Exploiting Sql Injection With Nmap And Sqlmap Hacking Articles
Sqlmap Tool Identify And Exploit Sql Injection Vulnerabilities Lab Learn to conduct an nmap sql injection scan with sqlmap to identify vulnerabilities and exploit them effectively. This sql injection assessment is critical for organizations to identify and remediate severe web application vulnerabilities that could lead to complete database compromise.
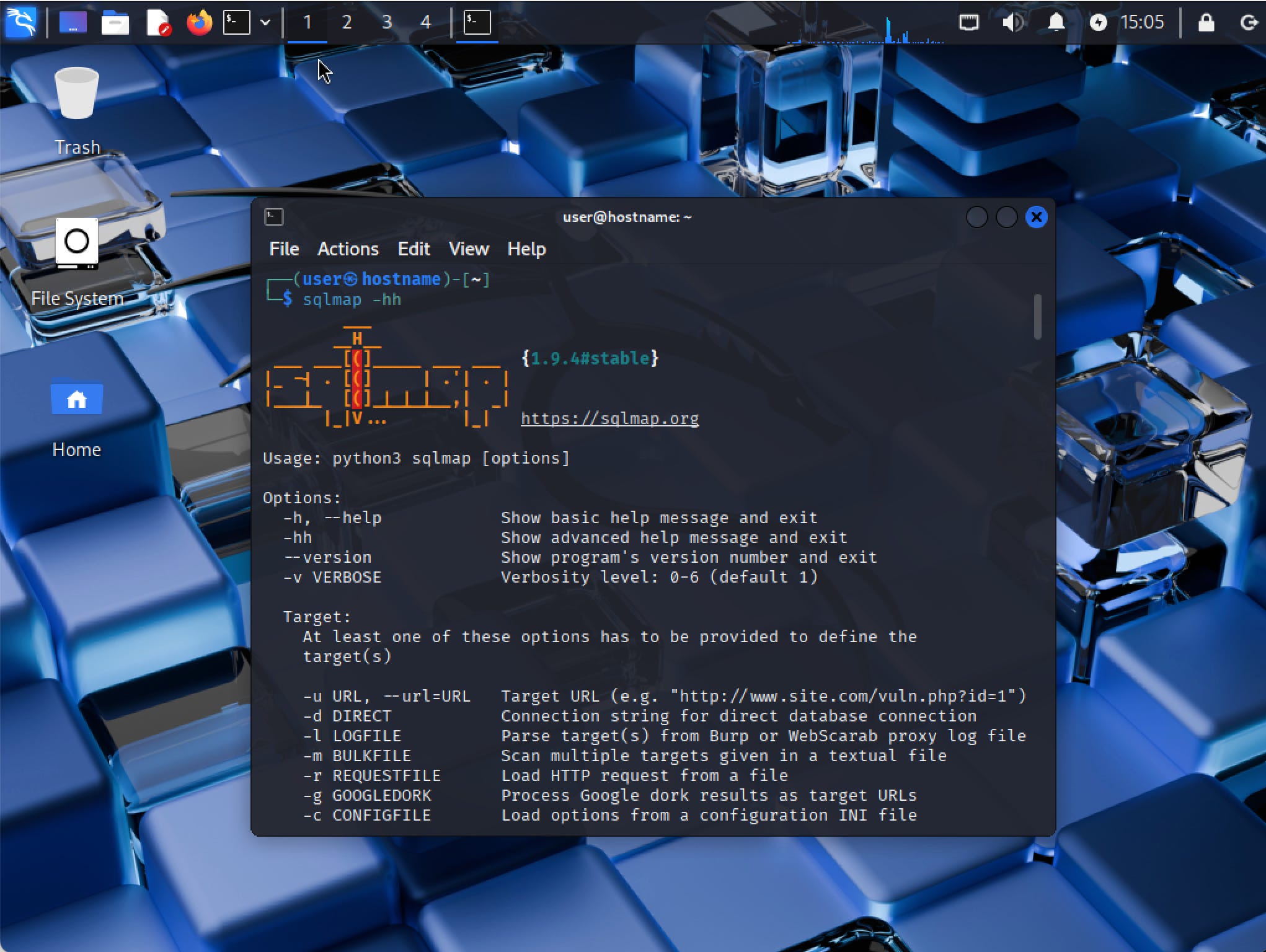
Sqlmap Tool Identify And Exploit Sql Injection Vulnerabilities Lab Nowadays, web applications are an essential part of our lives. the vulnerabilities in these applications enable hackers to gain access to confidential informati. Learn how to exploit sql injection vulnerabilities with nmap! this lab covers identifying sql injection points, determining database types, and retrieving sensitive data like database names, table names, and column data using nmap sql injection techniques. In this write up, i’ll walk you through my exact path — the one that relied heavily on nmap for discovery and sqlmap for efficient database dumping — all the way to root. Master sqlmap on kali linux with this expert guide to automated sql injection, data extraction, and system control techniques.

Sqlmap Uncovering And Exploiting Sql Injection Vulnerabilities In this write up, i’ll walk you through my exact path — the one that relied heavily on nmap for discovery and sqlmap for efficient database dumping — all the way to root. Master sqlmap on kali linux with this expert guide to automated sql injection, data extraction, and system control techniques. Test sql injection with sqlmap tool in this hands on pen testing lab exercise. learn how to find and then exploit sql injection, test it in a secure environment. Discover how to detect and exploit sql injections with sqlmap. a complete guide to using this pentest tool, with practical explanations and tips for securing your databases. This article is about how to scan any target for sql injection using nmap and then exploit the target with sqlmap if nmap finds the target is vulnerable to sql injection. Stay updated on security best practices to protect your web applications from sql injection and other vulnerabilities. using sqlmap with session cookies provides penetration testers with a powerful tool to detect and exploit sql injection vulnerabilities in login protected web applications.
Comments are closed.