Github Fredchang823913319 Hardware Security Side Channel Attack

Side Channel Attack Targets Windows Linux Infosecurity Magazine About implementing side channel attack based on prime reload and flush reload. Implementing side channel attack based on prime reload and flush reload releases · fredchang823913319 hardware security side channel attack.

Side Channel Attack Targets Windows Linux Infosecurity Magazine Github is where people build software. more than 100 million people use github to discover, fork, and contribute to over 420 million projects. Implementing side channel attack based on prime reload and flush reload activity · fredchang823913319 hardware security side channel attack. Implementing side channel attack based on prime reload and flush reload hardware security side channel attack readme.md at master · fredchang823913319 hardware security side channel attack. While primarily aimed at mitigating side channel attacks, these hardware level defenses simultaneously enhance memory security, achieving a resilient architecture with minimal performance trade offs.
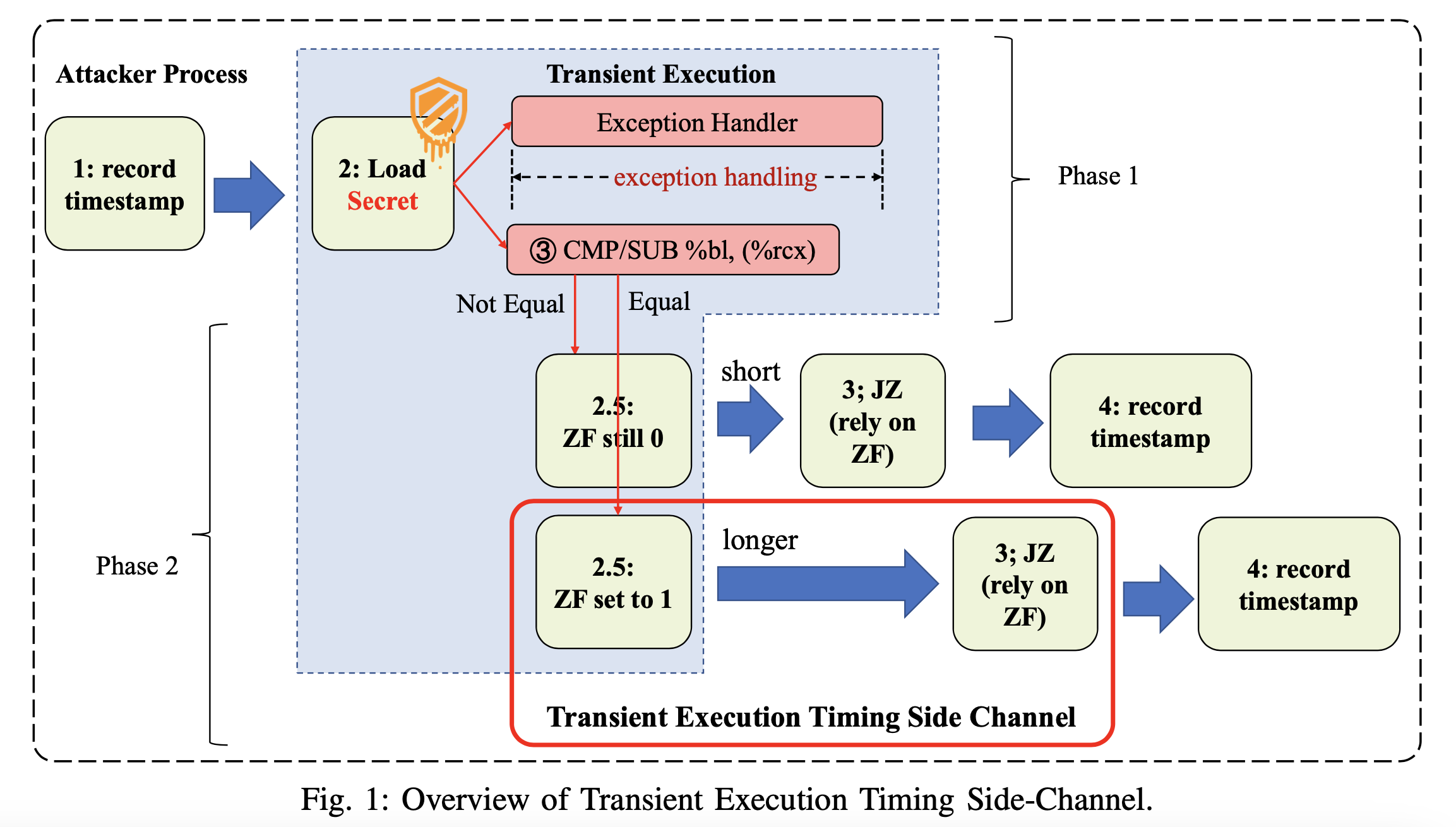
Researchers Discover New Side Channel Attack That Works Against Intel Implementing side channel attack based on prime reload and flush reload hardware security side channel attack readme.md at master · fredchang823913319 hardware security side channel attack. While primarily aimed at mitigating side channel attacks, these hardware level defenses simultaneously enhance memory security, achieving a resilient architecture with minimal performance trade offs. Learn how to perform a deep learning side channels attack using tensorflow to recover aes cryptographic keys from a hardware device power traces, step by step. We present a kernel level infrastructure that allows systemwide detection of malicious applications attempting to exploit cache based side channel attacks to break the process confinement enforced by standard operating systems. Abstract: attacks based on side channel analysis (sca) pose a severe security threat to modern computing platforms, further exacerbated on iot devices by their pervasiveness and handling of private and critical data. Design and fabrication outsourcing has made integrated circuits vulnerable to malicious modifications by third parties known as hardware trojan (ht). over the last decade, the use of side channel measurements for detecting the malicious manipulation of the chip has been extensively studied.
Researchers Discover New Side Channel Attack That Works Against Intel Learn how to perform a deep learning side channels attack using tensorflow to recover aes cryptographic keys from a hardware device power traces, step by step. We present a kernel level infrastructure that allows systemwide detection of malicious applications attempting to exploit cache based side channel attacks to break the process confinement enforced by standard operating systems. Abstract: attacks based on side channel analysis (sca) pose a severe security threat to modern computing platforms, further exacerbated on iot devices by their pervasiveness and handling of private and critical data. Design and fabrication outsourcing has made integrated circuits vulnerable to malicious modifications by third parties known as hardware trojan (ht). over the last decade, the use of side channel measurements for detecting the malicious manipulation of the chip has been extensively studied.
Comments are closed.