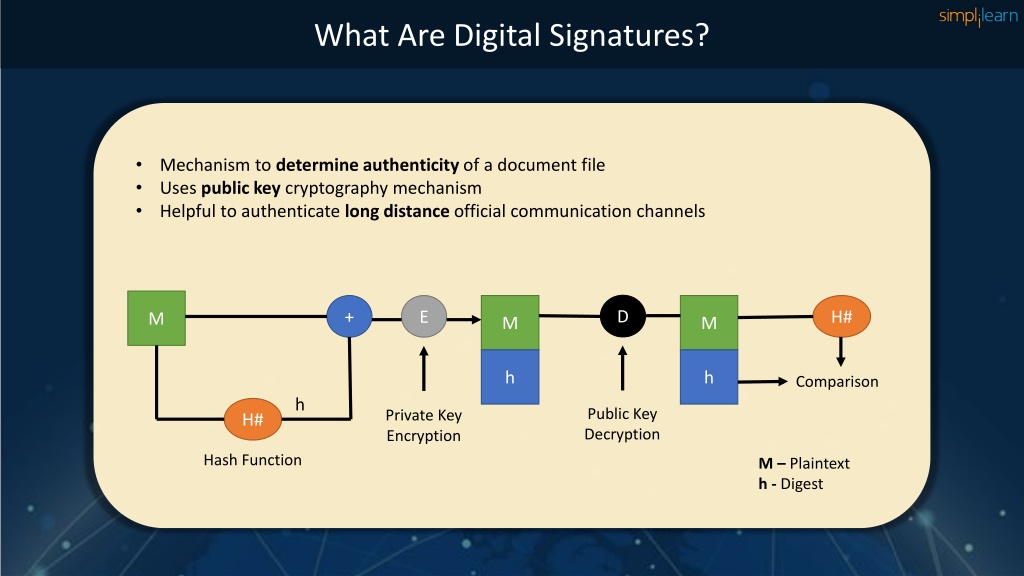
Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature Cryptography | digital signature algorithm (dsa): in this tutorial, we will learn about the digital signature algorithm (dsa), its steps of encryption and decryption, and the types of messages in the digital signature algorithm. Credible authentication mechanisms must be addressed with digital space characterized by data security and integrity at stake. one such type is a mechanism such as a digital signature algorithm (dsa), a cryptographic method with authenticity, integrity, and non repudiation of electronic data. The digital signature algorithm (dsa) is a public key cryptographic algorithm developed by the national institute of standards and technology (nist) for generating and verifying digital signatures. The digital signature algorithm (dsa) is a fips (federal information processing standard) and public key cryptosystem that’s used for digital signatures. it utilizes the modular exponentiation and the discrete logarithm problem to generate 2 digital signatures.

Ppt Dsa Algorithm Dsa Algorithm Explained Digital Signature The digital signature algorithm (dsa) is a public key cryptographic algorithm developed by the national institute of standards and technology (nist) for generating and verifying digital signatures. The digital signature algorithm (dsa) is a fips (federal information processing standard) and public key cryptosystem that’s used for digital signatures. it utilizes the modular exponentiation and the discrete logarithm problem to generate 2 digital signatures.
Comments are closed.