Types Of Authentication Cryptography And Network Security
User Authentication In Cryptography And Network Security Pptx There are several mechanisms made which are required to authenticate the access while providing access to the data. in this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. These two developments lead to ‘computer security’ and ‘network security’, where the computer security deals with collection of tools designed to protect data and to thwart hackers.
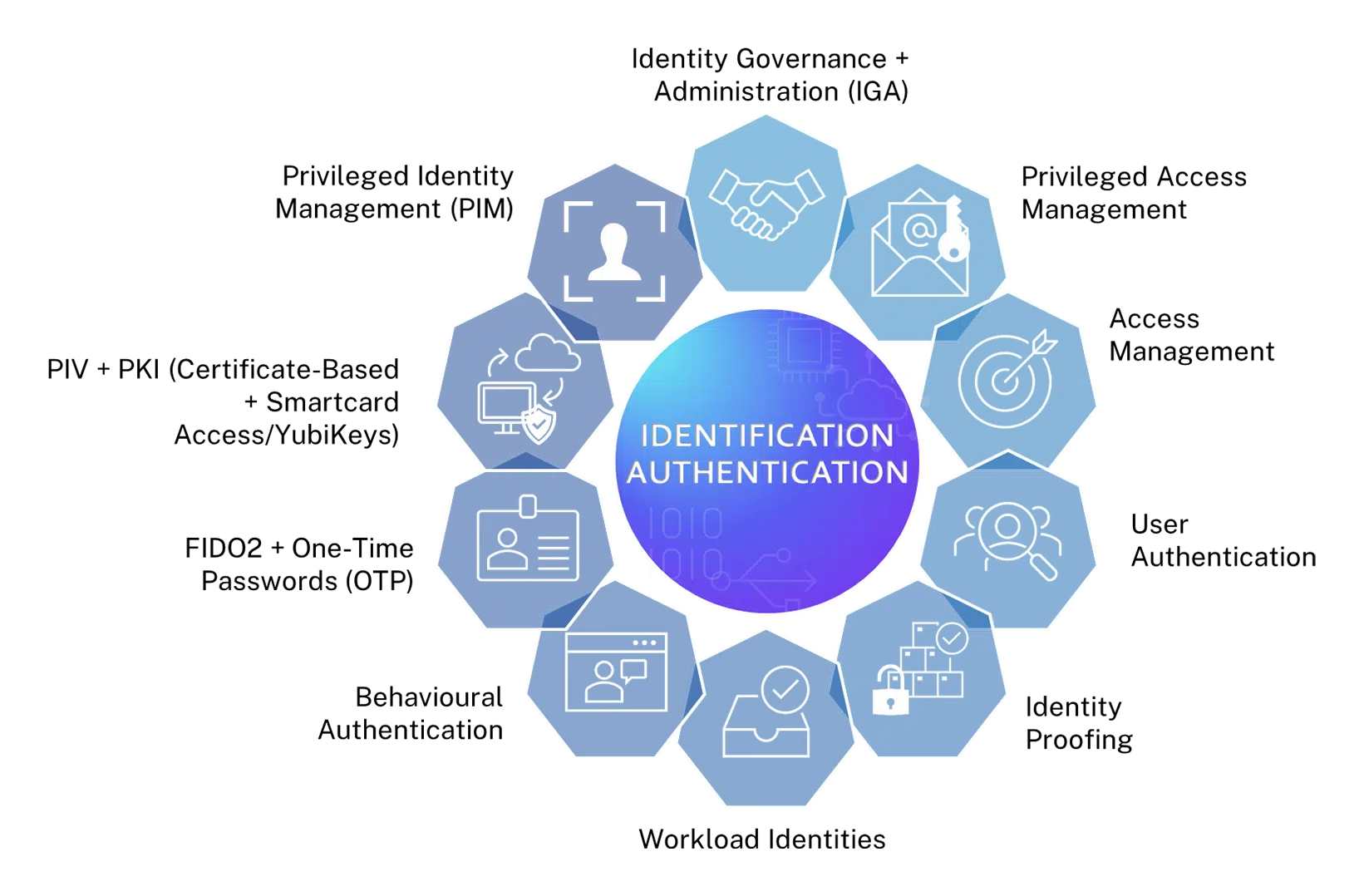
Accutive Security Leading Authentication Cryptography Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. By understanding the different types of authentication protocols, their strengths and weaknesses, and following best practices for implementation, we can ensure the secure authentication of entities and prevent unauthorized access. Authentication protocols form the foundation of network security by verifying user identities through various methods and standardized protocols. choosing the appropriate protocol depends on security requirements, infrastructure constraints, and user experience considerations.

Secure Network Authentication Methods Types And Protocols Nile By understanding the different types of authentication protocols, their strengths and weaknesses, and following best practices for implementation, we can ensure the secure authentication of entities and prevent unauthorized access. Authentication protocols form the foundation of network security by verifying user identities through various methods and standardized protocols. choosing the appropriate protocol depends on security requirements, infrastructure constraints, and user experience considerations. Explore different types of authentication in network security, including passwords, biometrics, and multi factor authentication, to safeguard sensitive data and systems. An assault on system security that derives from an intelligent threat; that is, an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of a system. Chapter 15 of 'cryptography and network security' by william stallings covers user authentication methods, emphasizing the importance of verifying identities via cryptographic keys, passwords, and biometrics. The most commonly used authentication methods in cybersecurity include password based authentication, multi factor authentication (mfa), biometric authentication, and token based authentication.
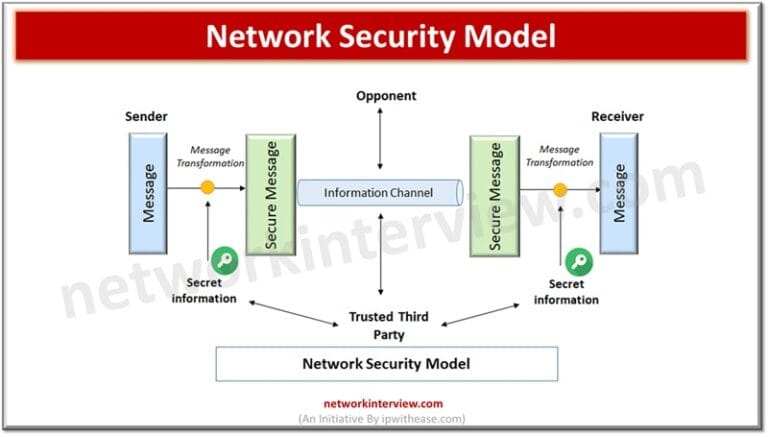
Network Security Model And Cryptography Network Interview Explore different types of authentication in network security, including passwords, biometrics, and multi factor authentication, to safeguard sensitive data and systems. An assault on system security that derives from an intelligent threat; that is, an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of a system. Chapter 15 of 'cryptography and network security' by william stallings covers user authentication methods, emphasizing the importance of verifying identities via cryptographic keys, passwords, and biometrics. The most commonly used authentication methods in cybersecurity include password based authentication, multi factor authentication (mfa), biometric authentication, and token based authentication.

Types Of Authentication Methods Used For Network Security Chapter 15 of 'cryptography and network security' by william stallings covers user authentication methods, emphasizing the importance of verifying identities via cryptographic keys, passwords, and biometrics. The most commonly used authentication methods in cybersecurity include password based authentication, multi factor authentication (mfa), biometric authentication, and token based authentication.
Comments are closed.