Side Channel Attack On Rsa Implementation

Tag Side Channel Attack Ars Technica In this article i will explore various attacks and weaknesses of rsa implementations documented in literature. in general, the class of side channel attacks consists of attacks which do. In this section we explain how we modified the rsa algorithm to effectively defeat side channel attacks as we make use of the commutative and distributive properties of the exponentiation operation.

Tag Side Channel Attack Ars Technica Abstract: profiling attack based on smaller and deeper neural network vggnet is performed on a smart card crt rsa implementation. crt rsa implementation uses security countermeasures including masking and time jittering. This paper reviews cache based software side channel attacks, mitigation and detection techniques that target various cryptosystems, particularly rsa, proposed over the last decade (2007–2018). Several side channel attacks have been presented on the implementation of rsa. the two main implementation approaches of rsa are rsa base and rsa crt (chinese remainder theorem). The marvin attack is a new side channel attack on cryptographic implementations of rsa in which the attacker decrypts previously captured ciphertext by measuring, over a network, server response times to specially crafted messages.
Mitigating A Token Length Side Channel Attack In Our Ai Products Several side channel attacks have been presented on the implementation of rsa. the two main implementation approaches of rsa are rsa base and rsa crt (chinese remainder theorem). The marvin attack is a new side channel attack on cryptographic implementations of rsa in which the attacker decrypts previously captured ciphertext by measuring, over a network, server response times to specially crafted messages. Side channel attacks, such as power analysis, exploit information leaked during the execution of cryptographic algorithms. power consumption during different operations can reveal patterns. A timing side channel attack on a rsa key. contribute to groggero95 tsca development by creating an account on github. This was a review of the different styles of successful side channel attacks against rsa looked through the different research papers, how they managed to become into exis tence and how these attacks were dwarfed with new and improved defences. Specifically, it provides guidance to implementers of the standard to protect against side channel attacks. it also deprecates the rsaes pkcs v1 5 encryption scheme, but provides an alternative depadding algorithm that protects against side channel attacks raising from users of vulnerable apis.
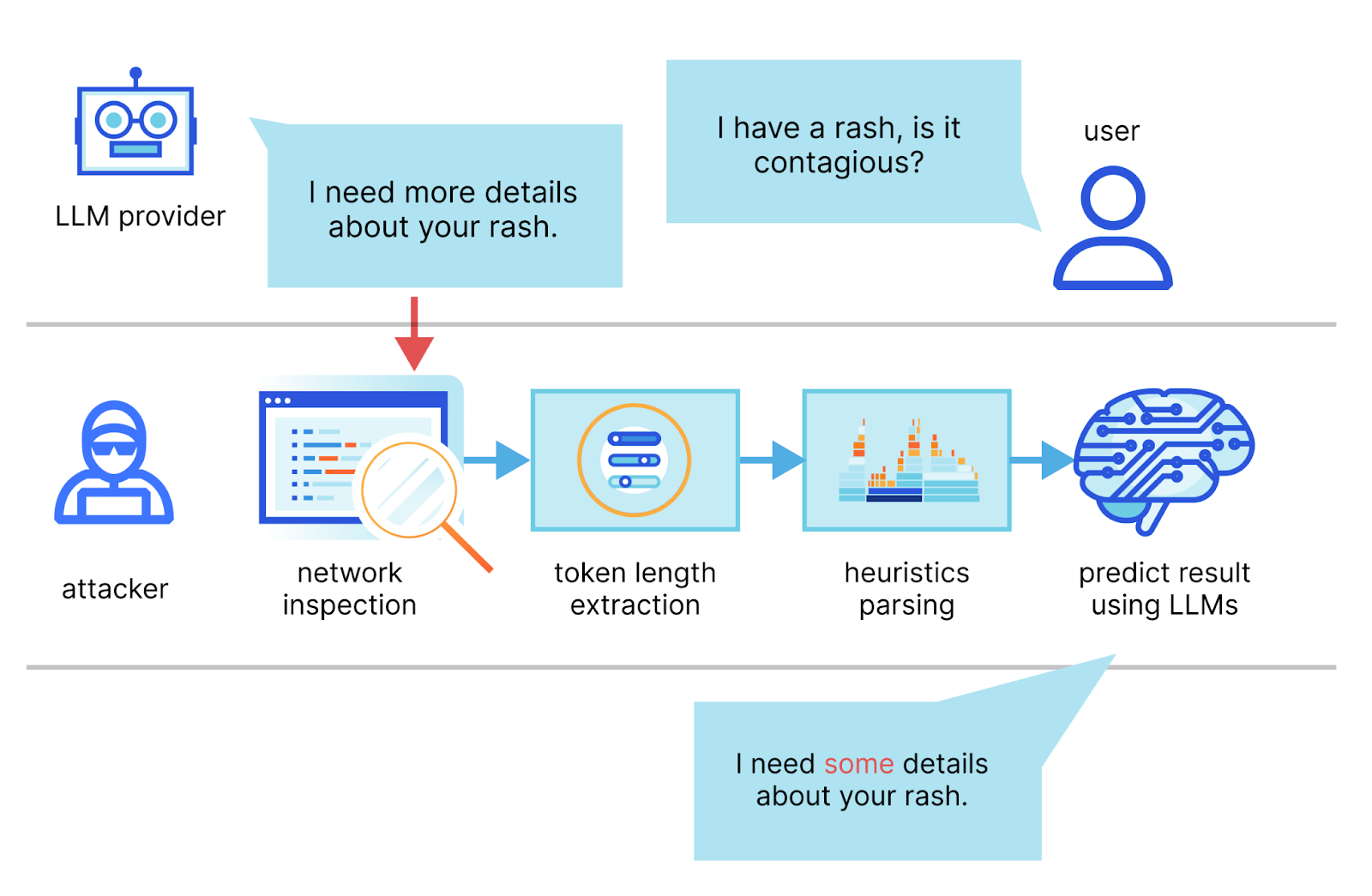
Mitigating A Token Length Side Channel Attack In Our Ai Products Side channel attacks, such as power analysis, exploit information leaked during the execution of cryptographic algorithms. power consumption during different operations can reveal patterns. A timing side channel attack on a rsa key. contribute to groggero95 tsca development by creating an account on github. This was a review of the different styles of successful side channel attacks against rsa looked through the different research papers, how they managed to become into exis tence and how these attacks were dwarfed with new and improved defences. Specifically, it provides guidance to implementers of the standard to protect against side channel attacks. it also deprecates the rsaes pkcs v1 5 encryption scheme, but provides an alternative depadding algorithm that protects against side channel attacks raising from users of vulnerable apis.

Side Channel Attacks Explained All You Need To Know Rambus This was a review of the different styles of successful side channel attacks against rsa looked through the different research papers, how they managed to become into exis tence and how these attacks were dwarfed with new and improved defences. Specifically, it provides guidance to implementers of the standard to protect against side channel attacks. it also deprecates the rsaes pkcs v1 5 encryption scheme, but provides an alternative depadding algorithm that protects against side channel attacks raising from users of vulnerable apis.
Comments are closed.