Power Analysis Attacks Pptx
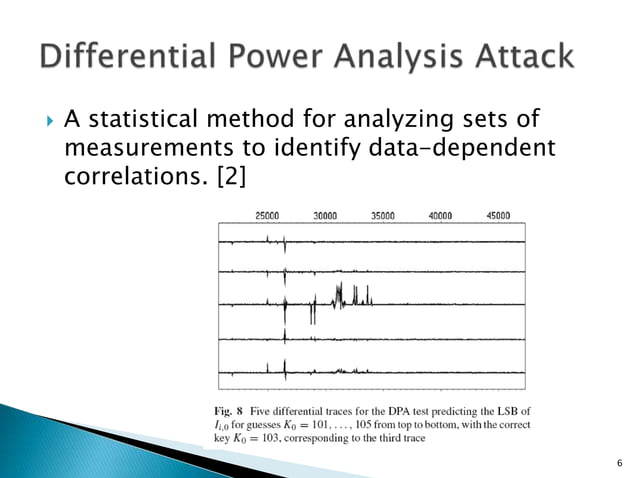
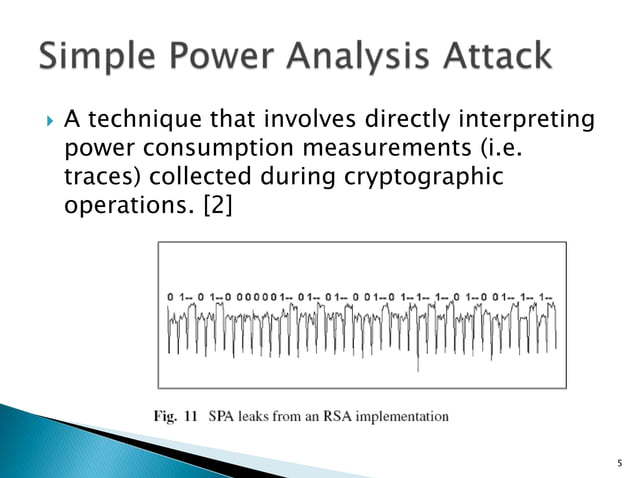
Power Analysis Attacks Ppt This document discusses differential power analysis (dpa) attacks against cryptographic devices. it begins with background on side channel attacks in general and then defines simple power analysis and differential power analysis attacks specifically. Power analysis is a form of side channel attack in which operation and key material can be exposed through the measurement of a cryptographic device’s power consumption.
Power Analysis Attacks Ppt The goal of countermeasures against dpa attacks is to make the power consumption of the cryptographic device independent of the intermediate values of the executed cryptographic algorithm. Deliver inspiring presentations with power analysis attack presentation templates and google slides. Power voltage sensors or impedance monitoring can detect probing measurement conditions (e.g., unusual analogue behaviour on the power delivery network). these approaches can be costly (area power), complex, and stochastic (not guaranteed). The power consumption of a cmos gate depends on the data: q: 0 >0 virtually no power cons. q: 1 >1 virtually no power cons. q: 0 >1 high power cons. (proportional to c2) q: 1 >0 high power cons. (proportional to c1).
Power Analysis Attacks Ppt Power voltage sensors or impedance monitoring can detect probing measurement conditions (e.g., unusual analogue behaviour on the power delivery network). these approaches can be costly (area power), complex, and stochastic (not guaranteed). The power consumption of a cmos gate depends on the data: q: 0 >0 virtually no power cons. q: 1 >1 virtually no power cons. q: 0 >1 high power cons. (proportional to c2) q: 1 >0 high power cons. (proportional to c1). This lecture explores the relationship between power consumption and cryptographic security in aes (advanced encryption standard). it discusses the fundamental theories behind power analysis attacks, including simple power analysis (spa) and correlation power analysis (cpa). Explore power analysis attacks: understand how they operate, see real examples, learn their risks, and discover effective protection strategies. In this comprehensive guide, we will explore the principles of power analysis attacks, their historical context, and the various types of attacks that have been developed. Power analysis attack on an asic aes implementation. ors, et. al. presented by michael cloppert discussion by jeffery, adam, and brad. discussion overview.
Power Analysis Attacks Ppt This lecture explores the relationship between power consumption and cryptographic security in aes (advanced encryption standard). it discusses the fundamental theories behind power analysis attacks, including simple power analysis (spa) and correlation power analysis (cpa). Explore power analysis attacks: understand how they operate, see real examples, learn their risks, and discover effective protection strategies. In this comprehensive guide, we will explore the principles of power analysis attacks, their historical context, and the various types of attacks that have been developed. Power analysis attack on an asic aes implementation. ors, et. al. presented by michael cloppert discussion by jeffery, adam, and brad. discussion overview.
Power Analysis Attacks Ppt In this comprehensive guide, we will explore the principles of power analysis attacks, their historical context, and the various types of attacks that have been developed. Power analysis attack on an asic aes implementation. ors, et. al. presented by michael cloppert discussion by jeffery, adam, and brad. discussion overview.
Comments are closed.