Authentication Protocols Types And Uses Adaptive
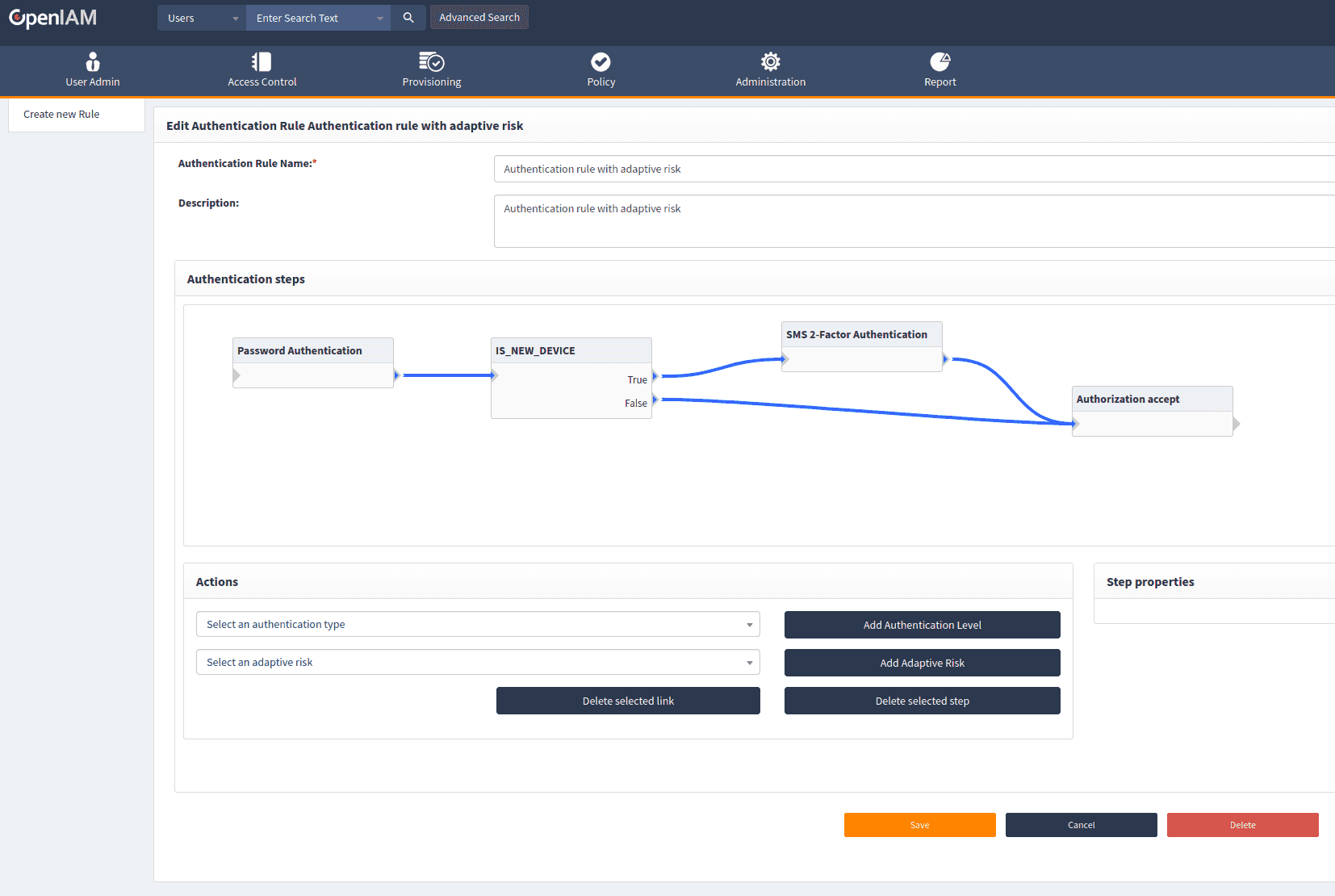
Adaptive Authentication Protocols Types And Uses Authentication protocols define contents of the authentication data, its mode of transfer, and the communication between a server and a client in the network. Traditional authentication is binary—either granting or denying access based on credentials alone—without evaluating contextual risks. in contrast, adaptive authentication applies real time risk assessment to determine whether to grant, challenge, or block access.
301 Moved Permanently In this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. 1. kerberos : kerberos is a protocol that aids in network authentication. this is used for validating clients servers during a network employing a cryptographic key. An authentication protocol transfers authentication data between network entities. discover the different types of authentication protocols with okta. Adaptive authentication use risk based authentication models that adapt to the user's behavior and context multi factor authentication (mfa) require an additional layer of verification for sensitive actions or events challenge based verification prompt users to confirm their identity with a challenge question or secondary method. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security.

Authentication Protocols Types And Uses Adaptive Adaptive authentication use risk based authentication models that adapt to the user's behavior and context multi factor authentication (mfa) require an additional layer of verification for sensitive actions or events challenge based verification prompt users to confirm their identity with a challenge question or secondary method. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. Explore the top authentication protocols, including oauth, saml, oidc, kerberos, and certificate based methods. understand how they improve security. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets. While traditional multi factor authentication (mfa) adds crucial protection, aggressive authentication methods frustrate legitimate users with roadblocks. enter adaptive authentication, which solves this challenge by dynamically adjusting security based on real time risk signals. Explore adaptive authentication strategies, risk based approaches, and implementation techniques. learn how to balance robust security with seamless user experience in modern ciam.
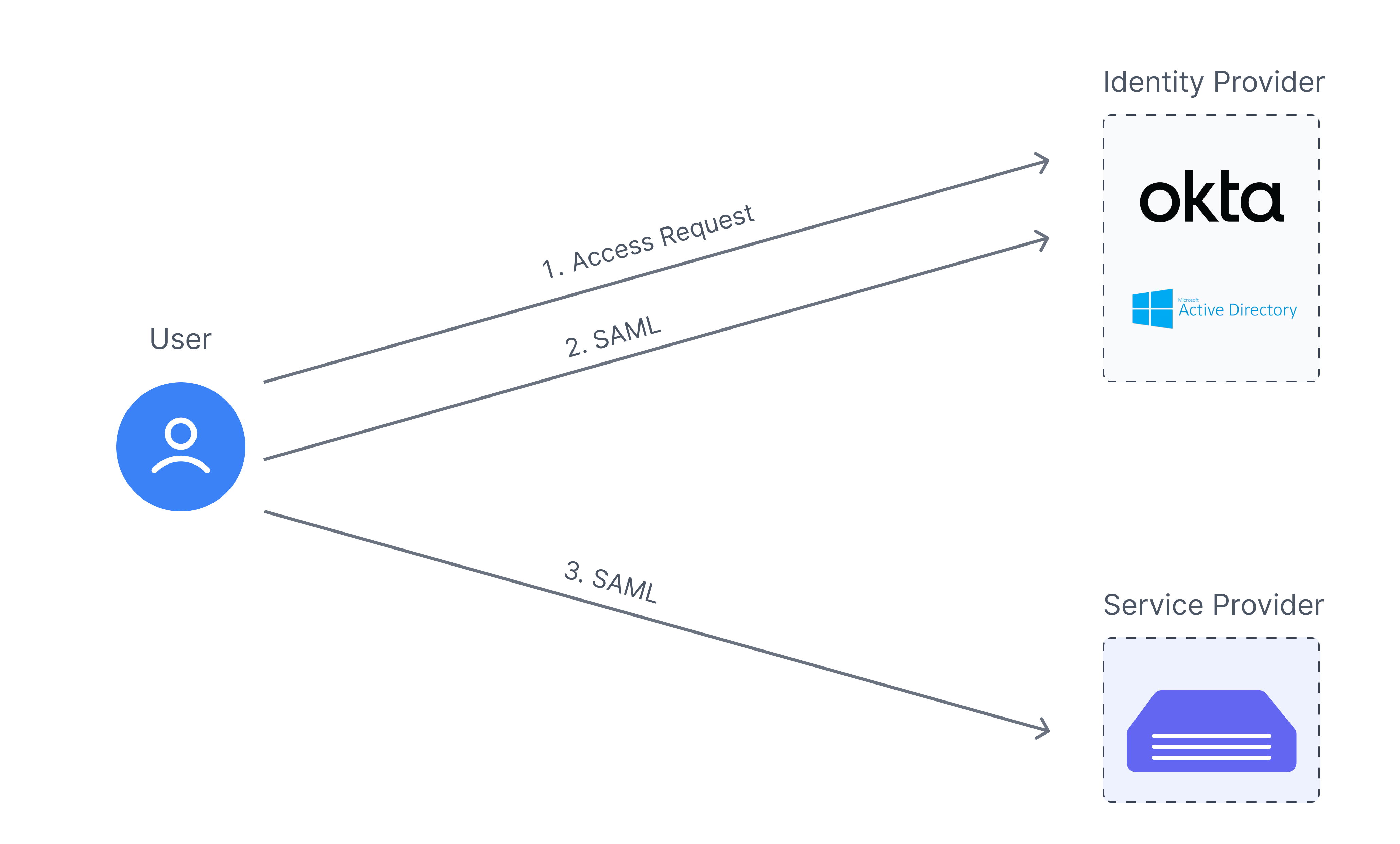
Authentication Protocols Types And Uses Adaptive Explore the top authentication protocols, including oauth, saml, oidc, kerberos, and certificate based methods. understand how they improve security. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets. While traditional multi factor authentication (mfa) adds crucial protection, aggressive authentication methods frustrate legitimate users with roadblocks. enter adaptive authentication, which solves this challenge by dynamically adjusting security based on real time risk signals. Explore adaptive authentication strategies, risk based approaches, and implementation techniques. learn how to balance robust security with seamless user experience in modern ciam.
Comments are closed.