Cryptography 2 Rsa

Rsa Cryptography By Wentz Wu Issap Issep Issmp Cissp Ccsp Csslp Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data. 12.2.1 the rsa algorithm — putting to use the basic idea the basic idea described in the previous subsection can be used to create a confidential communication channel in the manner described here.

Nobita69 Rsa Cryptography Tool At Main Hu abstract. in the field of cryptography, which aims to ensure secure message communica tion, the rsa public key cryptosystem is the oldest widely applied secure data transmi. sion method. in this expository paper, we provide a historical and technical overview of the rsa . Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Cryptography (how we keep messages secure) uses mathematics and prime numbers in particular. in essence it is a lot easier to multiply primes together than to work out what primes were multiplied to make a number. example: what is 101 × 131? after a short while we can get the answer of 13231.
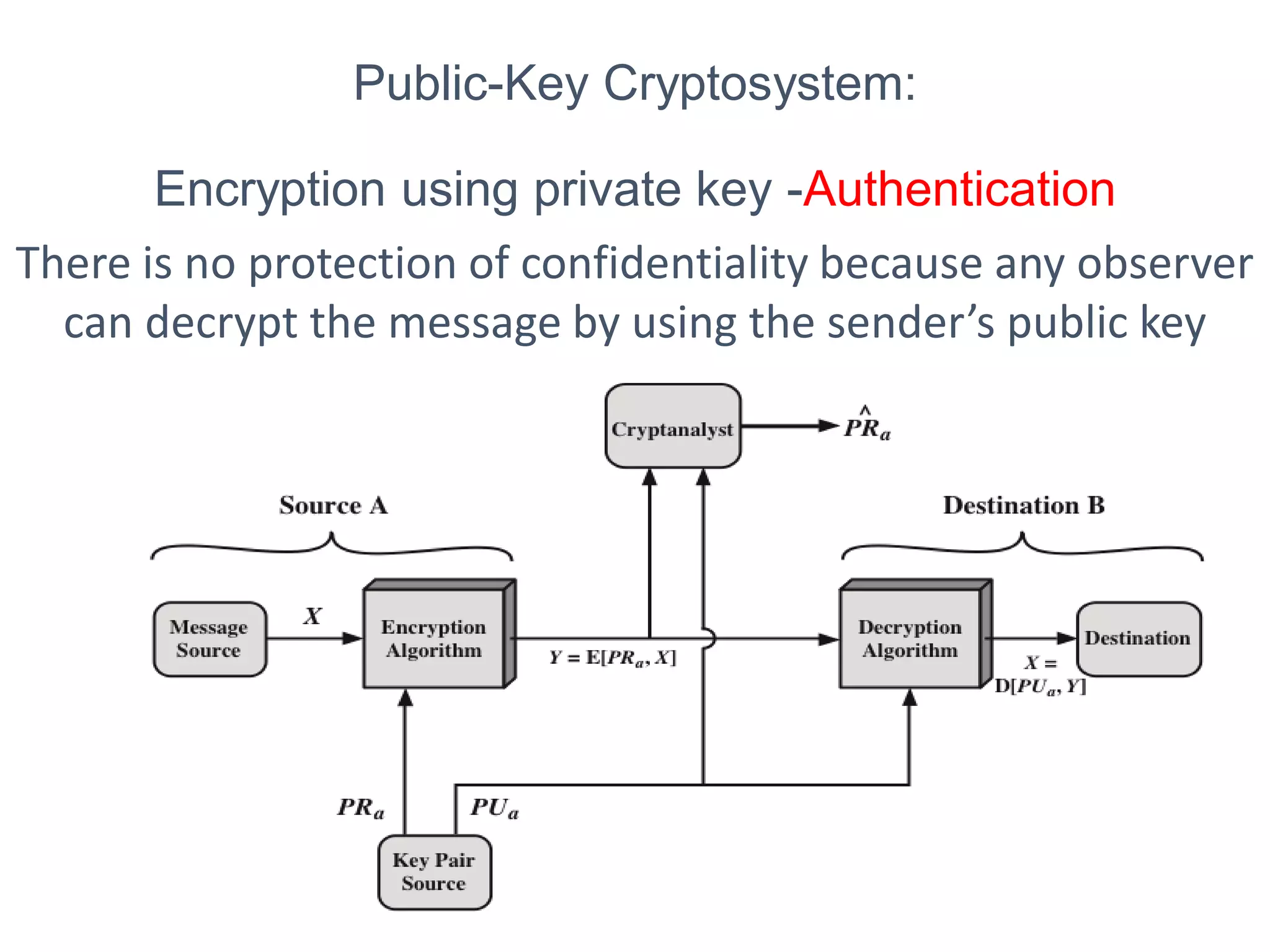
2 Public Key Cryptography And Rsa Pdf Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Cryptography (how we keep messages secure) uses mathematics and prime numbers in particular. in essence it is a lot easier to multiply primes together than to work out what primes were multiplied to make a number. example: what is 101 × 131? after a short while we can get the answer of 13231. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Rsa is an encryption algorithm, used to securely transmit messages over the internet. it is based on the principle that it is easy to multiply large numbers, but factoring large numbers is very difficult. Rsa is an example of a public key cryptosystem, and these are widely used today. all of these are characterized by an encryption function e: x ! x that is easy to compute but almost impossible to invert, unless you have the \secret key". unlike the methods in the previous lecture, public key systems are asymmetric cryptosystems. What is the rsa algorithm? the rsa algorithm is an asymmetric cryptographic algorithm, which means it uses two different keys: a public key for encryption and a private key for decryption.
Rsa Algorithm Secure Your Data With Public Key Encryption The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Rsa is an encryption algorithm, used to securely transmit messages over the internet. it is based on the principle that it is easy to multiply large numbers, but factoring large numbers is very difficult. Rsa is an example of a public key cryptosystem, and these are widely used today. all of these are characterized by an encryption function e: x ! x that is easy to compute but almost impossible to invert, unless you have the \secret key". unlike the methods in the previous lecture, public key systems are asymmetric cryptosystems. What is the rsa algorithm? the rsa algorithm is an asymmetric cryptographic algorithm, which means it uses two different keys: a public key for encryption and a private key for decryption.

2 Public Key Cryptography And Rsa Pdf Rsa is an example of a public key cryptosystem, and these are widely used today. all of these are characterized by an encryption function e: x ! x that is easy to compute but almost impossible to invert, unless you have the \secret key". unlike the methods in the previous lecture, public key systems are asymmetric cryptosystems. What is the rsa algorithm? the rsa algorithm is an asymmetric cryptographic algorithm, which means it uses two different keys: a public key for encryption and a private key for decryption.
Rsa Algorithm Public Key Cryptography Ppt
Comments are closed.