Rsa Algorithm
Rsa Algorithm Key Notes The rsa algorithm involves four steps: key generation, key distribution, public key operation (used for encryption or verifying a signature), and private key operation (used for decryption or signing a message). Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key.

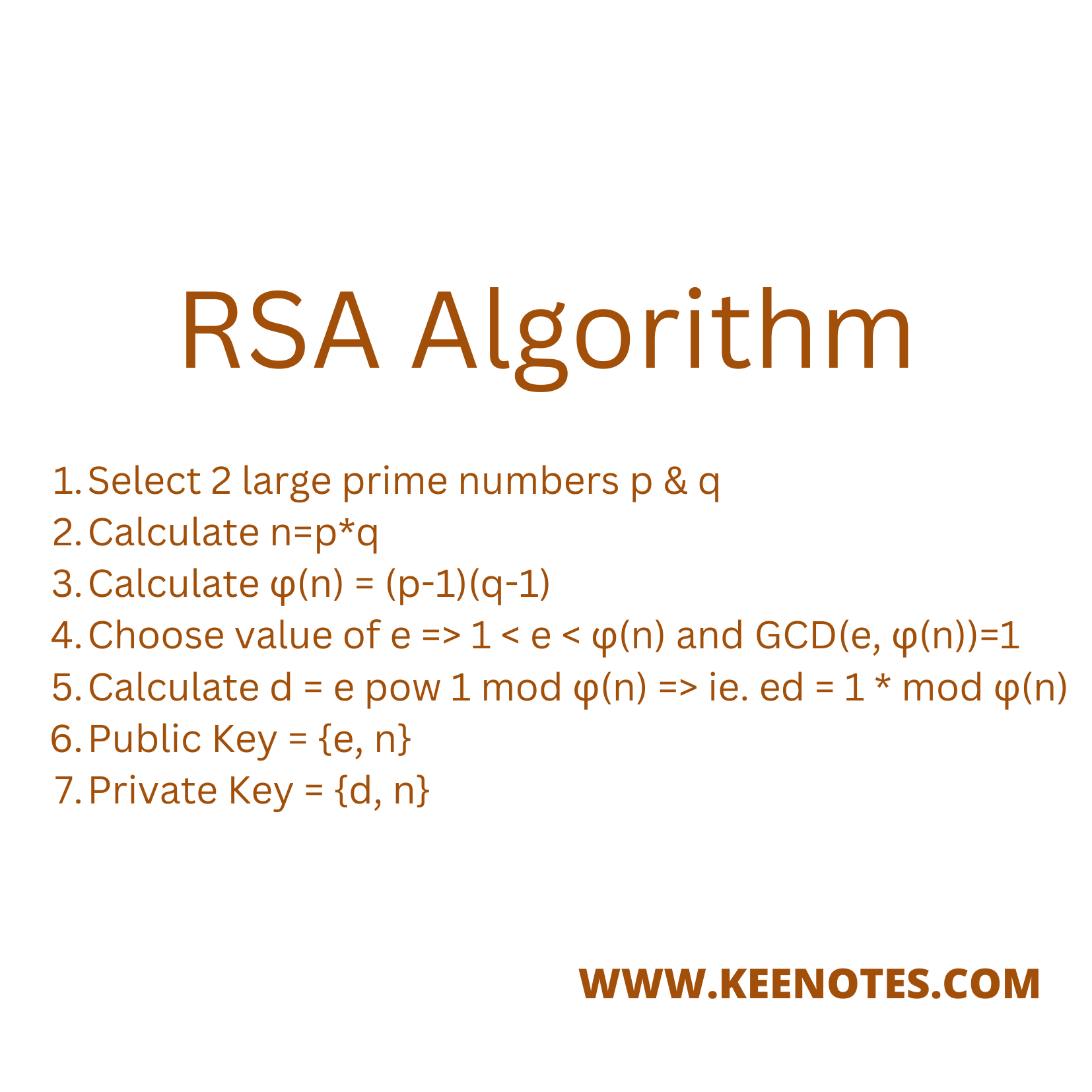
What Is Rsa Algorithm How Does An Rsa Work Mindmajix Learn how rsa works, its applications and security, and an example of encryption and decryption. rsa is a public key cryptography scheme that uses large prime numbers and modular arithmetic. Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Sion method. in this expository paper, we provide a historical and technical overview of the rsa . ryptosystem. we introduce the mathematical methods used in rsa, present the steps of the algorithm, discuss complexity results relating to the security of rsa, and implement a python ve. si. n of rsa. 1. What is the rsa algorithm? the rsa algorithm (rivest shamir adleman) is a public key cryptosystem that uses a pair of keys to secure digital communication and transactions over insecure networks, such as the internet.
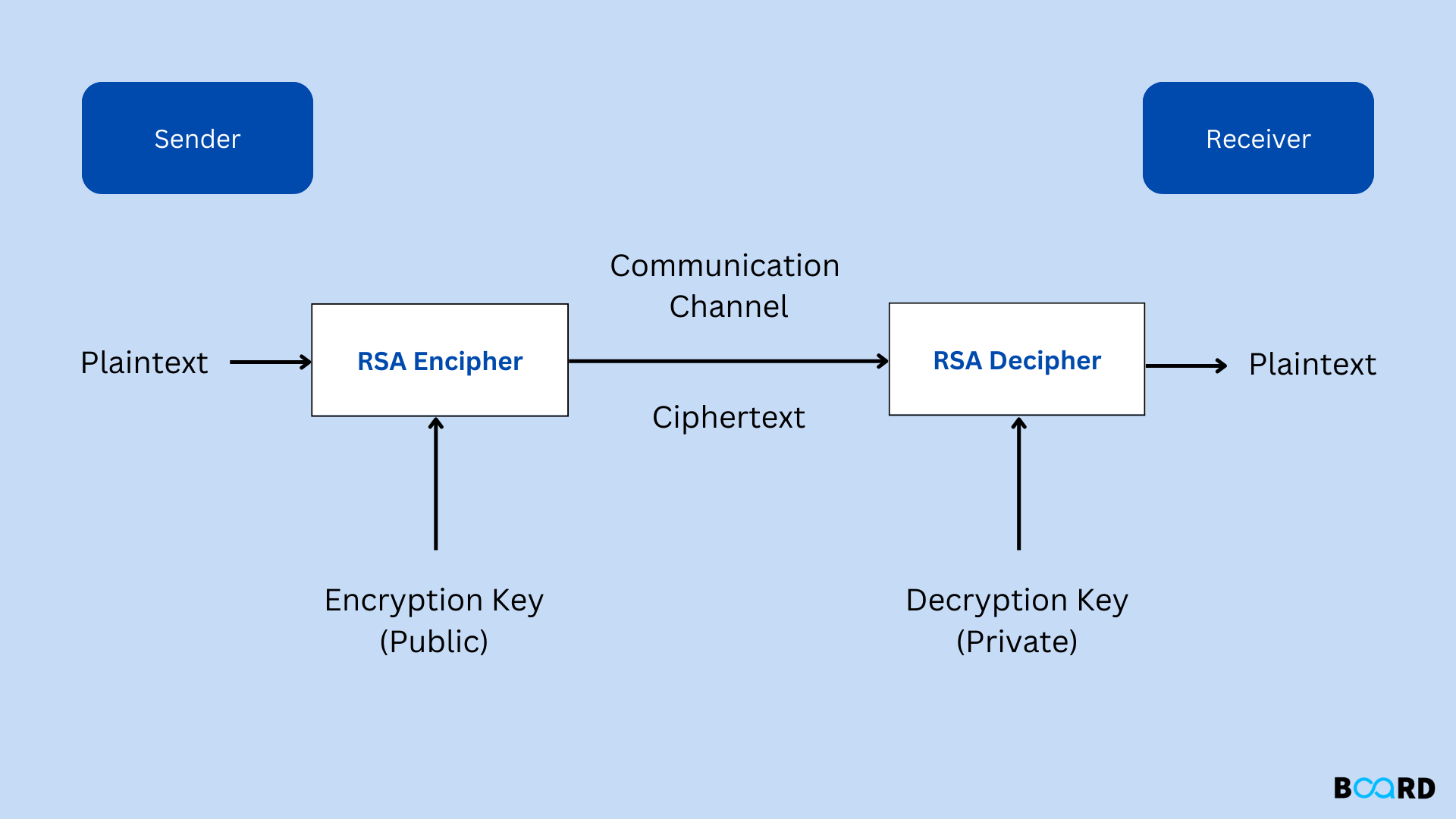
Rsa Cryptography Algorithm Sion method. in this expository paper, we provide a historical and technical overview of the rsa . ryptosystem. we introduce the mathematical methods used in rsa, present the steps of the algorithm, discuss complexity results relating to the security of rsa, and implement a python ve. si. n of rsa. 1. What is the rsa algorithm? the rsa algorithm (rivest shamir adleman) is a public key cryptosystem that uses a pair of keys to secure digital communication and transactions over insecure networks, such as the internet. Fakta inilah yang membuat algoritma rsa dianggap masih aman untuk saat ini. semakin panjang bilangan bulatnya, maka semakin lama waktu yang dibutuhkan untuk memfaktorkannya. Learn the basic idea, proof, and security of the rsa algorithm for public key cryptography. see examples, computational steps, and vulnerabilities of rsa and related protocols. Learn about rsa public key crypto system, its algorithm, security features and block diagram. see examples of key generation, encryption and decryption using rsa. Rsa is one of the most widely used encryption algorithms and has played a key role in securing digital communication for decades. its use of public and private keys makes it great for protecting sensitive data and verifying identities.

What Is Rsa Algorithm How Does An Rsa Work Mindmajix Fakta inilah yang membuat algoritma rsa dianggap masih aman untuk saat ini. semakin panjang bilangan bulatnya, maka semakin lama waktu yang dibutuhkan untuk memfaktorkannya. Learn the basic idea, proof, and security of the rsa algorithm for public key cryptography. see examples, computational steps, and vulnerabilities of rsa and related protocols. Learn about rsa public key crypto system, its algorithm, security features and block diagram. see examples of key generation, encryption and decryption using rsa. Rsa is one of the most widely used encryption algorithms and has played a key role in securing digital communication for decades. its use of public and private keys makes it great for protecting sensitive data and verifying identities.
Comments are closed.