Secure Network Authentication Methods Types And Protocols Nile

Secure Network Authentication Methods Types And Protocols Nile Network authentication is a fundamental aspect of network security and can be implemented through various methods such as two factor authentication, biometric authentication, and digital certificates among others. In this article, we learn about what authentication protocol is, the general principles of network authentication protocols, types of authentication protocols, and emerging technologies.
Secure Network Authentication Methods Types And Protocols Nile In this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. 1. kerberos : kerberos is a protocol that aids in network authentication. this is used for validating clients servers during a network employing a cryptographic key. Understanding the main types of authentication protocols gives you a clear view of how identity verification works across different systems. moving forward, let’s explore how modern protocols compare to legacy ones in terms of security and performance. Discover essential network authentication methods, their benefits, and how to enhance your security effectively. Various authentication methods exist, each with its strengths and weaknesses. this article explores popular network authentication methods such as passwords, certificates, and more, providing examples of their real life applications and discussing their pros and cons.

Secure Network Authentication Methods Types And Protocols Nile Discover essential network authentication methods, their benefits, and how to enhance your security effectively. Various authentication methods exist, each with its strengths and weaknesses. this article explores popular network authentication methods such as passwords, certificates, and more, providing examples of their real life applications and discussing their pros and cons. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. There are many authentication methods, ranging from passwords to fingerprints, to confirm the identity of a user before allowing access. This guide explains the main authentication types and factors, shows how modern authentication protocols fit together, and outlines which methods are most secure in 2025. In today's ever evolving cybersecurity landscape, knowing when and how to apply the correct authentication protocol is crucial for optimizing security, usability, and performance.
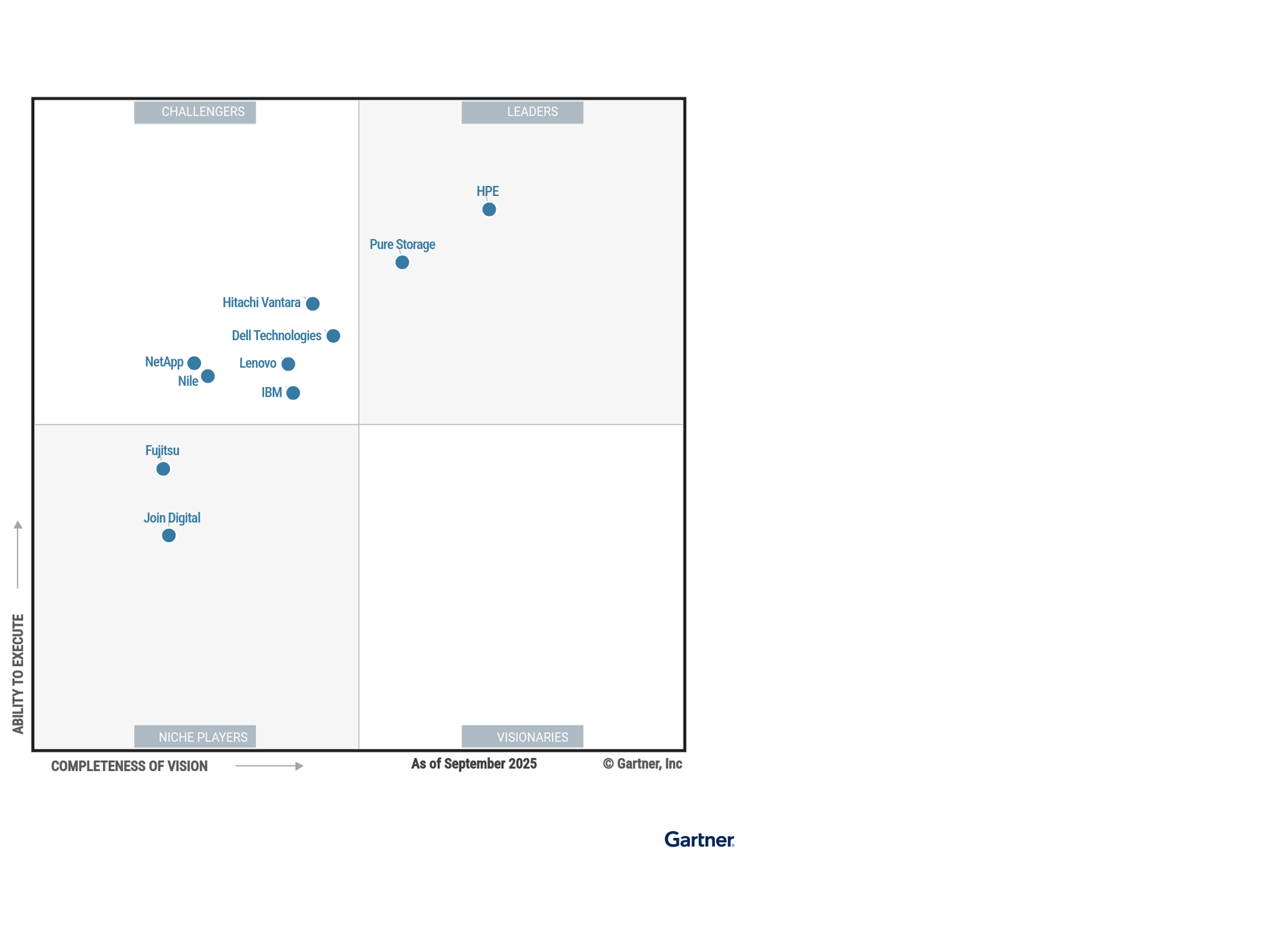
Secure Network Authentication Methods Types And Protocols Nile Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. There are many authentication methods, ranging from passwords to fingerprints, to confirm the identity of a user before allowing access. This guide explains the main authentication types and factors, shows how modern authentication protocols fit together, and outlines which methods are most secure in 2025. In today's ever evolving cybersecurity landscape, knowing when and how to apply the correct authentication protocol is crucial for optimizing security, usability, and performance.

Secure Network Authentication Methods Types And Protocols Nile This guide explains the main authentication types and factors, shows how modern authentication protocols fit together, and outlines which methods are most secure in 2025. In today's ever evolving cybersecurity landscape, knowing when and how to apply the correct authentication protocol is crucial for optimizing security, usability, and performance.
Secure Network Authentication Methods Types And Protocols Nile
Comments are closed.