Side Channel Attack Breaking Rsa Power Analysis
Rsa Side Channel Attack Simulation And Defense Analysis Rsa Py At Main Side channel attacks exploit unintended information leaks—such as power consumption, electromagnetic emissions, or timing variations—to extract sensitive data like cryptographic keys. A comprehensive educational project demonstrating real world cryptographic side channel attacks and quantum cryptanalysis techniques. this simulator includes interactive demonstrations of power analysis attacks, kleptographic vulnerabilities, and quantum computing threats to rsa encryption.
Power Analysis Based Side Channel Attack Deepai In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. In this work we propose two algorithms that defeat side channel attacks: paired permutation exponentiation (ppe) and permute, split, and accumulate (psa). we compare these two algorithms with the classic right to left technique. In this article i will explore various attacks and weaknesses of rsa implementations documented in literature. in general, the class of side channel attacks consists of attacks which do. Explore side channel attacks, including power and timing analysis, how they exploit cryptographic systems, and effective countermeasures to secure hardware implementations.
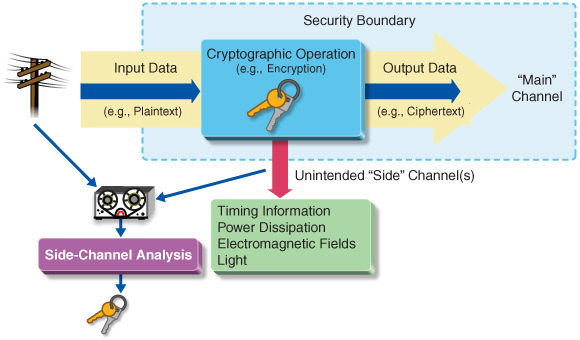
Power Analysis Based Side Channel Attack Deepai In this article i will explore various attacks and weaknesses of rsa implementations documented in literature. in general, the class of side channel attacks consists of attacks which do. Explore side channel attacks, including power and timing analysis, how they exploit cryptographic systems, and effective countermeasures to secure hardware implementations. Side channel analysis in the context of power analysis can reveal a lot of information and even leak the private key from the processors and has a lot of potential for research in hardware related attacks. In this work, we tackle the use of machine learning methods to perform a power consumption based side channel attack against asymmetric cryptosystems. The montgomery powering ladder exponentiation is adopted in order to protect against simple side channel analysis. we show that collision based attacks remain efficient against an rsa rns. Luckily, there is no need to dive too much into the mathematics to crack rsa using simple power analysis. in the chapter on aes, we will go a bit deeper into cache based power analysis attacks, why they work exactly and how to perform them on the chipwhisperer.
Correlation Power Analysis Cpa Based Power Side Channel Attack Side channel analysis in the context of power analysis can reveal a lot of information and even leak the private key from the processors and has a lot of potential for research in hardware related attacks. In this work, we tackle the use of machine learning methods to perform a power consumption based side channel attack against asymmetric cryptosystems. The montgomery powering ladder exponentiation is adopted in order to protect against simple side channel analysis. we show that collision based attacks remain efficient against an rsa rns. Luckily, there is no need to dive too much into the mathematics to crack rsa using simple power analysis. in the chapter on aes, we will go a bit deeper into cache based power analysis attacks, why they work exactly and how to perform them on the chipwhisperer.

Figure1 Side Channel Power Analysis Attack Download Scientific Diagram The montgomery powering ladder exponentiation is adopted in order to protect against simple side channel analysis. we show that collision based attacks remain efficient against an rsa rns. Luckily, there is no need to dive too much into the mathematics to crack rsa using simple power analysis. in the chapter on aes, we will go a bit deeper into cache based power analysis attacks, why they work exactly and how to perform them on the chipwhisperer.

The Side Channel Power Attack Process Based On Sa Svm The Side Channel
Comments are closed.