Rsa Power Analysis Side Channel Attack Rhme2
Power Analysis Based Side Channel Attack Deepai Preparing an arduino nano board to perform a power analysis side channel attack and explaining how that can be used to break rsa. also proof i can't count. more. Although rsa is computationally secure, its implementation using bit serial modular exponentiation is slow and can introduce vulnerabilities to side channel attacks such as timing or power analysis.
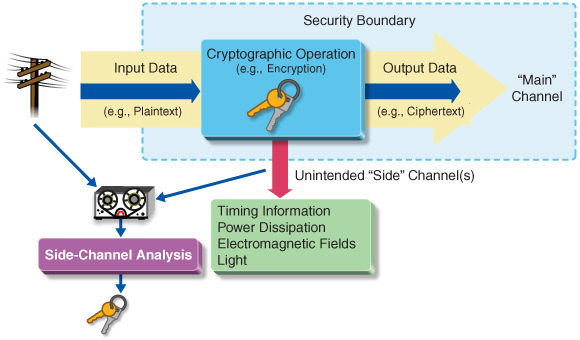
Power Analysis Based Side Channel Attack Deepai A comprehensive educational project demonstrating real world cryptographic side channel attacks and quantum cryptanalysis techniques. this simulator includes interactive demonstrations of power analysis attacks, kleptographic vulnerabilities, and quantum computing threats to rsa encryption. Feeling disappointed with my work i found out that my language can't handle a certain level of complexity because it's too slow, and now i feel pretty demotivated. r archlinux •. Introduction: side channel attacks exploit unintended information leaks—such as power consumption, electromagnetic emissions, or timing variations—to extract sensitive data like cryptographic keys. In this work, we tackle the use of machine learning methods to perform a power consumption based side channel attack against asymmetric cryptosystems.

The Side Channel Power Attack Process Based On Sa Svm The Side Channel Introduction: side channel attacks exploit unintended information leaks—such as power consumption, electromagnetic emissions, or timing variations—to extract sensitive data like cryptographic keys. In this work, we tackle the use of machine learning methods to perform a power consumption based side channel attack against asymmetric cryptosystems. In this article i will explore various attacks and weaknesses of rsa implementations documented in literature. in general, the class of side channel attacks consists of attacks which do. Rsa power analysis side channel attack rhme2 liveoverflow • 55k views • 8 years ago. The montgomery powering ladder exponentiation is adopted in order to protect against simple side channel analysis. we show that collision based attacks remain efficient against an rsa rns. Technology rsa power analysis side channel attack rhme2 (3 replies).

The Side Channel Power Attack Process Based On Sa Svm The Side Channel In this article i will explore various attacks and weaknesses of rsa implementations documented in literature. in general, the class of side channel attacks consists of attacks which do. Rsa power analysis side channel attack rhme2 liveoverflow • 55k views • 8 years ago. The montgomery powering ladder exponentiation is adopted in order to protect against simple side channel analysis. we show that collision based attacks remain efficient against an rsa rns. Technology rsa power analysis side channel attack rhme2 (3 replies).
Comments are closed.