Microsoft Defender Vulnerability Management Why Is It Important

Microsoft Defender Vulnerability Management Add On Using microsoft threat intelligence, breach likelihood predictions, business contexts, and devices assessments, defender vulnerability management rapidly and continuously prioritizes the biggest vulnerabilities on your most critical assets and provides security recommendations to mitigate risk. Microsoft defender for servers provides integrated vulnerability assessment capabilities using microsoft defender vulnerability management (mdvm). it supports both agentless and agent based scanning to detect vulnerabilities across azure, aws, gcp, and on premises machines.
About The Microsoft Defender Vulnerability Management Trial Microsoft Part 9 introduces microsoft defender vulnerability management (mdvm) the continuous assessment engine that discovers vulnerabilities before attackers do and tells you exactly which ones to fix first based on real risk, not just cve scores. Microsoft defender vulnerability management is completely agentless and collects data based on the installed mde sensor. data is stored for up to 180 days in defender and 30 days in advanced hunting. Microsoft defender vulnerability management (mdvm) has come a long way and has become an indispensable part of microsoft defender for endpoint (mde) and the whole microsoft defender xdr ecosystem, that deserves your attention and daily operationalization. None of this is surprising given microsoft’s product footprint, but it underscores the need for robust, independent vulnerability management tools raising the critical question many security teams ask today.
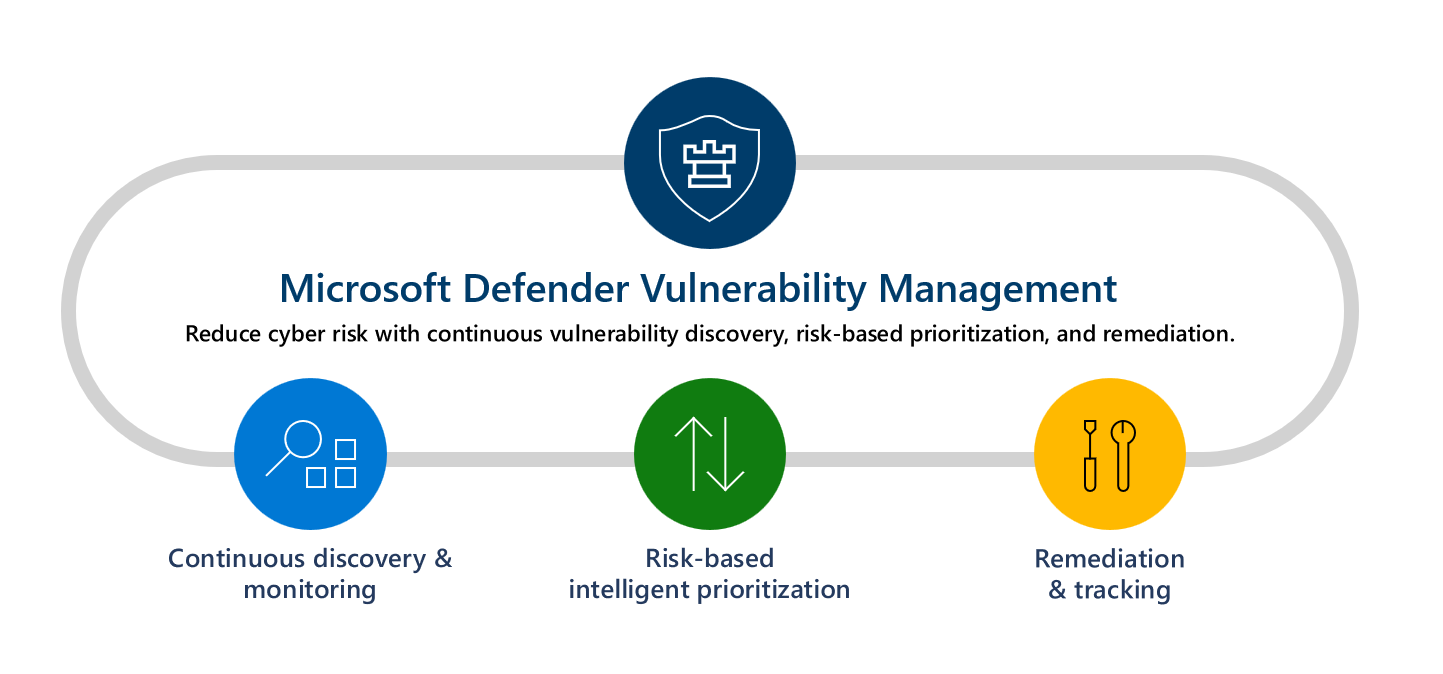
Microsoft Defender Vulnerability Management Microsoft Learn Microsoft defender vulnerability management (mdvm) has come a long way and has become an indispensable part of microsoft defender for endpoint (mde) and the whole microsoft defender xdr ecosystem, that deserves your attention and daily operationalization. None of this is surprising given microsoft’s product footprint, but it underscores the need for robust, independent vulnerability management tools raising the critical question many security teams ask today. At its core, defender vulnerability management is a component of microsoft defender for endpoint plan 2 that uses real time threat intelligence, breach likelihood scoring, and device specific context to identify, assess, prioritize, and remediate vulnerabilities across all your endpoints. Microsoft defender vulnerability management identifies and prioritizes security exposures across devices in an organization’s environment. it integrates with microsoft security tools to provide contextual risk insights and remediation guidance. The software delivers continuous vulnerability discovery and prioritization by analyzing devices, operating systems, and applications for security weaknesses. it provides risk based insights, threat intelligence integration, and recommendations for remediation actions. Using microsoft threat intelligence, breach likelihood predictions, business contexts, and devices assessments, defender vulnerability management rapidly and continuously prioritizes the biggest vulnerabilities on your most critical assets and provides security recommendations to mitigate risk.
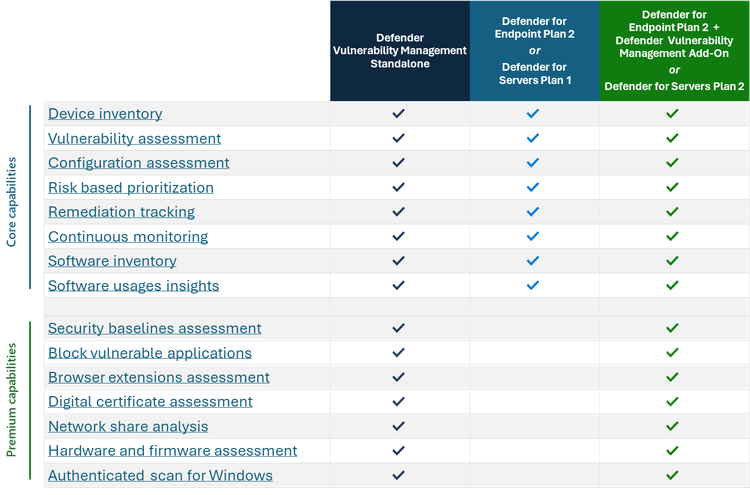
Defender Vulnerability Management Ga In Government Cloud Microsoft At its core, defender vulnerability management is a component of microsoft defender for endpoint plan 2 that uses real time threat intelligence, breach likelihood scoring, and device specific context to identify, assess, prioritize, and remediate vulnerabilities across all your endpoints. Microsoft defender vulnerability management identifies and prioritizes security exposures across devices in an organization’s environment. it integrates with microsoft security tools to provide contextual risk insights and remediation guidance. The software delivers continuous vulnerability discovery and prioritization by analyzing devices, operating systems, and applications for security weaknesses. it provides risk based insights, threat intelligence integration, and recommendations for remediation actions. Using microsoft threat intelligence, breach likelihood predictions, business contexts, and devices assessments, defender vulnerability management rapidly and continuously prioritizes the biggest vulnerabilities on your most critical assets and provides security recommendations to mitigate risk.
Comments are closed.