What Is The Side Channel Attack The Security Buddy

Performing Side Channel Attack Keeloq25c3 2 Pdf Information And In side channel attack, an attacker uses this side channel information to determine the secret keys and break the cryptosystem. In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information.
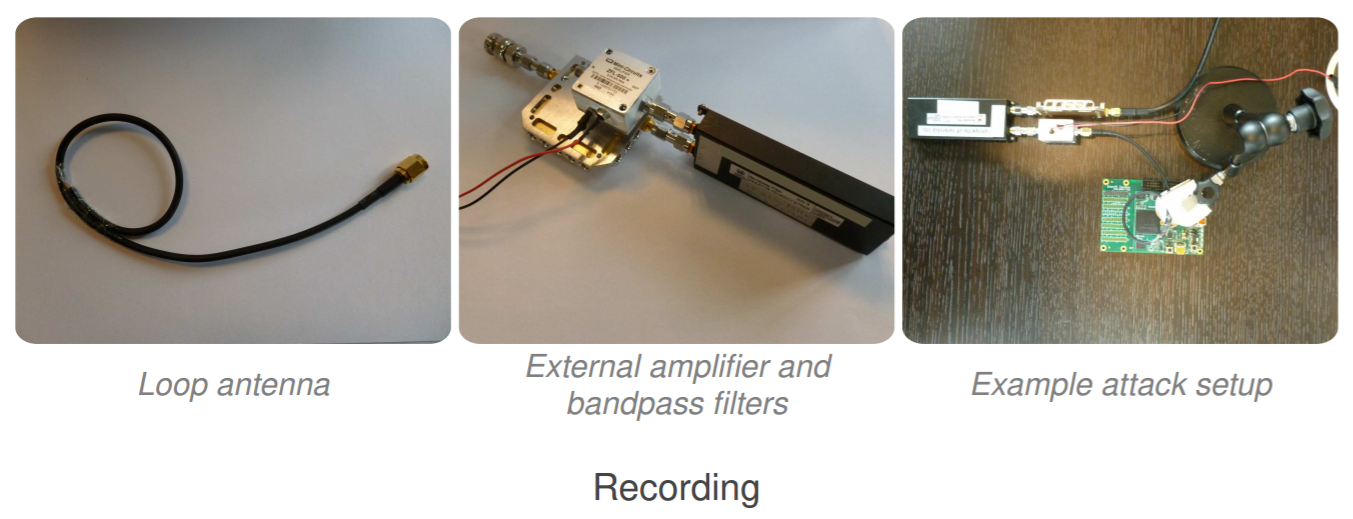
Side Channel Attack Archives Security Affairs Side channel attacks don't target cryptographic systems, but their implementations instead. find out how they can compromise secure algorithms. you can have the best cryptographic systems in the world in place, but your setup may still be vulnerable to side channel attacks. A side channel attack is a cybersecurity exploit that aims to gather information from or influence a system's program execution. it does this by measuring or exploiting indirect effects of the system or its hardware rather than directly targeting the program or its code. Learn what a side channel attack is, how it works, and why it threatens even the most secure hardware by exploiting physical information leaks. A side channel attack is a security exploit that targets the implementation of a computer system rather than theoretical vulnerabilities in the algorithms. these attacks analyze information gained from the physical operation of a system.

What Is The Side Channel Attack The Security Buddy Learn what a side channel attack is, how it works, and why it threatens even the most secure hardware by exploiting physical information leaks. A side channel attack is a security exploit that targets the implementation of a computer system rather than theoretical vulnerabilities in the algorithms. these attacks analyze information gained from the physical operation of a system. A side channel attack is a type of cyberattack that involves exploiting various side channels to gain unauthorized access to sensitive information. in computing and cryptography, side channels refer to unintended channels of communication that leak information about the system’s internal state. A side channel attack is a type of cyberattack that extracts sensitive information from a system by analyzing indirect physical data—such as power consumption, electromagnetic emissions,. Discover what side channel attacks are, how they operate, their examples, potential risks, and effective protection strategies in this comprehensive guide. Side channel attacks present a sophisticated and often overlooked threat in the field of cybersecurity. unlike conventional cyberattacks that exploit software vulnerabilities or network misconfigurations, side channel attacks exploit indirect data leaks from the physical operation of a system.

Side Channel Attack Stories Hackernoon A side channel attack is a type of cyberattack that involves exploiting various side channels to gain unauthorized access to sensitive information. in computing and cryptography, side channels refer to unintended channels of communication that leak information about the system’s internal state. A side channel attack is a type of cyberattack that extracts sensitive information from a system by analyzing indirect physical data—such as power consumption, electromagnetic emissions,. Discover what side channel attacks are, how they operate, their examples, potential risks, and effective protection strategies in this comprehensive guide. Side channel attacks present a sophisticated and often overlooked threat in the field of cybersecurity. unlike conventional cyberattacks that exploit software vulnerabilities or network misconfigurations, side channel attacks exploit indirect data leaks from the physical operation of a system.

Side Channel Attack By Wentz Wu Issap Issep Issmp Cissp Ccsp Csslp Discover what side channel attacks are, how they operate, their examples, potential risks, and effective protection strategies in this comprehensive guide. Side channel attacks present a sophisticated and often overlooked threat in the field of cybersecurity. unlike conventional cyberattacks that exploit software vulnerabilities or network misconfigurations, side channel attacks exploit indirect data leaks from the physical operation of a system.
Comments are closed.