Types Of Authentication Protocols Geeksforgeeks

Introduction To Authentication Protocols Pdf Authentication In this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. 1. kerberos : kerberos is a protocol that aids in network authentication. this is used for validating clients servers during a network employing a cryptographic key. Authentication systems are classified based on the number of independent factors used to verify a user’s identity. increasing the number of factors improves security by reducing reliance on a single credential.
Types Of Authentication Protocols Geeksforgeeks Authentication protocols form the foundation of network security by verifying user identities through various methods and standardized protocols. choosing the appropriate protocol depends on security requirements, infrastructure constraints, and user experience considerations. In this blog post, we introduce the five most commonly used authentication protocols and explain how they work and their benefits. An authentication protocol transfers authentication data between network entities. discover the different types of authentication protocols with okta. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security.
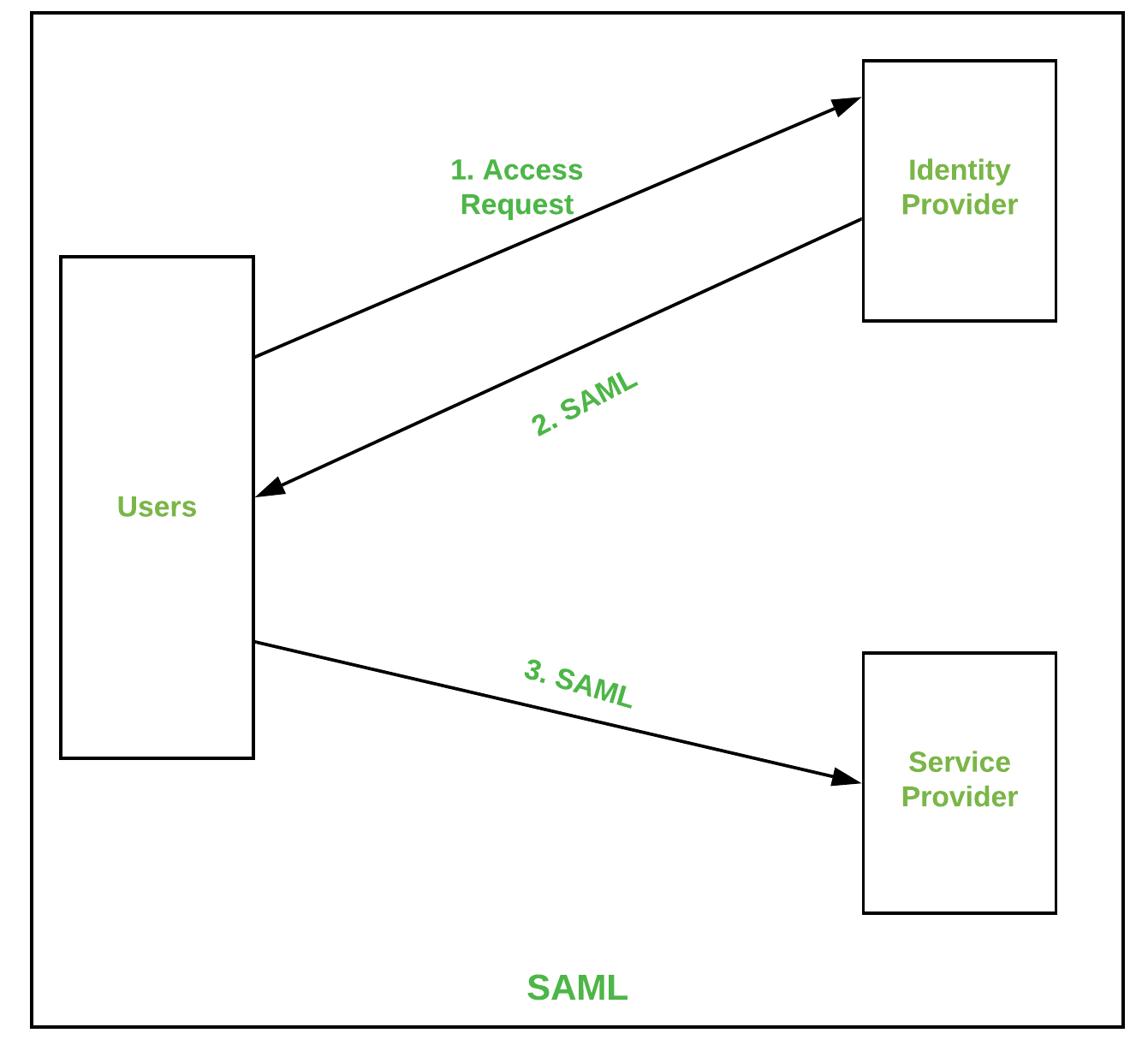
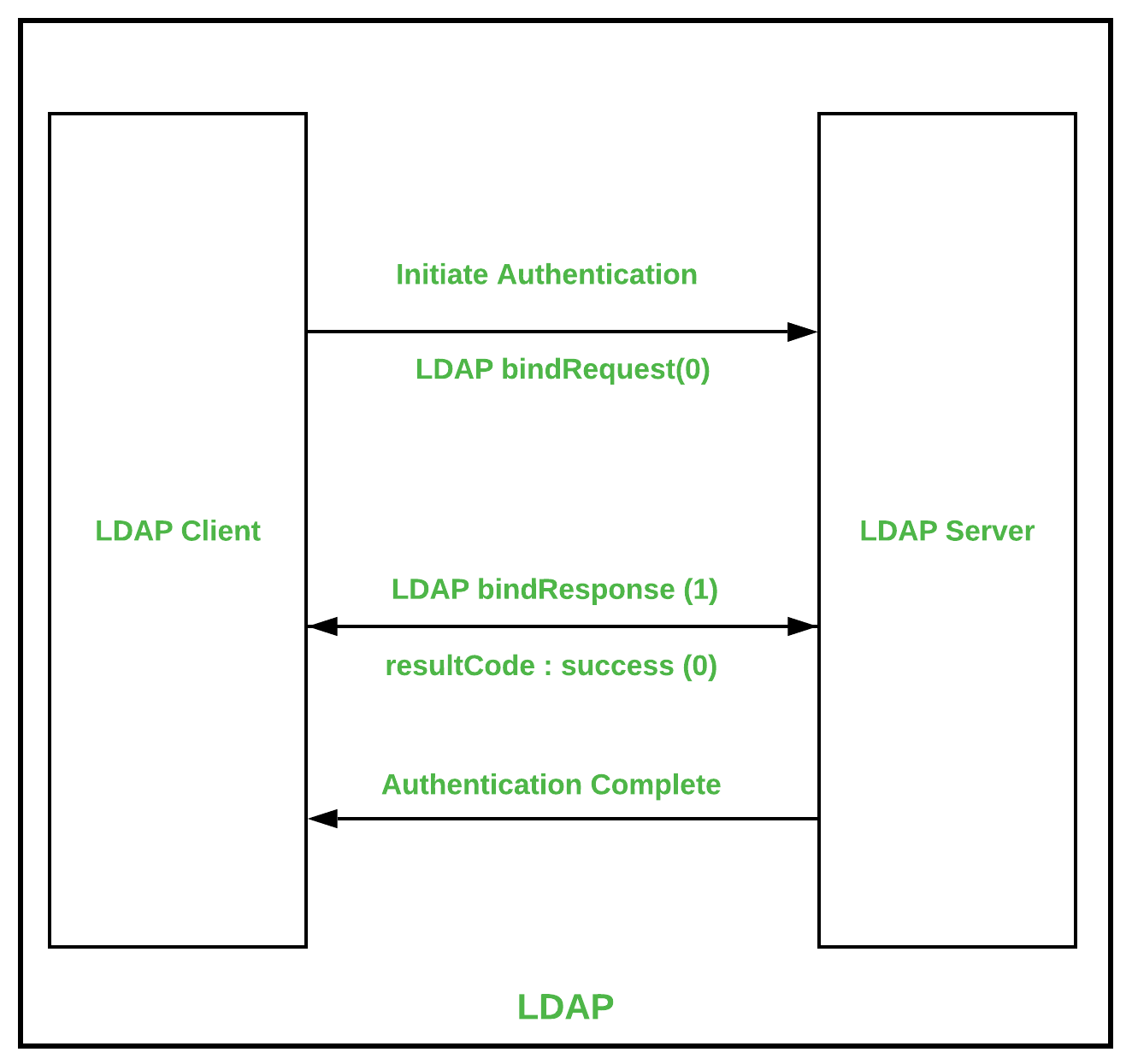
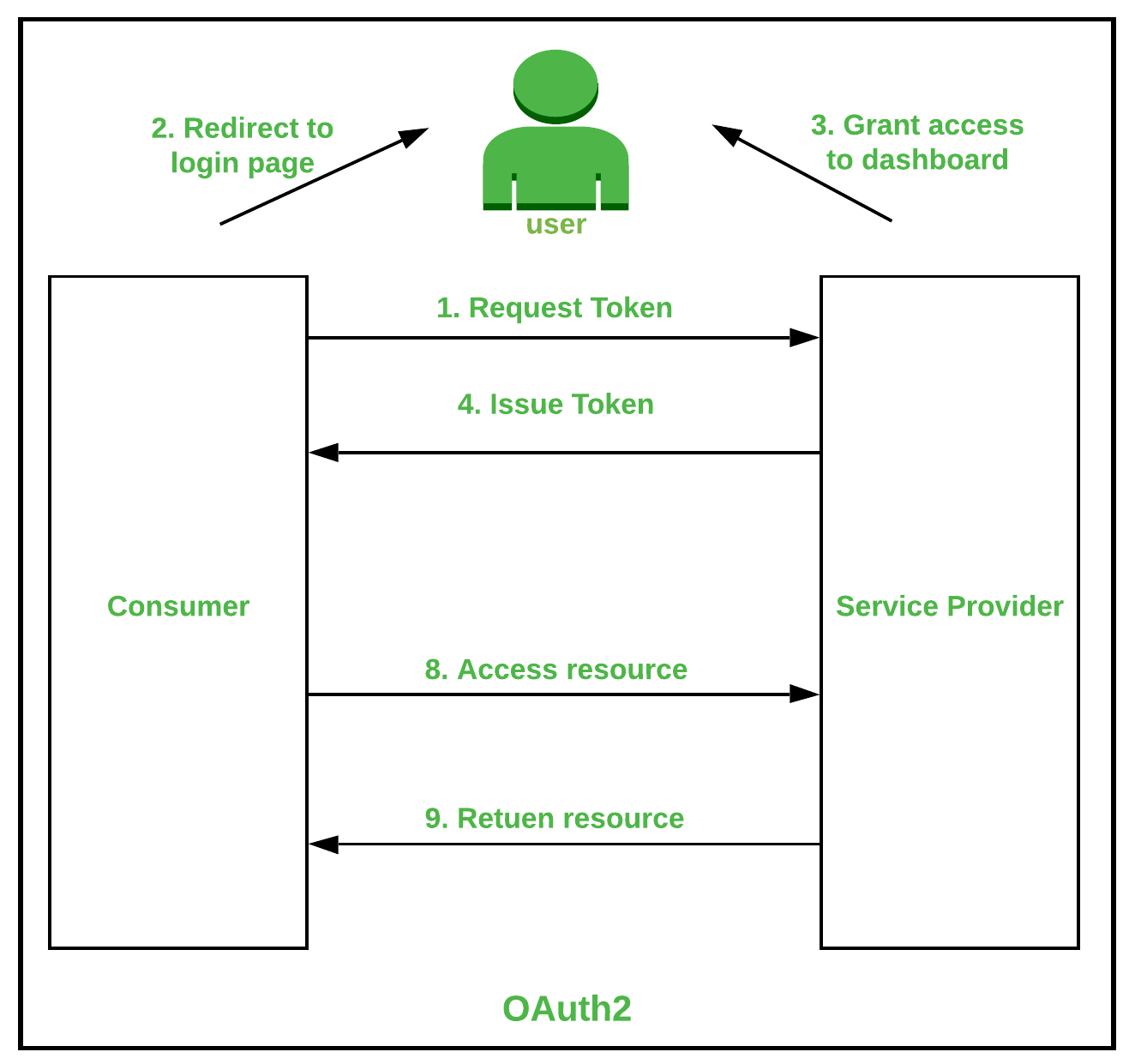
Types Of Authentication Protocols Geeksforgeeks An authentication protocol transfers authentication data between network entities. discover the different types of authentication protocols with okta. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. To authenticate the user there are several mechanisms by which we can authenticate the data that are given by the user. in this article, we are going to learn the most common types of the authentication protocol and their advantages and disadvantages. Network authentication protocols: radius, tacacs the network authentication protocols serve as the backbone of the secure network access which makes sure that only the authorized users or the authorized devices can connect and interact with the network’s resources. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets. Delivers privacy, integrity, and authentication in data transmission using the transport layer security (tls) protocol. encrypts data during transmission. verifies data integrity to detect tampering. authenticates communicating parties. widely used in web applications, email services, and voip. successor and more secure version of ssl.
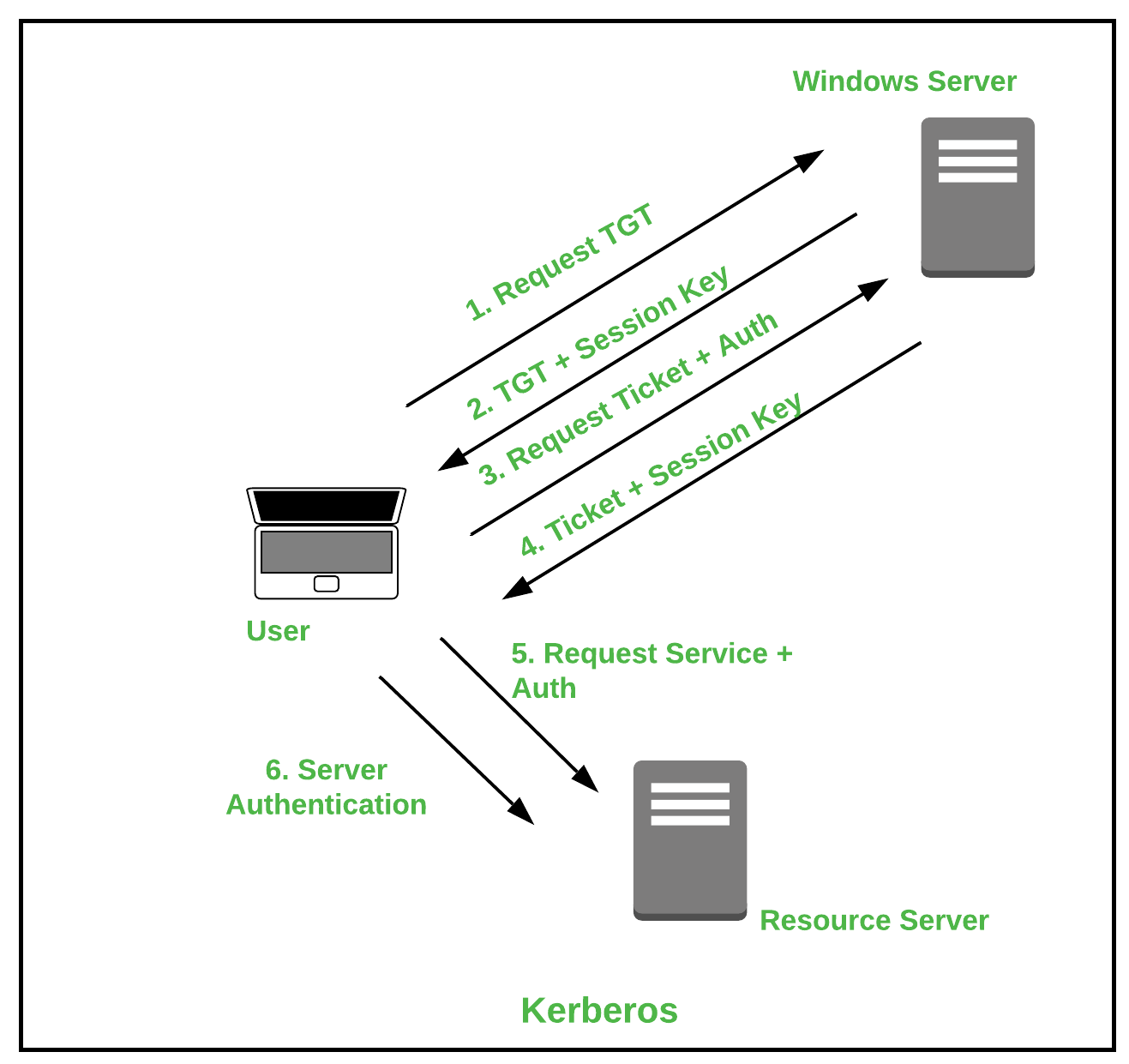
Types Of Authentication Protocols Geeksforgeeks To authenticate the user there are several mechanisms by which we can authenticate the data that are given by the user. in this article, we are going to learn the most common types of the authentication protocol and their advantages and disadvantages. Network authentication protocols: radius, tacacs the network authentication protocols serve as the backbone of the secure network access which makes sure that only the authorized users or the authorized devices can connect and interact with the network’s resources. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets. Delivers privacy, integrity, and authentication in data transmission using the transport layer security (tls) protocol. encrypts data during transmission. verifies data integrity to detect tampering. authenticates communicating parties. widely used in web applications, email services, and voip. successor and more secure version of ssl.
Types Of Authentication Protocols Geeksforgeeks Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets. Delivers privacy, integrity, and authentication in data transmission using the transport layer security (tls) protocol. encrypts data during transmission. verifies data integrity to detect tampering. authenticates communicating parties. widely used in web applications, email services, and voip. successor and more secure version of ssl.
Comments are closed.