Database Hacking Common Sql Injection Commands Hackers Arise
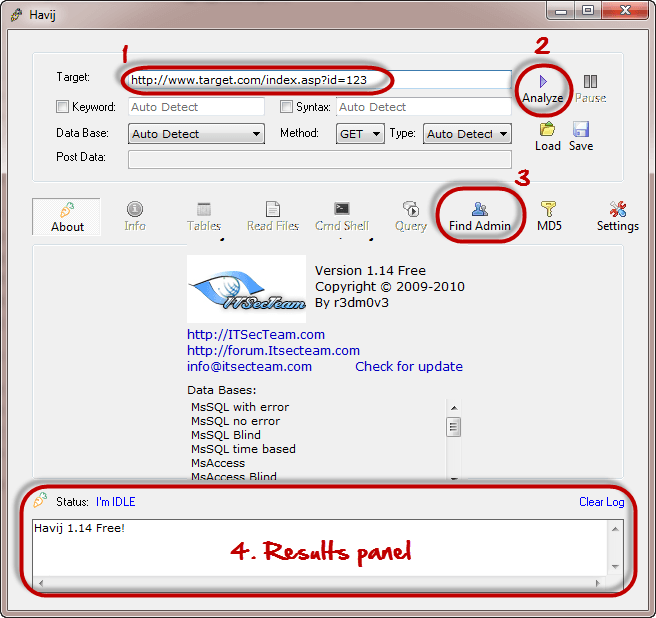
Database Hacking Using Sql Injection Attack Buranprofessor When testing for sql injection vulnerabilities, these are some of the most common commands and special characters. the better you understand sql, the more successful you will be with sql injection. Read this practical technical guide about the 5 most common sql injection attacks and how to prevent them. it packs real life examples, mitigation steps & more!.

Sql Injection Attacks Know How To Prevent Them Edureka Use the invicti sql injection cheat sheet to learn about exploiting different variants of the sql injection vulnerability. the cheat sheet includes technical information and payloads for sql injection attacks against mysql, microsoft sql server, oracle and postgresql database servers. This sql injection cheat sheet contains examples of useful syntax that you can use to perform a variety of tasks that often arise when performing sql injection attacks. Beyond data retrieval, sql injection can alter database content, impacting data integrity. attackers might delete or modify records, disrupt services, or execute commands leading to information loss or corruption. This cheat sheet contains vital sql injection payloads, commands, and tips that will help penetration testers and ethical hackers to find and use weaknesses in applications.
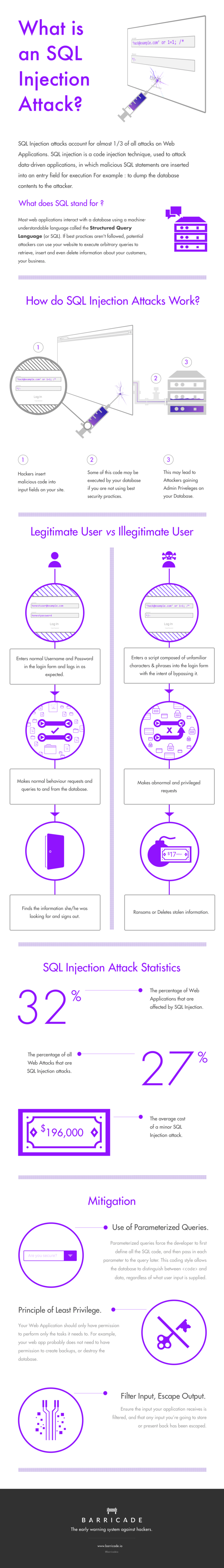
Infographic What Is Sql Injection Attack And How Does It Works Beyond data retrieval, sql injection can alter database content, impacting data integrity. attackers might delete or modify records, disrupt services, or execute commands leading to information loss or corruption. This cheat sheet contains vital sql injection payloads, commands, and tips that will help penetration testers and ethical hackers to find and use weaknesses in applications. When testing for sql injection vulnerabilities, these are some of the most common commands and special characters. the better you understand sql, the more successful you will be with the. Confidentiality: since sql databases generally hold sensitive data, loss of confidentiality is a frequent problem with sql injection vulnerabilities. authentication: if poor sql commands are used to check user names and passwords, it may be possible to connect to a system as another user with no previous knowledge of the password. Sql injection (sqli) remains one of the most critical and pervasive web application vulnerabilities, allowing attackers to manipulate backend databases and access sensitive information. Sql injection occurs when attackers insert malicious sql code into application queries through user input fields. this can let them read sensitive data, modify or delete records, and sometimes execute system commands on the database server.

What Is An Sql Injection Cheatsheet And Examples When testing for sql injection vulnerabilities, these are some of the most common commands and special characters. the better you understand sql, the more successful you will be with the. Confidentiality: since sql databases generally hold sensitive data, loss of confidentiality is a frequent problem with sql injection vulnerabilities. authentication: if poor sql commands are used to check user names and passwords, it may be possible to connect to a system as another user with no previous knowledge of the password. Sql injection (sqli) remains one of the most critical and pervasive web application vulnerabilities, allowing attackers to manipulate backend databases and access sensitive information. Sql injection occurs when attackers insert malicious sql code into application queries through user input fields. this can let them read sensitive data, modify or delete records, and sometimes execute system commands on the database server.

Sql Injection And Cross Site Scripting The Differences And Attack Sql injection (sqli) remains one of the most critical and pervasive web application vulnerabilities, allowing attackers to manipulate backend databases and access sensitive information. Sql injection occurs when attackers insert malicious sql code into application queries through user input fields. this can let them read sensitive data, modify or delete records, and sometimes execute system commands on the database server.
Comments are closed.