Hack Sql Database Using Sql Injection And Brute Force With Sqlmap

Brute Force Dos And Sql Injection Ocr Computer Science Complete Sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting sql injection flaws and taking over of database servers. Sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting sql injection flaws and taking over of database servers.
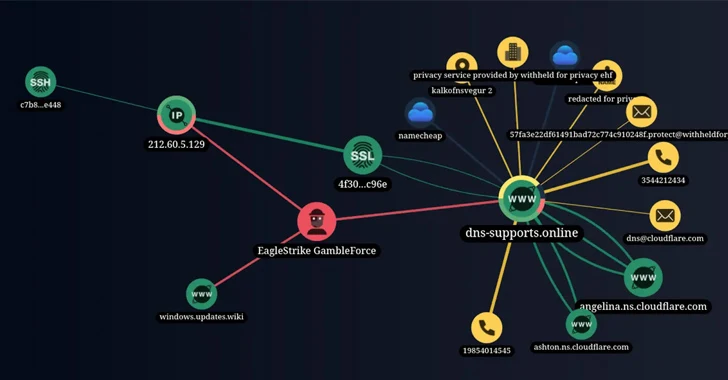
New Hacker Group Gambleforce Tageting Apac Firms Using Sql Injection Sqlmap is an open source tool that automatically finds and exploits sql injection vulnerabilities. we can use it to test web applications for sql injection vulnerabilities and gain access to a vulnerable database. When a site appears to be vulnerable to sql injection (sqli) due to unusual server responses to sqli related inputs, the first step is to understand how to inject data into the query without disrupting it. Learn how to hack sql database, performing authentication bypass with sql injection (sqli) and sqlmap, a tool available in kali linux. this ethical hacking and penetration testing. In this blog post, we’ll explore 15 sql injection attack recipes that leverage automation tools such as sqlmap. each scenario will be described with specific ingredients, steps, and.

The Anatomy Of An Sql Injection Attack And How To Avoid One Learn how to hack sql database, performing authentication bypass with sql injection (sqli) and sqlmap, a tool available in kali linux. this ethical hacking and penetration testing. In this blog post, we’ll explore 15 sql injection attack recipes that leverage automation tools such as sqlmap. each scenario will be described with specific ingredients, steps, and. With its extensive features, sqlmap can identify injection points, enumerate databases and tables, extract data, run arbitrary sql queries, and even brute force database credentials. This cheat sheet focuses on real world sqli exploitation with hands on examples, bypassing security filters, and using tools like burp suite and sqlmap. setting up a testing environment. Sqlmap is an essential tool for detecting and exploiting all types of sql injections (sqli). this article explains how sqlmap works and its key features. In this comprehensive 2600 word guide, we will understand what sql injection is, learn how to use the powerful sqlmap tool to find and exploit sql injection flaws, and look at ways to prevent such attacks.

Sqlmap Uncovering And Exploiting Sql Injection Vulnerabilities With its extensive features, sqlmap can identify injection points, enumerate databases and tables, extract data, run arbitrary sql queries, and even brute force database credentials. This cheat sheet focuses on real world sqli exploitation with hands on examples, bypassing security filters, and using tools like burp suite and sqlmap. setting up a testing environment. Sqlmap is an essential tool for detecting and exploiting all types of sql injections (sqli). this article explains how sqlmap works and its key features. In this comprehensive 2600 word guide, we will understand what sql injection is, learn how to use the powerful sqlmap tool to find and exploit sql injection flaws, and look at ways to prevent such attacks.
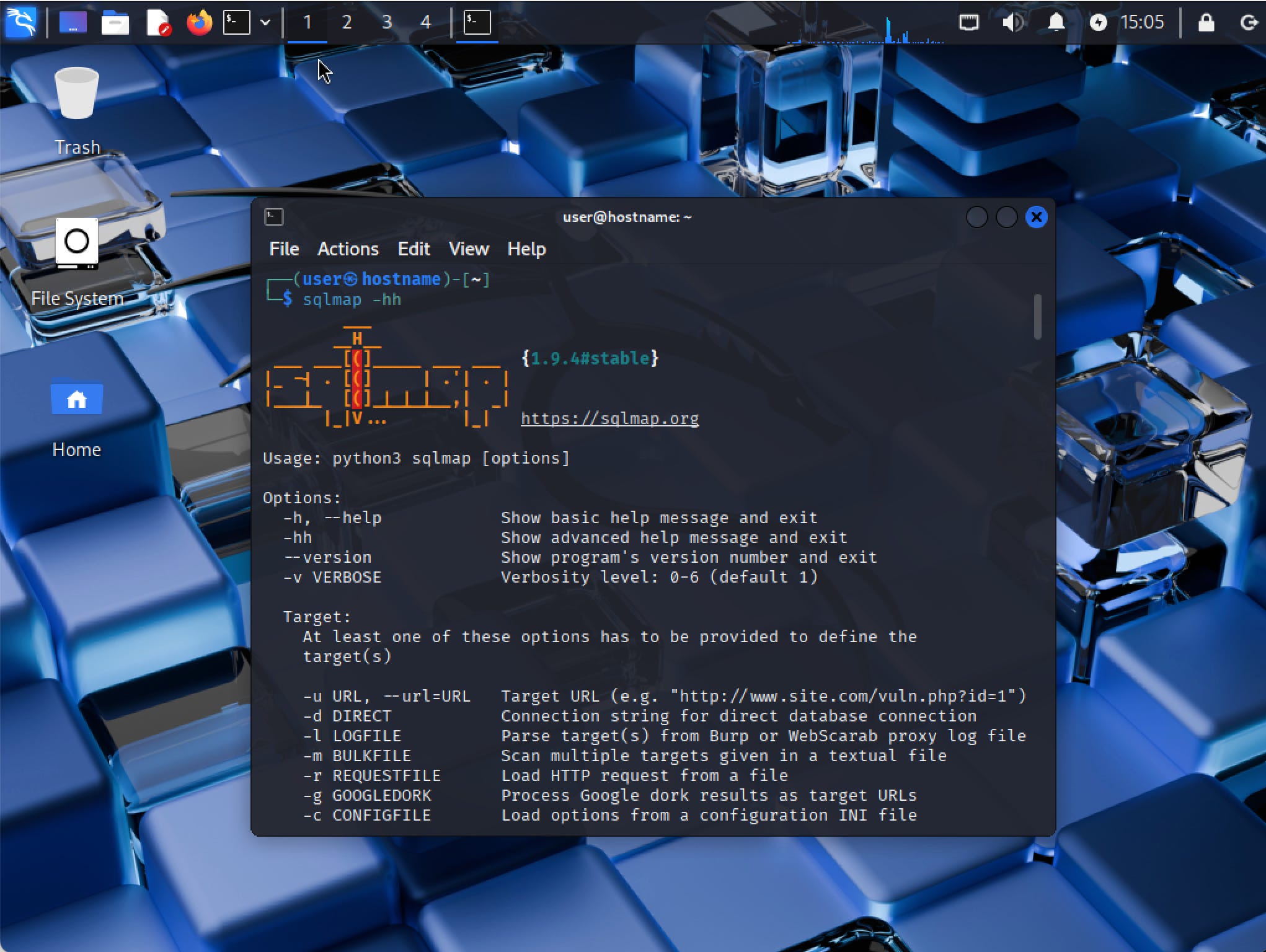
Sqlmap Tool Identify And Exploit Sql Injection Vulnerabilities Lab Sqlmap is an essential tool for detecting and exploiting all types of sql injections (sqli). this article explains how sqlmap works and its key features. In this comprehensive 2600 word guide, we will understand what sql injection is, learn how to use the powerful sqlmap tool to find and exploit sql injection flaws, and look at ways to prevent such attacks.
Comments are closed.