Database Hacking Sql Injection 2026
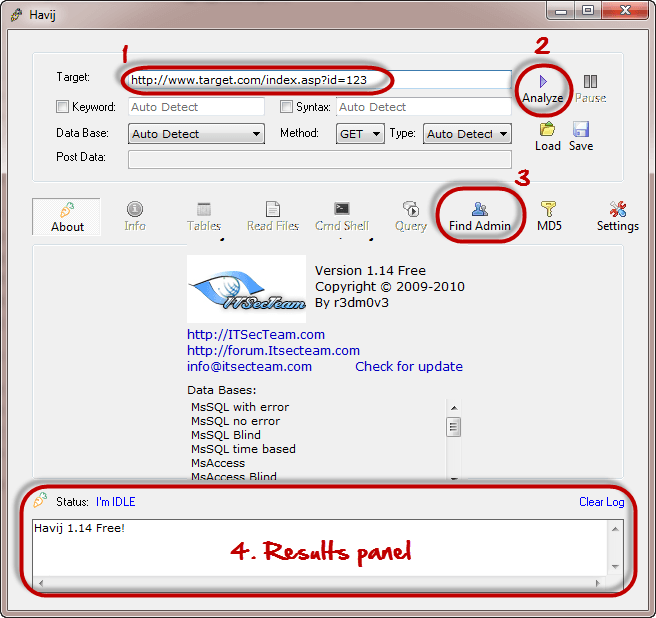
Database Hacking Using Sql Injection Attack Buranprofessor Focus on education, not exploitation 💡 key takeaways: • sql injection remains prevalent in 2026 • understanding both attack and defense is crucial • automation tools don't replace manual. Our purpose will be to access all the data in the database using this sql injection cheat sheet. as we are trying to guess the backend sql statement to fit in our query instead of expected arguments, sqli attacking process can vary.

Demystifying Sql Injection And Database Security Defend Edge Sql injection in modern apps: still a threat in 2026? sql injection is a persistent threat that can expose or alter sensitive data; this guide covers key prevention strategies and shows how grsee helps secure your applications. Explore 10 dangerous injection attacks in 2026, including sql injection, command injection, ldap injection, and modern exploit risks. Explore the latest news, real world incidents, expert analysis, and trends in sql injection — only on the hacker news, the leading cybersecurity and it news platform. Major data breaches affecting millions of users have been traced to sql injection vulnerabilities. the primary defense is parameterized queries (prepared statements), which separate sql code from data at the protocol level.

Sql Injection Attacks Know How To Prevent Them Edureka Explore the latest news, real world incidents, expert analysis, and trends in sql injection — only on the hacker news, the leading cybersecurity and it news platform. Major data breaches affecting millions of users have been traced to sql injection vulnerabilities. the primary defense is parameterized queries (prepared statements), which separate sql code from data at the protocol level. Tl;dr: security startup codewall pointed an autonomous ai agent at mckinsey's internal ai platform lilli on february 28, 2026. within two hours — with no credentials, no insider help, no human guidance — the agent had full read write access to the production database. Master database security with this comprehensive sql injection tutorial. learn how to identify vulnerabilities, perform legal tests, and implement secure code. Sql injection attacks exploit insecure application logic to manipulate database queries. this article explains how sqli works and how to prevent it. Sql injection in 2026: still exploited, still costly sql injection remains one of the most exploited web vulnerabilities. the reason is simple. many systems still rely on insecure query handling.
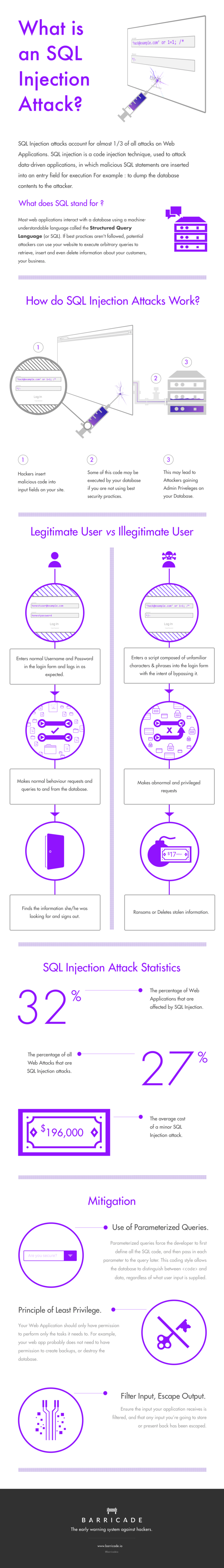
Infographic What Is Sql Injection Attack And How Does It Works Tl;dr: security startup codewall pointed an autonomous ai agent at mckinsey's internal ai platform lilli on february 28, 2026. within two hours — with no credentials, no insider help, no human guidance — the agent had full read write access to the production database. Master database security with this comprehensive sql injection tutorial. learn how to identify vulnerabilities, perform legal tests, and implement secure code. Sql injection attacks exploit insecure application logic to manipulate database queries. this article explains how sqli works and how to prevent it. Sql injection in 2026: still exploited, still costly sql injection remains one of the most exploited web vulnerabilities. the reason is simple. many systems still rely on insecure query handling.
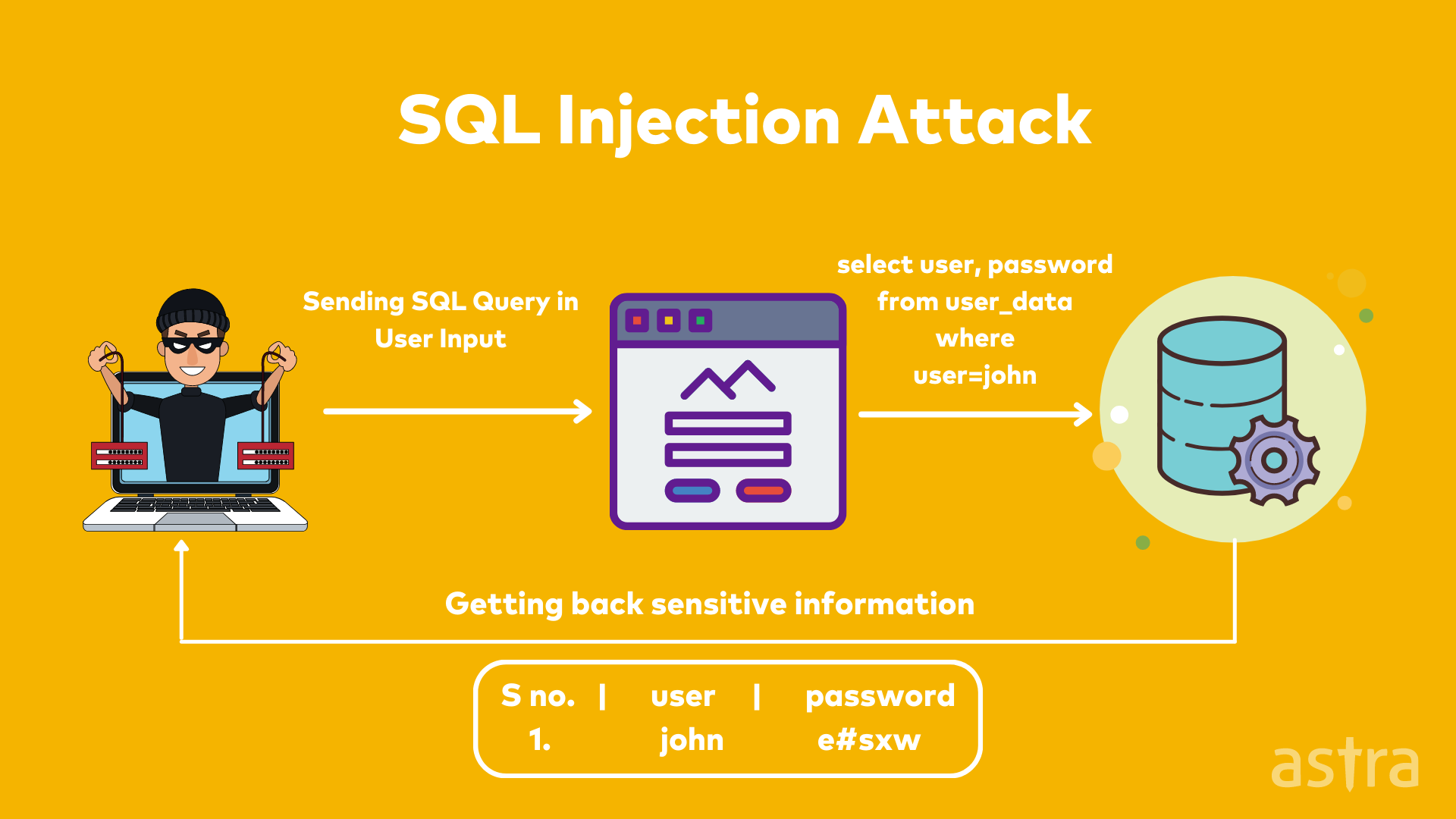
A Quick Guide On Sql Server Audits Astra Security Sql injection attacks exploit insecure application logic to manipulate database queries. this article explains how sqli works and how to prevent it. Sql injection in 2026: still exploited, still costly sql injection remains one of the most exploited web vulnerabilities. the reason is simple. many systems still rely on insecure query handling.

Database Hacking Common Sql Injection Commands Hackers Arise
Comments are closed.