Power Analysis Attacks Ppt
Power Analysis Attacks Ppt This document discusses differential power analysis (dpa) attacks against cryptographic devices. it begins with background on side channel attacks in general and then defines simple power analysis and differential power analysis attacks specifically. The goal of countermeasures against dpa attacks is to make the power consumption of the cryptographic device independent of the intermediate values of the executed cryptographic algorithm.
Power Analysis Attacks Ppt Power analysis is a form of side channel attack in which operation and key material can be exposed through the measurement of a cryptographic device’s power consumption. Unlock the secrets of power analysis attacks with our comprehensive powerpoint presentation deck. this expertly designed resource covers techniques, examples, and strategies for understanding and mitigating vulnerabilities. This lecture explores the relationship between power consumption and cryptographic security in aes (advanced encryption standard). it discusses the fundamental theories behind power analysis attacks, including simple power analysis (spa) and correlation power analysis (cpa). Common side channels include power, timing, and electromagnetic (em) emissions. the core question is whether those observations reveal anything about secret data (especially cryptographic keys).
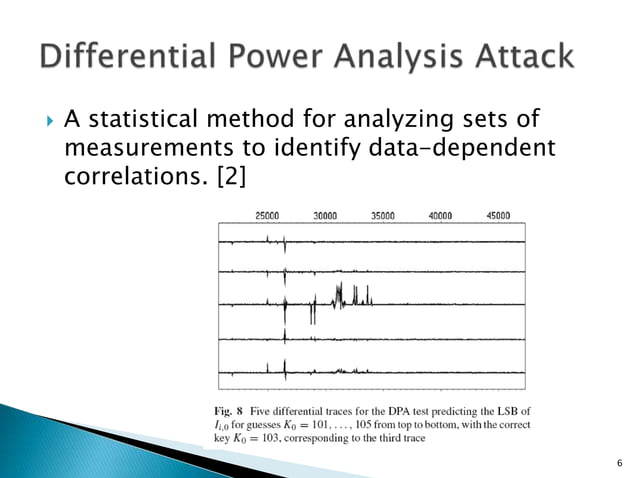
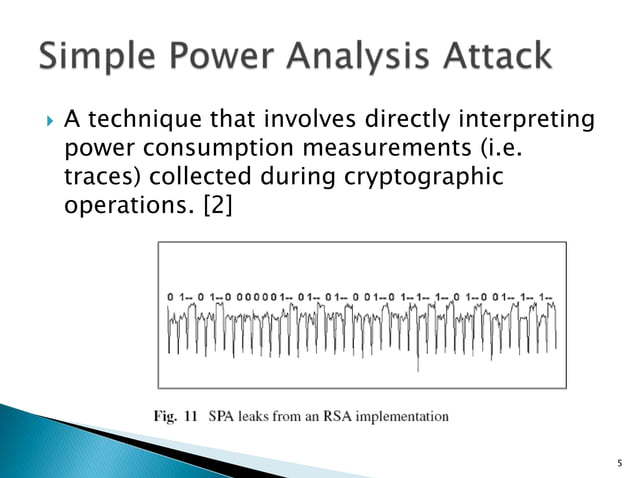
Power Analysis Attacks Ppt This lecture explores the relationship between power consumption and cryptographic security in aes (advanced encryption standard). it discusses the fundamental theories behind power analysis attacks, including simple power analysis (spa) and correlation power analysis (cpa). Common side channels include power, timing, and electromagnetic (em) emissions. the core question is whether those observations reveal anything about secret data (especially cryptographic keys). A simple power analysis attack on the twofish key schedule jose powerpoint ppt presentation. Overview introduction background what is a smart card evolution attacks power analysis conclusion background what is a ‘smart card’? vs. dumb cards why smart cards?. Kocher, joshua jaffe, and benjamin jun, 'differential power analysis', advances – a free powerpoint ppt presentation (displayed as an html5 slide show) on powershow id: 2050a6 zdc1z. The document discusses power analysis attacks and countermeasures. it describes simple power analysis (spa) attacks which visually inspect power traces to obtain secrets.
Power Analysis Attacks Ppt A simple power analysis attack on the twofish key schedule jose powerpoint ppt presentation. Overview introduction background what is a smart card evolution attacks power analysis conclusion background what is a ‘smart card’? vs. dumb cards why smart cards?. Kocher, joshua jaffe, and benjamin jun, 'differential power analysis', advances – a free powerpoint ppt presentation (displayed as an html5 slide show) on powershow id: 2050a6 zdc1z. The document discusses power analysis attacks and countermeasures. it describes simple power analysis (spa) attacks which visually inspect power traces to obtain secrets.
Comments are closed.