Pdf Face Morphing Attack Detection Using Privacy Aware Training Data

Pdf Face Morphing Attack Detection Using Privacy Aware Training Data In this paper, we tackle the privacy issues associated with the datasets used for the development of face morphing detection algorithms. to address related privacy concerns, we explore the idea of using a training database with faces of non–existing people, generated by stylegan. In this paper, we explore the efficacy of detection algorithms that are trained only on faces of non–existing people and their respective morphs.

Pdf Differential Newborn Face Morphing Attack Detection Using Wavelet This approach raises various privacy concerns and limits the amount of publicly available training data. in this paper, we explore the efficacy of detection algorithms that are trained only on faces of non existing people and their respective morphs. This approach raises various privacy concerns and limits the amount of publicly available training data. in this paper, we explore the efficacy of detection algorithms that are trained only on faces of non existing people and their respective morphs. In this paper, we explore the efficacy of detection algorithms that are trained only on faces of non existing people and their respective morphs. View a pdf of the paper titled face morphing attack detection using privacy aware training data, by marija ivanovska and 4 other authors.

Pdf Fusion Of Face Demorphing And Deep Face Representations For In this paper, we explore the efficacy of detection algorithms that are trained only on faces of non existing people and their respective morphs. View a pdf of the paper titled face morphing attack detection using privacy aware training data, by marija ivanovska and 4 other authors. Face morphing attack detection using privacy aware training data. in proceedings of the 31st international electrotechnical and computer science conference (under review), 2022. Literature review of face morphing attacks and generation face morphing repository 3 s mad 2022 syn mad 2022 competition on face morphing attack detection based on privacy aware synthetic training data.pdf at main · nz0001na face morphing repository. This work is the first to question the possibility of using synthetic face data as the basis of face mad development data. this was driven by presenting an extensive legal anal ysis on the privacy and security issues raised by using real biometric data.
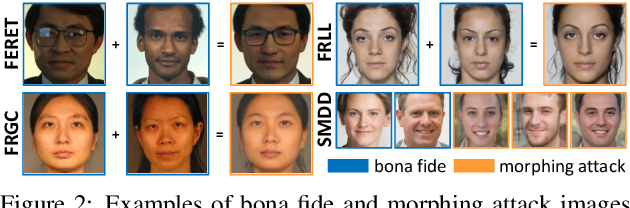
Face Morphing Attack Detection Using Privacy Aware Training Data Face morphing attack detection using privacy aware training data. in proceedings of the 31st international electrotechnical and computer science conference (under review), 2022. Literature review of face morphing attacks and generation face morphing repository 3 s mad 2022 syn mad 2022 competition on face morphing attack detection based on privacy aware synthetic training data.pdf at main · nz0001na face morphing repository. This work is the first to question the possibility of using synthetic face data as the basis of face mad development data. this was driven by presenting an extensive legal anal ysis on the privacy and security issues raised by using real biometric data.

Github Naserdamer Smdd Synthetic Face Morphing Attack Detection This work is the first to question the possibility of using synthetic face data as the basis of face mad development data. this was driven by presenting an extensive legal anal ysis on the privacy and security issues raised by using real biometric data.
Comments are closed.