Adaptive Authentication Protocols Types And Uses
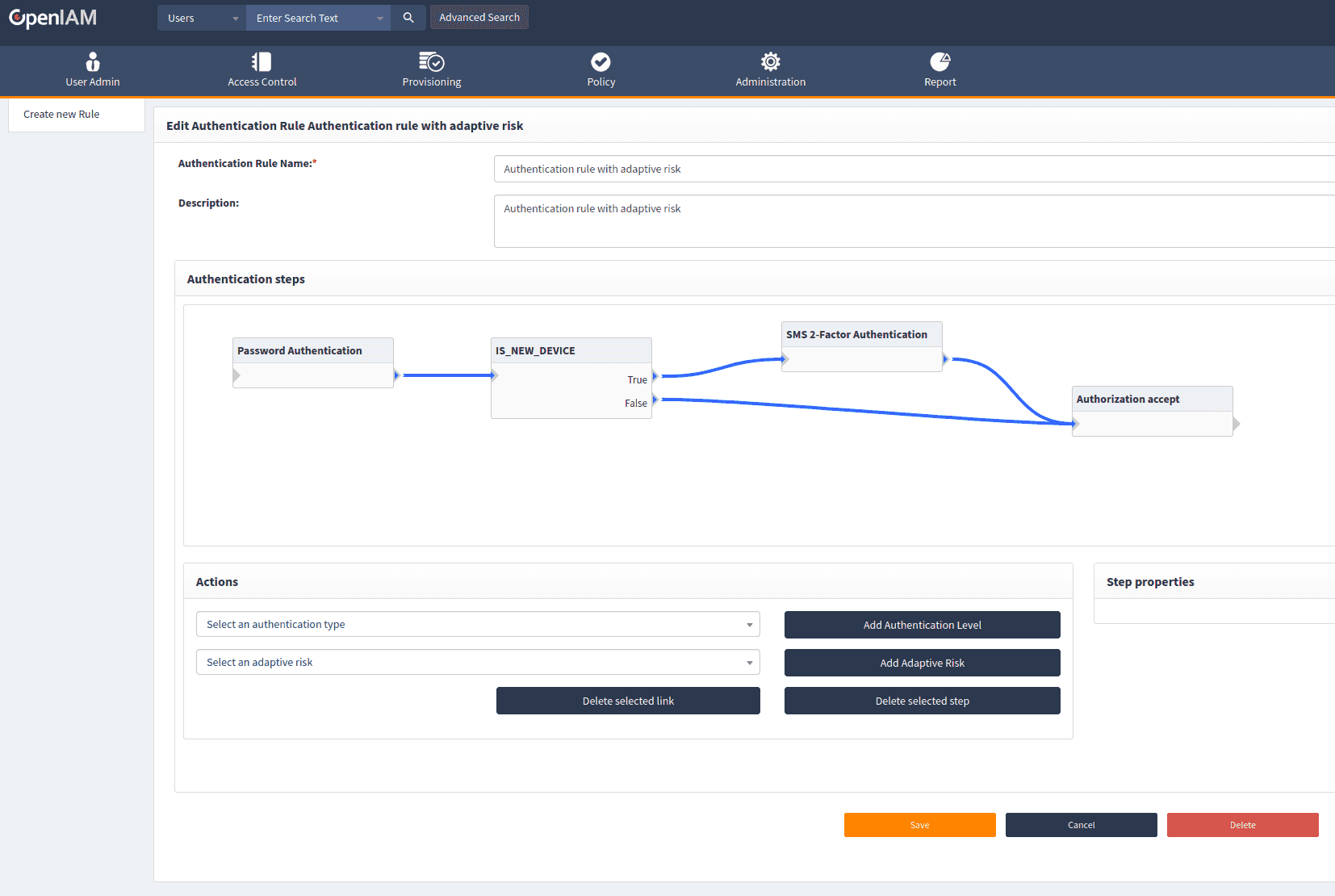
Adaptive Authentication Protocols Types And Uses Traditional authentication is binary—either granting or denying access based on credentials alone—without evaluating contextual risks. in contrast, adaptive authentication applies real time risk assessment to determine whether to grant, challenge, or block access. More formally, authentication protocols define the contents of the authentication data itself, the mode of its transfer, and the communication that must take place between two entities (server and client) in a network.
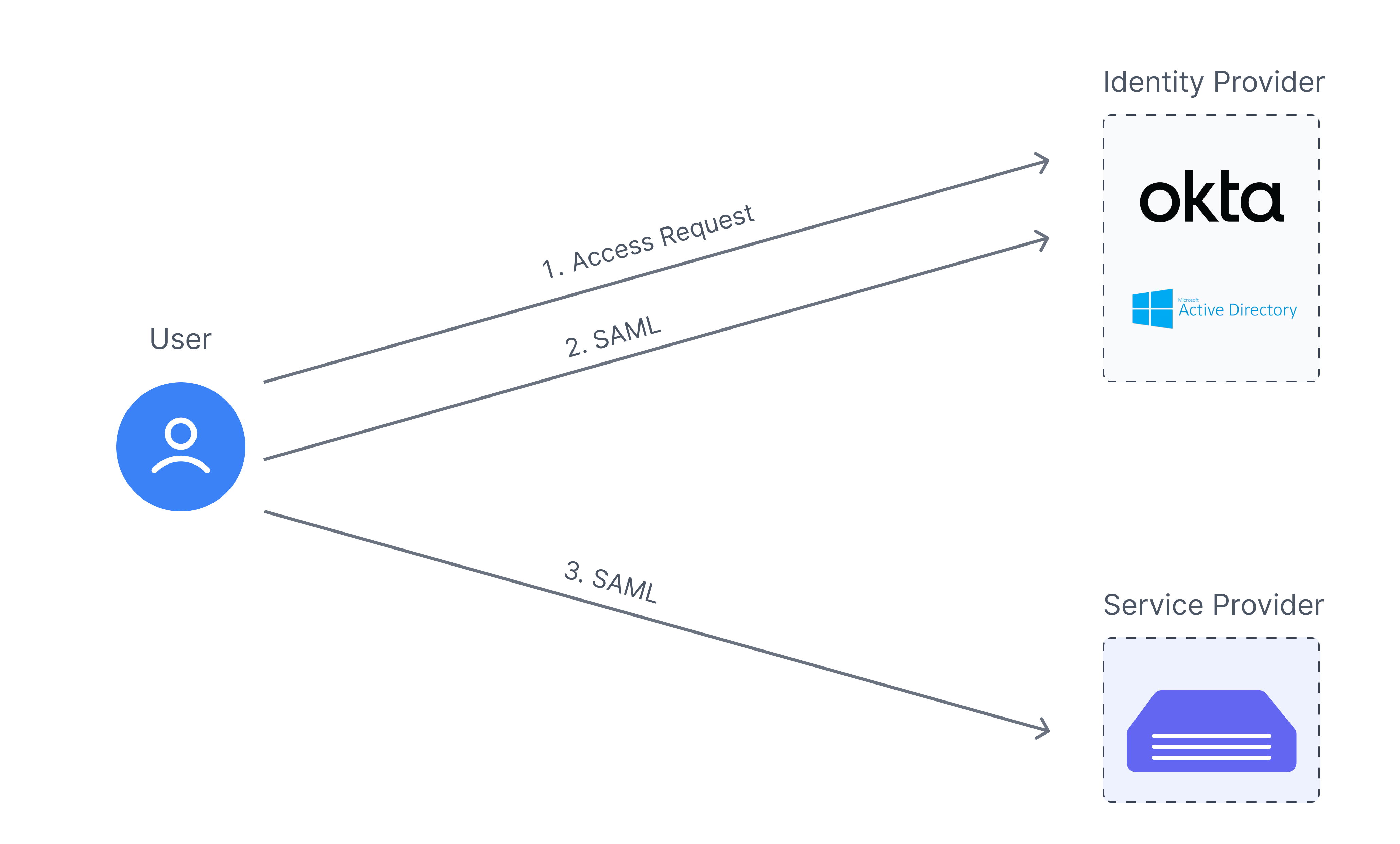
301 Moved Permanently Explore adaptive authentication strategies, risk based approaches, and implementation techniques. learn how to balance robust security with seamless user experience in modern ciam. Learn what adaptive authentication is and how it can improve your online protection. we explain how adaptive auth works and what to look for in vendors. This guide explains how adaptive authentication works, evaluates contextual signals, and enforces appropriate security responses. learn implementation strategies, common use cases, and best practices for deploying risk based authentication across enterprise environments. What are authentication protocols? an authentication protocol allows the receiving party (such as a server) to verify the identity of another party (such as a person using a mobile device to log in).

Authentication Protocols Types And Uses Adaptive This guide explains how adaptive authentication works, evaluates contextual signals, and enforces appropriate security responses. learn implementation strategies, common use cases, and best practices for deploying risk based authentication across enterprise environments. What are authentication protocols? an authentication protocol allows the receiving party (such as a server) to verify the identity of another party (such as a person using a mobile device to log in). Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. By analyzing risk factors and user behavior in real time, adaptive authentication provides an end to end security layer that stays updated and adaptive to emerging threats and changes in user activity. Adaptive authentication systems use multiple technical components that work together to evaluate risk factors and adjust authentication requirements. understanding these components reveals how adaptive systems implement risk based security. While the survey provides an in depth overview of adaptive authentication systems and a discussion on the challenges, it covers a broad range of authentication systems which use a concept of adaptive or context aware features without limiting the scope of authentication factors.
Authentication Protocols Types And Uses Adaptive Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. By analyzing risk factors and user behavior in real time, adaptive authentication provides an end to end security layer that stays updated and adaptive to emerging threats and changes in user activity. Adaptive authentication systems use multiple technical components that work together to evaluate risk factors and adjust authentication requirements. understanding these components reveals how adaptive systems implement risk based security. While the survey provides an in depth overview of adaptive authentication systems and a discussion on the challenges, it covers a broad range of authentication systems which use a concept of adaptive or context aware features without limiting the scope of authentication factors.
Comments are closed.