Rsa Algorithm Part 2
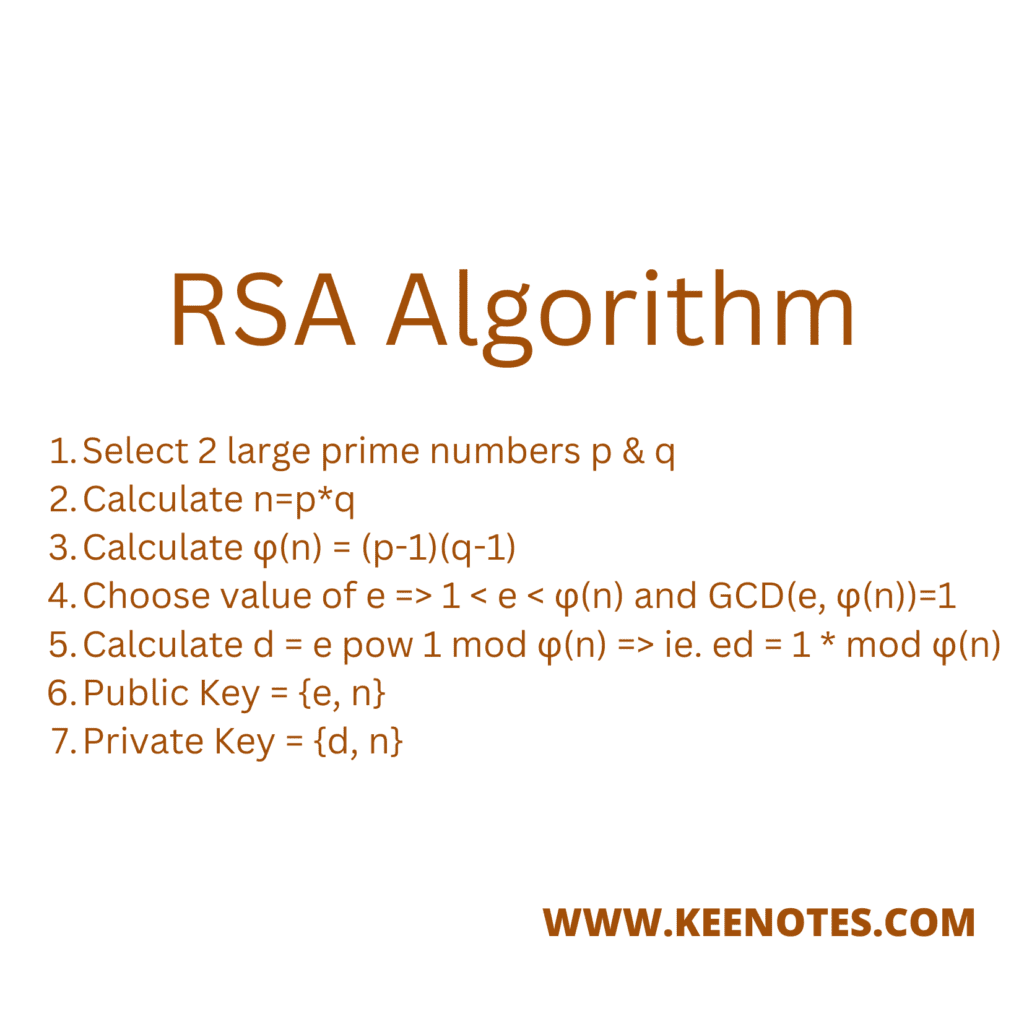
Rsa Algorithm Key Notes Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data. 12.2.1 the rsa algorithm — putting to use the basic idea the basic idea described in the previous subsection can be used to create a confidential communication channel in the manner described here.
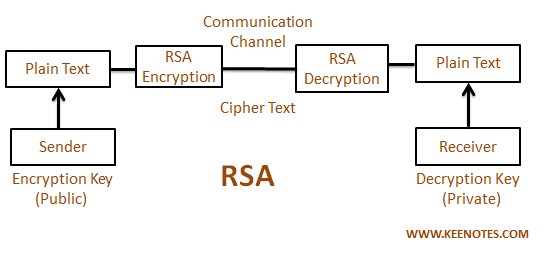
Rsa Algorithm Key Notes Rsa provides security using the mathematical concept that it is much more difficult to factor a number than to multiply two large numbers together. rsa uses two keys – a public key and a private key. rsa can be used for digital signatures and for encryption of data. This is the rsa algorithm part 2 encryption and decryptionthis will cover the mathematical process of encrypting and decrypting a message using rsa algorit. Fakta inilah yang membuat algoritma rsa dianggap masih aman untuk saat ini. semakin panjang bilangan bulatnya, maka semakin lama waktu yang dibutuhkan untuk memfaktorkannya. The paper is organized as follows: the necessary foundational information of the rsa algorithm is provided in section 2. then the detailed onion peeling style introduction of the algorithm is elaborated in section 3.

Rsa Algorithm Ppt Fakta inilah yang membuat algoritma rsa dianggap masih aman untuk saat ini. semakin panjang bilangan bulatnya, maka semakin lama waktu yang dibutuhkan untuk memfaktorkannya. The paper is organized as follows: the necessary foundational information of the rsa algorithm is provided in section 2. then the detailed onion peeling style introduction of the algorithm is elaborated in section 3. Industrial quality rsa works with enormous prime numbers consisting of hundreds of digits. to keep our explanations sim ple, we’re going to use only small prime numbers in our explanations. such small prime number rsa versions are not secure, but they’ll help you understand how rsa works. Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. This paper focuses on the mathematics behind the algorithm, along with its core functionality and implementation. in addition, the code implementation and the encryption and decryption procedure. Lecture notes: cryptography part 2: public key cryptography: the rsa algorithm.
Comments are closed.