Defence Against Side Channel Attacks For Encrypted Network
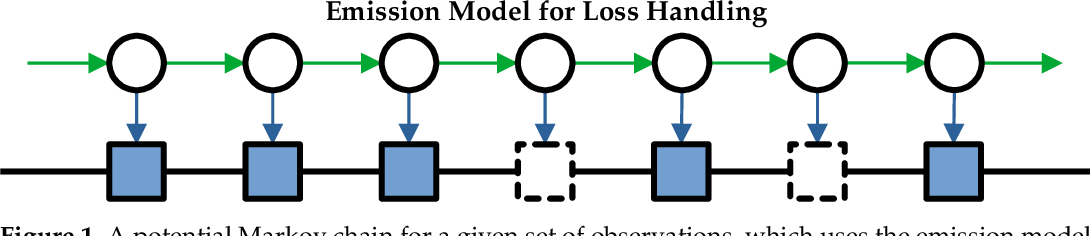
Figure 1 From Defence Against Side Channel Attacks For Encrypted In this paper, we argue that multipath communication can act as a defence against traffic analysis attacks based on side channels. As more network communication is encrypted to provide data privacy for users, attackers are focusing their attention on traffic analysis methods for side channel attacks on user privacy.

Pdf Defence Against Side Channel Attacks For Encrypted Network As more network communication is encrypted to provide data privacy for users, attackers are focussing their attention on traffic analysis methods for side channel attacks on user privacy. This paper proposes a novel defense mechanism using a per burst injection technique, called deep fingerprinting defender (dfd), against deep learning based wf attacks, and demonstrates that dfd outperforms the state of the art alternatives by requiring lower bandwidth overhead. The proposed hybrid cryptographic framework is designed to address a range of side channel attacks (sca) and cryptanalysis based threats. Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies.

Securing Against Compression Side Channel Attacks The proposed hybrid cryptographic framework is designed to address a range of side channel attacks (sca) and cryptanalysis based threats. Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies. In this paper, we present a side channel resilient moving target defense mechanism against power electromagnetic based side channel attacks. recent countermeasures use fresh rekeying after every encryption decryption process; this causes major overhead in synchronizing the communicating parties. Outline what are side channel attacks (scas)? which adversary models are suitable for scas? which types of attacks exists? how do these attacks work precisely?. The increasing sophistication of side channel attacks (scas) poses a critical threat to the security of cryptographic systems, necessitating the development of effective defense mechanisms. In this blog post, we'll define what side channel attacks are, explore their various types, discuss defense strategies, and offer an outlook on their evolving role in cybersecurity.
Side Channel Attacks Ppt In this paper, we present a side channel resilient moving target defense mechanism against power electromagnetic based side channel attacks. recent countermeasures use fresh rekeying after every encryption decryption process; this causes major overhead in synchronizing the communicating parties. Outline what are side channel attacks (scas)? which adversary models are suitable for scas? which types of attacks exists? how do these attacks work precisely?. The increasing sophistication of side channel attacks (scas) poses a critical threat to the security of cryptographic systems, necessitating the development of effective defense mechanisms. In this blog post, we'll define what side channel attacks are, explore their various types, discuss defense strategies, and offer an outlook on their evolving role in cybersecurity.

Side Channel Attacks On Hsms Threats Defences Cyber Snowden The increasing sophistication of side channel attacks (scas) poses a critical threat to the security of cryptographic systems, necessitating the development of effective defense mechanisms. In this blog post, we'll define what side channel attacks are, explore their various types, discuss defense strategies, and offer an outlook on their evolving role in cybersecurity.
Comments are closed.