Microsoft Defender Vulnerability Scanning Eicqn

Microsoft Defender Vulnerability Scanning Eicqn Vulnerability management is enabled by default when you enable defender for servers. use the instructions in this article if you need to enable vulnerability scanning manually. This section describes the microsoft defender vulnerability management experience for customers using the microsoft defender xdr microsoft defender for identity preview.
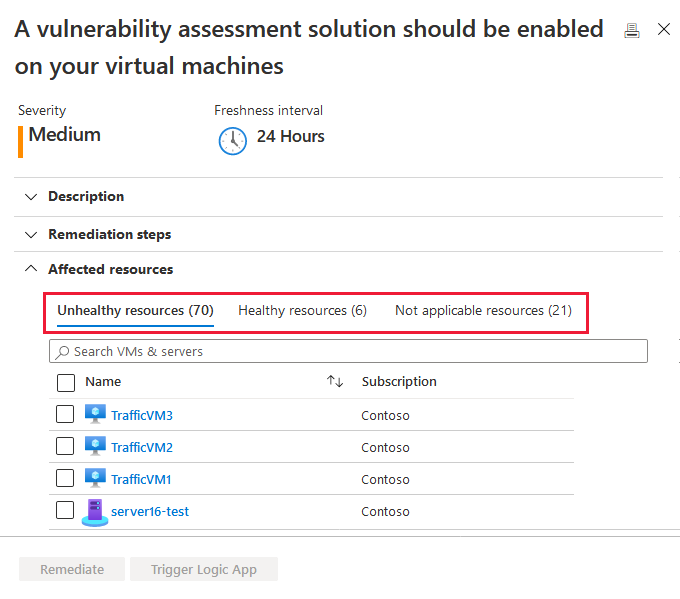
Microsoft Defender Vulnerability Scanning Eicqn Get agentless and agent based vulnerability scanning for agility and comprehensive workload protection. get proactive protection across different domains including endpoints, servers, and cloud workloads with defender vulnerability management. Microsoft defender for servers includes integrated vulnerability scanning capabilities through microsoft defender vulnerability management (mdvm). this helps identify weaknesses in server workloads across azure, aws, gcp, and on premises environments. Whether you have used the built in qualys scanner previously or are new to our vulnerability assessment solution, you can make sure you are using defender vulnerability management as your va provider. Learn about vulnerability scanning in the defender for servers plan in microsoft defender for cloud.
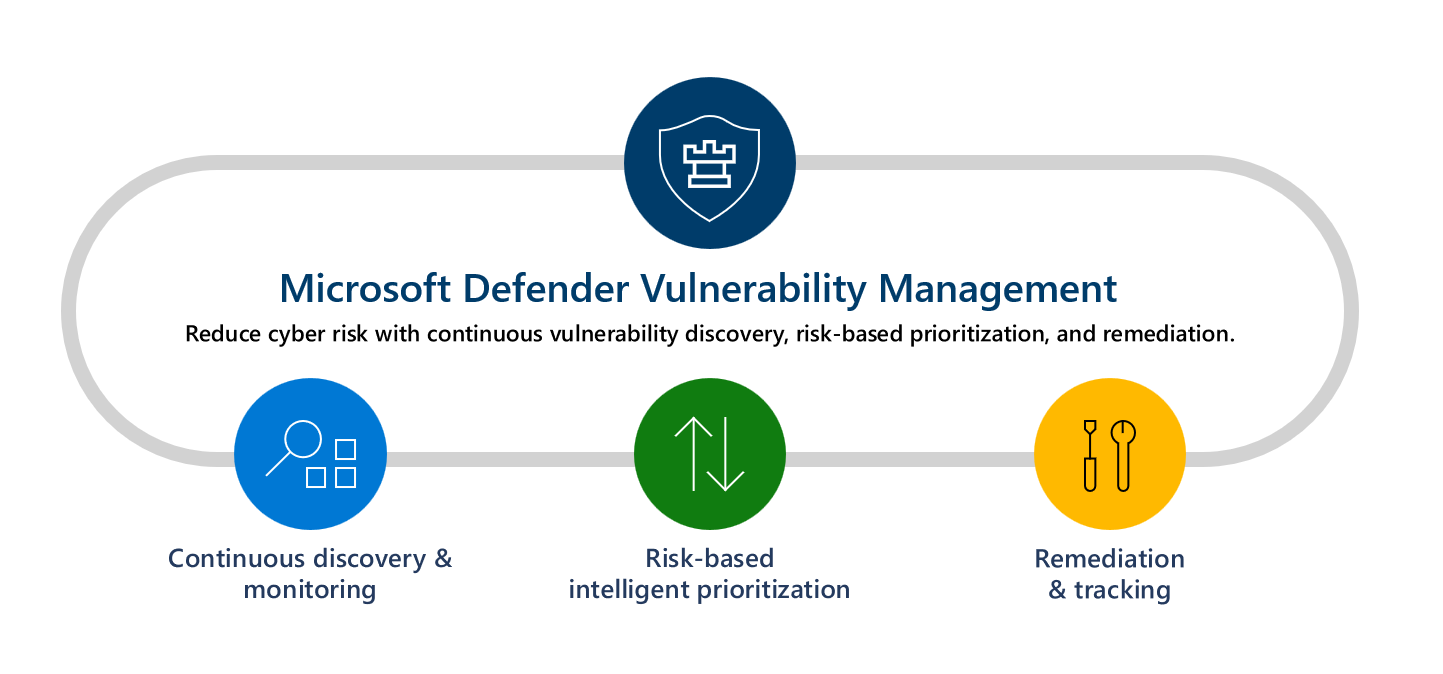
Microsoft Defender Vulnerability Management Microsoft Learn Whether you have used the built in qualys scanner previously or are new to our vulnerability assessment solution, you can make sure you are using defender vulnerability management as your va provider. Learn about vulnerability scanning in the defender for servers plan in microsoft defender for cloud. Set up authenticated network scans to discover network devices in microsoft defender for endpoint. Mdvm in defender helps discover vulnerabilities using the mde sensor; without the need of deploying additional collectors or agents. mdvm is based on continuous discovery. microsoft defender for endpoint continuously collects and sends telemetry of the device to the cloud. Common questions about the integrated microsoft defender vulnerability management solution in defender for cloud. Lists the common vulnerabilities and exposures (cve) id of weaknesses found in the software running in your organization. discovered by the microsoft defender vulnerability management capabilities.
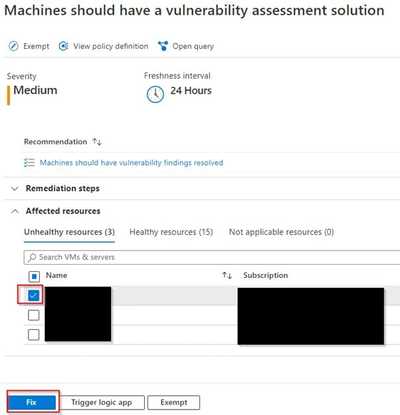
Vulnerability Scanning In Microsoft Defender For Server Joe Ho Blog Set up authenticated network scans to discover network devices in microsoft defender for endpoint. Mdvm in defender helps discover vulnerabilities using the mde sensor; without the need of deploying additional collectors or agents. mdvm is based on continuous discovery. microsoft defender for endpoint continuously collects and sends telemetry of the device to the cloud. Common questions about the integrated microsoft defender vulnerability management solution in defender for cloud. Lists the common vulnerabilities and exposures (cve) id of weaknesses found in the software running in your organization. discovered by the microsoft defender vulnerability management capabilities.

Vulnerability Scanning In Microsoft Defender For Server Joe Ho Blog Common questions about the integrated microsoft defender vulnerability management solution in defender for cloud. Lists the common vulnerabilities and exposures (cve) id of weaknesses found in the software running in your organization. discovered by the microsoft defender vulnerability management capabilities.
Comments are closed.