3d Face Morphing Attack Generation Using Non Rigid Registration
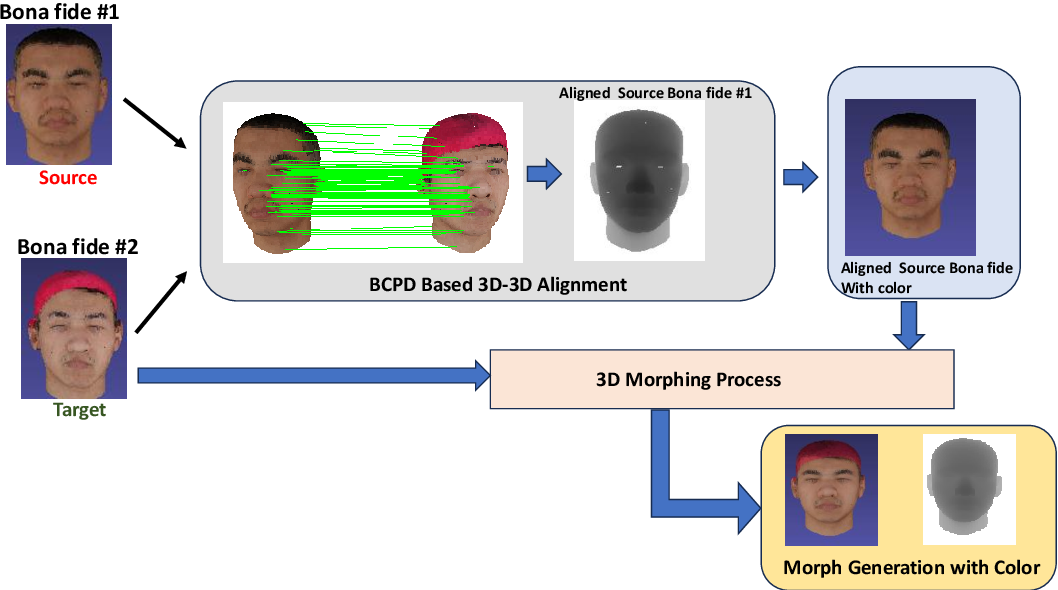
Figure 1 From 3d Face Morphing Attack Generation Using Non Rigid However, these systems are vulnerable to facial morphing attacks, which are generated by blending face color images of different subjects. this paper presents a new method for generating 3d face morphs from two bona fide point clouds. Face recognition systems (frs) have been found to be vulnerable to morphing attacks, where the morphed face image is generated by blending the face images from contributory data subjects. this.
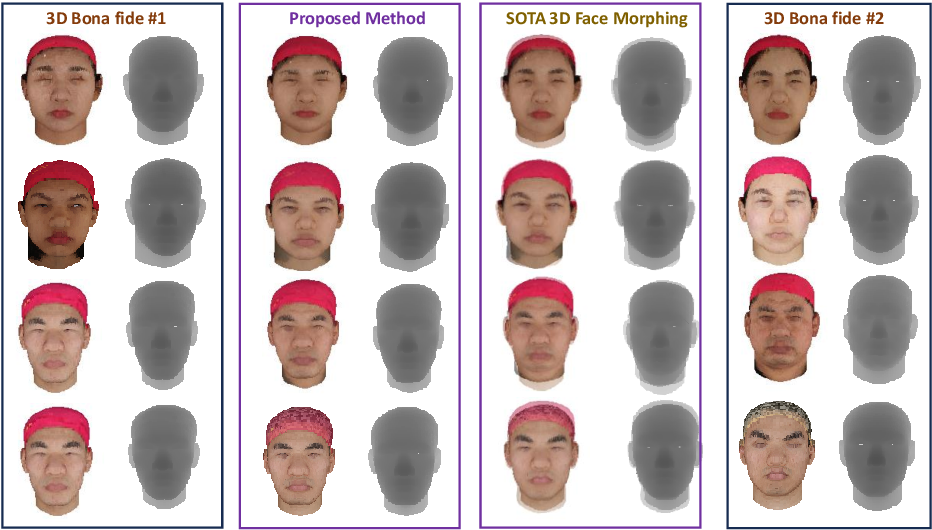
3d Face Morphing Attack Generation Using Non Rigid Registration This paper aims to provide a comprehensive overview of face morphing attacks and the developments happening in this field, and provides an overview of the most significant results from studies done in this area of research. This paper introduces a novel method for generating 3d face morphing attacks using non rigid registration of neutral expression point clouds, achieving a high generalized morphing attack potential (g map) of 97.93%, surpassing existing techniques. Article "3d face morphing attack generation using non rigid registration" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). Bibliographic details on 3d face morphing attack generation using non rigid registration.

3d Face Morphing Attack Generation Using Non Rigid Registration Article "3d face morphing attack generation using non rigid registration" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). Bibliographic details on 3d face morphing attack generation using non rigid registration. Abstract: face recognition systems (frs) have been found to be vulnerable to morphing attacks, where the morphed face image is generated by blending the face images from contributory data subjects. this work presents a novel direction for generating face morphing attacks in 3d. In this paper, we introduce an enhanced 3d facial registration algorithm that leverages edge constrained non rigid iterative closest point (icp) and a global spatial similarity metric. Face recognition systems (frs) have been found to be vulnerable to morphing attacks, where the morphed face image is generated by blending the face images from contributory data subjects. this work presents a novel direction for generating face morphing attacks in 3d. The 3d face point clouds corresponding to neutral expressions were used to generate the morphing generation, and the smiling expression was used to compute the attack potential of the proposed morphing technique.
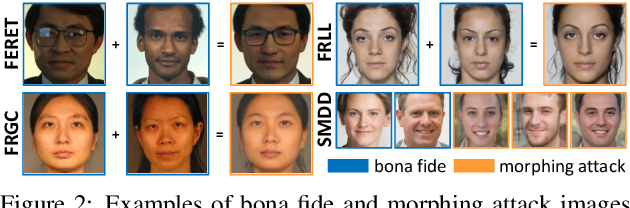
Face Morphing Attack Detection Using Privacy Aware Training Data Abstract: face recognition systems (frs) have been found to be vulnerable to morphing attacks, where the morphed face image is generated by blending the face images from contributory data subjects. this work presents a novel direction for generating face morphing attacks in 3d. In this paper, we introduce an enhanced 3d facial registration algorithm that leverages edge constrained non rigid iterative closest point (icp) and a global spatial similarity metric. Face recognition systems (frs) have been found to be vulnerable to morphing attacks, where the morphed face image is generated by blending the face images from contributory data subjects. this work presents a novel direction for generating face morphing attacks in 3d. The 3d face point clouds corresponding to neutral expressions were used to generate the morphing generation, and the smiling expression was used to compute the attack potential of the proposed morphing technique.

Face Morphing Attack Generation Detection A Comprehensive Survey Deepai Face recognition systems (frs) have been found to be vulnerable to morphing attacks, where the morphed face image is generated by blending the face images from contributory data subjects. this work presents a novel direction for generating face morphing attacks in 3d. The 3d face point clouds corresponding to neutral expressions were used to generate the morphing generation, and the smiling expression was used to compute the attack potential of the proposed morphing technique.
Comments are closed.