Microsoft Defender Vulnerability Management

Microsoft Defender Vulnerability Management Add On Using microsoft threat intelligence, breach likelihood predictions, business contexts, and devices assessments, defender vulnerability management rapidly and continuously prioritizes the biggest vulnerabilities on your most critical assets and provides security recommendations to mitigate risk. Microsoft defender for servers includes integrated vulnerability scanning capabilities through microsoft defender vulnerability management (mdvm). this helps identify weaknesses in server workloads across azure, aws, gcp, and on premises environments.
About The Microsoft Defender Vulnerability Management Trial Microsoft Microsoft defender vulnerability management delivers asset visibility, continuous real time discovery and assessment of vulnerabilities, context aware threat & business prioritization, and built in remediation processes. Learn how to reduce cybersecurity threats with a risk based approach to vulnerability management across endpoints and cloud workloads. see plans and pricing, key capabilities, and latest updates of defender vulnerability management. Compare defender vulnerability management offerings. learn about the differences between the plans and select the plan that suits your organization's needs. The exploitation of unpatched vulnerabilities in microsoft defender indicates a failure to apply critical security patches, violating pci dss requirement 6.2. the incident suggests deficiencies in the organization's cybersecurity policy, particularly in vulnerability management and patching processes, as required by nydfs 500.03.
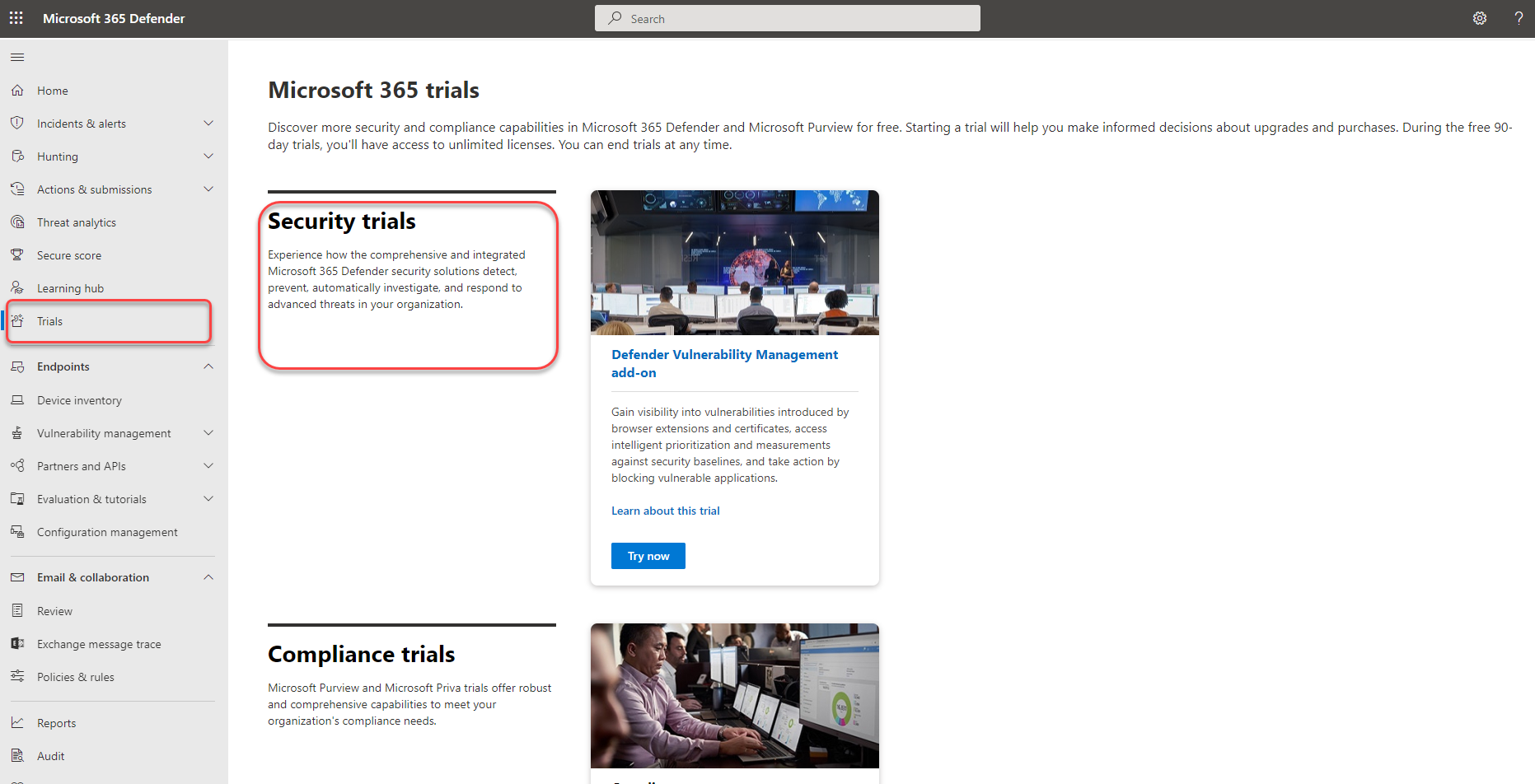
About The Microsoft Defender Vulnerability Management Trial Microsoft Compare defender vulnerability management offerings. learn about the differences between the plans and select the plan that suits your organization's needs. The exploitation of unpatched vulnerabilities in microsoft defender indicates a failure to apply critical security patches, violating pci dss requirement 6.2. the incident suggests deficiencies in the organization's cybersecurity policy, particularly in vulnerability management and patching processes, as required by nydfs 500.03. Run hipaa compliant vulnerability scanning in microsoft 365 to detect risks, prioritize remediation, enforce dlp and produce audit ready evidence to protect phi. Defender vulnerability management uses microsoft's threat intelligence, breach likelihood predictions, business contexts, and device assessments to quickly prioritize the biggest vulnerabilities in your organization. Microsoft defender for servers provides integrated vulnerability assessment capabilities using microsoft defender vulnerability management (mdvm). it supports both agentless and agent based scanning to detect vulnerabilities across azure, aws, gcp, and on premises machines. Learn how to use microsoft defender vulnerability management to reduce cyber risk with continuous vulnerability discovery and assessment, risk based prioritization, and remediation. find out how to get started, explore inventories, detect and assess threats, identify and prioritize risk, and remediate vulnerabilities.
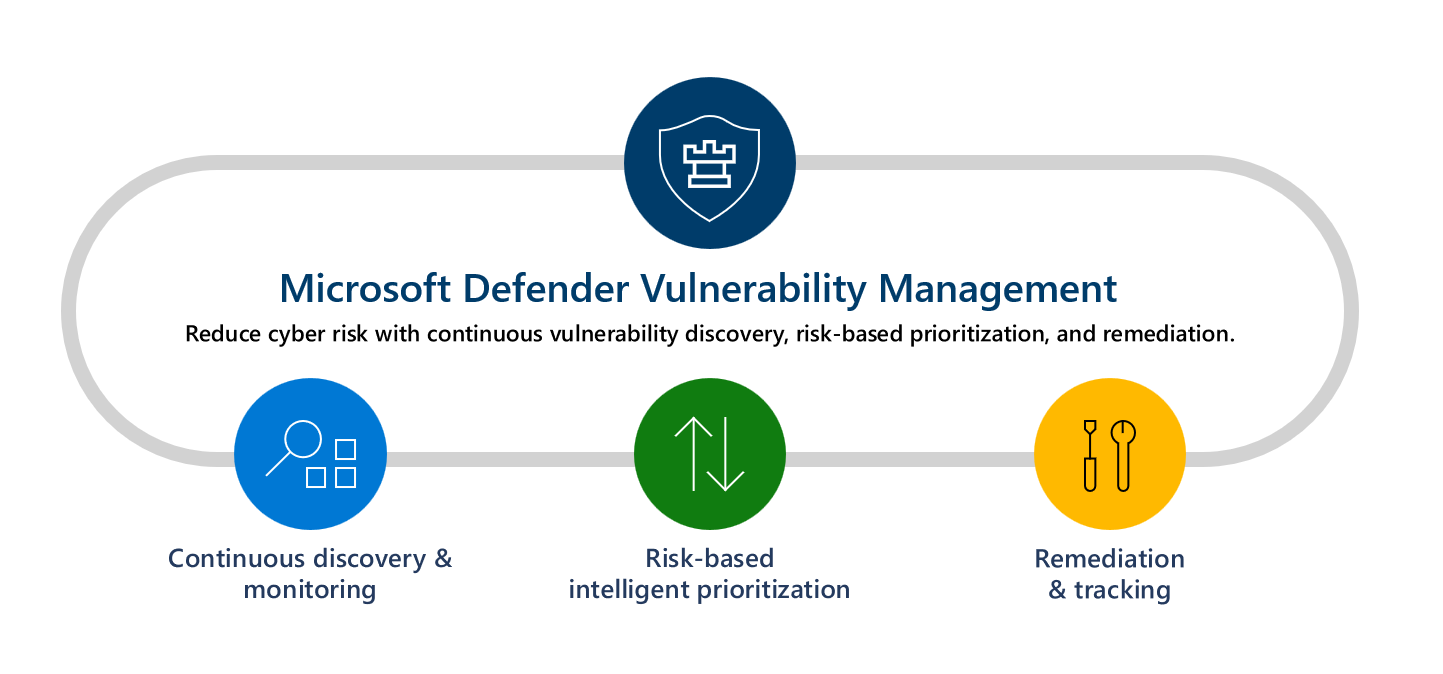
Microsoft Defender Vulnerability Management Microsoft Learn Run hipaa compliant vulnerability scanning in microsoft 365 to detect risks, prioritize remediation, enforce dlp and produce audit ready evidence to protect phi. Defender vulnerability management uses microsoft's threat intelligence, breach likelihood predictions, business contexts, and device assessments to quickly prioritize the biggest vulnerabilities in your organization. Microsoft defender for servers provides integrated vulnerability assessment capabilities using microsoft defender vulnerability management (mdvm). it supports both agentless and agent based scanning to detect vulnerabilities across azure, aws, gcp, and on premises machines. Learn how to use microsoft defender vulnerability management to reduce cyber risk with continuous vulnerability discovery and assessment, risk based prioritization, and remediation. find out how to get started, explore inventories, detect and assess threats, identify and prioritize risk, and remediate vulnerabilities.
Comments are closed.